Snyk Code support for PHP vulnerability scanning enters beta
DeveloperSteve Coochin
September 2, 2021
0 mins readSnyk Code support for PHP vulnerability scanning is now available in beta. Now security issues in PHP code can be identified quickly and easily.
To get started, log into Snyk or sign up for a free account. Once logged in on the dashboard, click on the Add Project button in the top right corner and connect to a repository you want to scan.

From there you can connect to a number of different repository platforms and run a PHP vulnerability scan on all of the repos you manage, even if they're private. There is also an option to scan from the CLI or an IDE. Explore other ways to integrate Snyk Code into your development setup.
Let's look at the top three possible vulnerabilities the new PHP scans may identify and dig into what to look for as part of the beta release.
XSS
Cross-site scripting (XSS) vulnerabilities are where an attacker will inject malicious codeinto trusted applications. This can either be targeted at a user's browser or injected into the application runtime or operating system.
In PHP, this can occur for a number of reasons and is more commonly associated with improper sanitization of user input. I covered this in more detail in my previous post on avoiding code injection.
Let's take a look at a working example to better understand what to look for using this pull request for a repository.

In the example, you can see the side-by-side comparison which has filter_var with the filter type FILTER_SANITIZE_NUMBER_INT being added to handle the $_POST input sanitisation, this filter will remove all characters except digits and the plus or minus signs.
Insecure hash
Hashing via code is a way of securely encrypting a string of characters into a value or key that represents the original string, sometimes for storage in a database or for storage within the runtime for use later. Often it's a two-way hashing so that the encrypted data can be stored and decrypted later.
Traditionally, MD5 was the standard method — particularly in PHP — for encrypting things like user passwords until the method was proven to be “cryptographically broken and unsuitable for further use” in 2008.
Looking at this example of a fix that was put in place for this repository, we can see that it involves setting null as a default value as part of the signed key function call. This means that if no value is passed into the function, it will default to null and can be handled appropriately within the signed key function.

SQL injection
SQL injection is similar to XSS, only the vulnerability surfaces the ability to inject a malicious SQL payload into a database. In application security, this can lead to a new user being added with elevated privileges, data being compromised, or the deletion of data from the database.
It's really important to keep in mind here, particularly when dealing with user input that needs to touch a database, that proper sanitation is key.
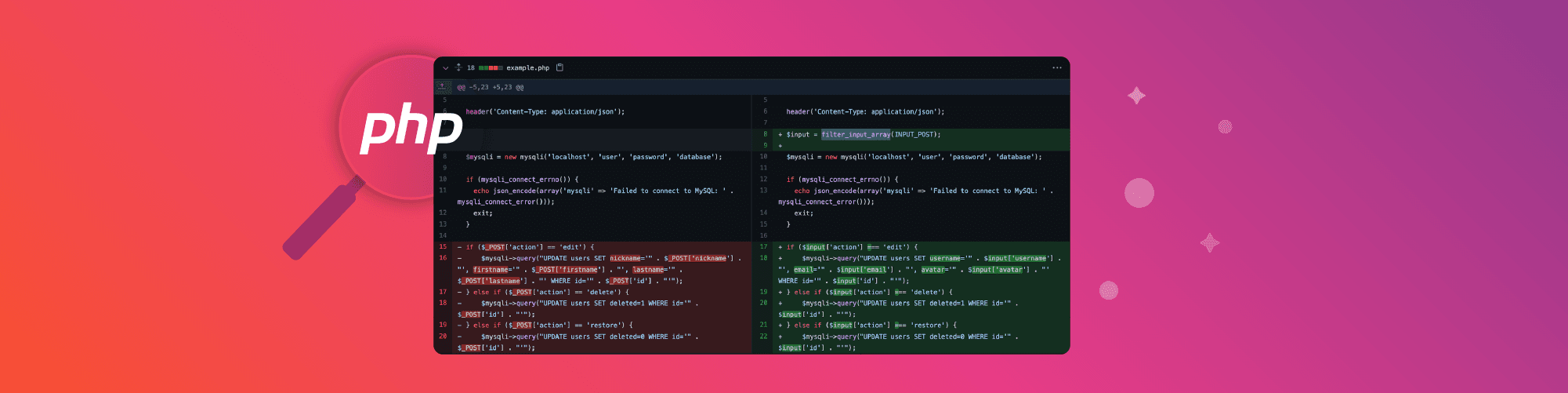
Looking at another example repository, you can see that the pull request implemented uses PHP's filter_input_array to handle the input going into this database function.

Scan your PHP using Snyk Code
Those were just a few common examples from Snyk Code's deep knowledge base of vulnerabilities. I encourage you to take it for a spin to see what is identified in your code.
It's important to note again that PHP in Snyk Code is in beta. We would love your feedback to help make our PHP support even better. So reach out with any questions or if you want to talk about your findings.
Here are some other great reads about PHP security:
Get started in capture the flag
Learn how to solve capture the flag challenges by watching our virtual 101 workshop on demand.