Announcing the Snyk and Docker Security Guide for Developers
November 18, 2020
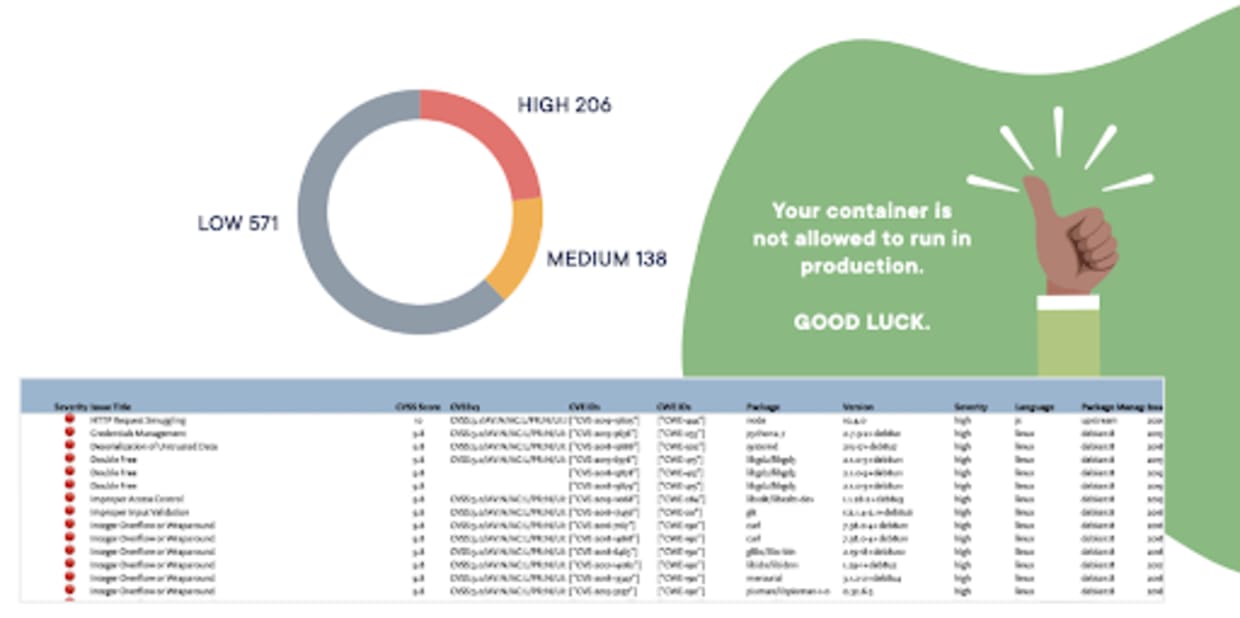
0 mins readNow that you might be seeing your first scan results for container vulnerabilities, you have likely discovered a few issues… maybe even more than a few! It can be daunting to get a list of 10s or 100s of vulnerabilities when you scan an image. Fear not! to lay the foundations for handling these issues. And we are pleased to announce the release of the Guide to Container Security for Development Teams.
Snyk Container will help you figure out what is in your container images, how a developer—who may not be an expert in container and operating system security pitfalls—can fix these issues, and where you should focus your efforts amidst the many vulnerabilities you might find.
A practical guide, built for developers
There are many best practices lists for building secure containers, but they usually have a single bullet that says something like “Scan for container vulnerabilities”. The concept is good, but the problem is, what do you do once you know about all those vulnerabilities? In fact, this issue of what to do next isn’t unique to just container vulnerabilities, which is one reason our company is named Snyk: “So Now You Know...”!
So now you know you have container vulnerabilities...what do you do about it?
While we believe our products solve some of the technical hurdles, there is an educational aspect for the people and process side that isn’t so easy to just build into a product, and that’s where this guide comes in. We present you with a starting point for a process for handling container vulnerabilities, no matter which tools you use to build or scan container images.
We provide a general overview of the umbrella topic of container security and then dive deeper into the specific area of container image security. Then we outline a process for addressing vulnerabilities in containers, and also some examples of DevSecOps workflows that other organizations have implemented successfully to collaboratively build secure images. We also get into how you can keep your own code secure in a container, why you should use Docker Official images, and how to choose the best base images, from a security perspective.
Hint: our products will help you quite a bit here!
And fear not! It’s not all just a process manual. There are plenty of examples and code as well.
Let us know what you think
We hope this Guide to Container Security for Development Teams is useful to you as you start to build your container image scanning practices. This guide is meant to show best practices, which we can’t do without continued input from our users!
So, if you have a great practice that you think we should cover, please reach out on the Snyk Community site and let us know.
Developer-first container security
Snyk finds and automatically fixes vulnerabilities in container images and Kubernetes workloads.
