Shifting Docker security left
William Henry
April 17, 2019
0 mins readWelcome to the Docker security report: Shifting Docker security left.
This report is split into several posts:
Shifting Docker security left
The top two most popular Docker base images each have over 500 vulnerabilities
Or download our lovely handcrafted pdf report which contains all of this information and more in one place:
Download Shifting Docker Security Left
Docker vulnerabilities are widespread
The top 10 official Docker images with more than 10 million downloads each contain at least 30 vulnerabilities.
Of the top 10 most popular free certified Docker images, 50% have known vulnerabilities.
There is a lack of clear ownership for Docker security
68% believe developers should be responsible for owning container security, followed by operations (39%).
80% of developers say they don’t test their Docker images during development.
50% of developers don’t scan their Docker images for vulnerabilities at all.
Easy fixes can have big security impact
20% of the Docker images with vulnerabilities could have been solved by a simple image rebuild.
44% of Docker images had known vulnerabilities for which there were newer and more secure base images available.
45% of developers never discover new vulnerabilities disclosed in their production containers.
How you can improve:
Choose the right Docker base image
Work with the smallest base image: don't package what you don't need!
Proactive remediation advice: tools such as Snyk offer recommended image upgrades and alternatives with the fewest vulnerabilities from which you can choose.
Use multi-stage builds and build often!
By using multi-stage builds, you only copy the artifacts you actually need, reducing unnecessary vulnerabilities in your images.
Re-build your Docker images as part of your development pipeline.
Scan your Docker images frequently
Scan your Docker images as part of your development workflow and in your CI/CD pipelines.
Proactive remediation advice: tools such as Snyk pinpoint which image layers introduce vulnerabilities and offer remediation advice.
Monitor your Docker containers in production by automatically scanning your base image and packages.
An introduction to this report
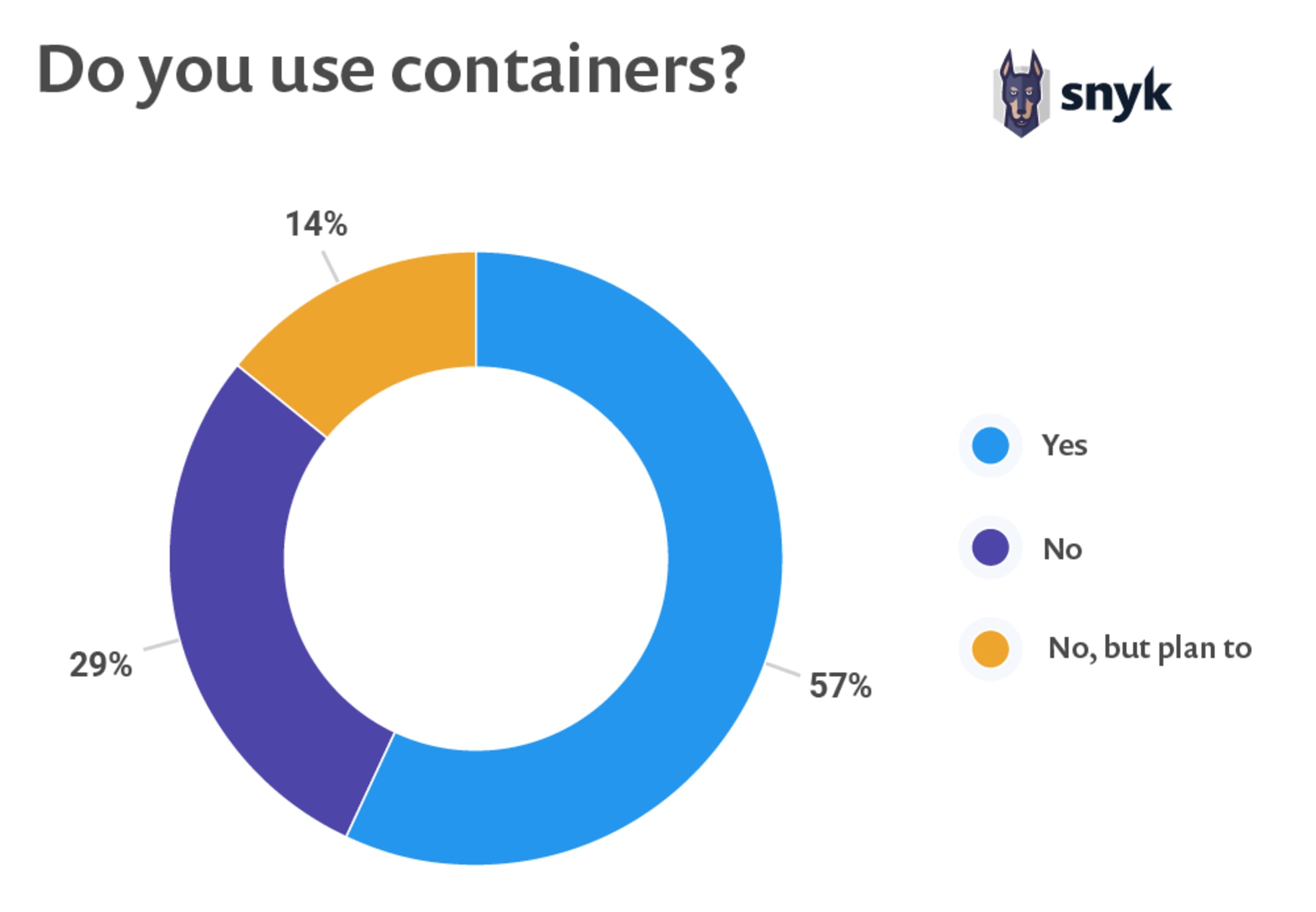
Docker turned 6 years old this year. Over the course of these 6 years, the adoption of Docker—and containers in general—has grown massively. Currently 57% of developers claim to use containers in their day-to-day work (see our graph later in this section). With the advent of container technologies, developers have been able to build innovative solutions more easily. Lots of these open source solutions are freely available. Today, even major software vendors post pre-built images in public registries such as Docker Hub, enabling developers to download and use these images.
In 2015 Docker, Red Hat, CoreOS, IBM, Google and a broad coalition of industry leaders focused on common standards for software containers, founding the Open Container Initiative (OCI). This initiative was founded with the goal to host an open source, technical community. In addition, it aims to build a vendor-neutral, open-specification and portable runtime for container-based solutions.
Since the time OCI standards were released, many other build and runtime technologies have been developed. So, while this article often mentions “Docker containers” and “Docker images” it should be understood that there are many technologies available that adhere to the OCI (open container initiative) standards. At the time of writing this piece, Docker is still, by far, the most popular OCI build tool and runtime. The dominance of Kubernetes and its use of CRI-O is beginning to change that landscape.
As more organizations create, spread and use Docker containers, the risk of security vulnerabilities grows. Docker images are largely built on top of other images, meaning a vulnerability in one image is also present in all the images that utilize it. The wide adoption of Docker comes at a price — a single vulnerability can be widely spread and have major impact.
We took a closer look at the raw data from our State of Open Source Security report, to gain a better understanding of the Docker landscape and its associated security risks and best practices. In this report we look at common security problems with Docker containers and Docker images and some of the actions you can take to improve security.
The Docker landscape
Today, Docker is widely used and Docker Hub is the default place to go if you need a Docker image. Docker Hub is the world's largest library and community for container images. At the time of writing this blog, Docker Hub already had over 2 million (2,085,422) images available to download and use instantly, and that number grows daily.
Anyone can push images to Docker Hub but Docker Hub labels certain images as more trustworthy than others. While Docker offers official recognition and even certification for some contributors and their images, even those images still contain vulnerabilities that should be managed.
Currently, Docker Hub contains:
223 images published by verified publishers. These products are published and maintained directly by a commercial entity.
151 official images available for use. Official images are a curated set of Docker open source and "drop-in" solution repositories.
40 Docker images certified by Docker, meaning that they must conform to best practices and pass certain baseline tests.
Each of the top 10 official Docker images with more than 10 million downloads and each of them with at least 30 vulnerabilities.
Of the top 10 most popular free Docker certified images, half with known vulnerabilities. One image we checked had almost 160 known vulnerabilities.
The adoption of application container technology is increasing at a remarkable rate and is expected to grow by a further 40% in 2020, according to 451 Research.