How to publish Node.js Docker images to Docker Hub registry using GitHub Actions
August 9, 2021
0 mins readIn a previous post, we presented a step-by-step tutorial on how to publish Node.js Docker images to GitHub Packages registry using GitHub Actions. In this post, we’ll focus on publishing the Docker image that we build to the public Docker Hub registry.
Why is this useful you might ask? The Docker command line application docker has a default registry setting for docker.io which points to the Docker Hub registry. This provides a nice developer experience of pulling images by the <user>/<repository> convention, such as the following, if you wanted to use the Snyk CLI as a Docker image:
In this article, we’ll go through a step-by-step walkthrough of configuring another Docker image build and publish workflow, which can work side-by-side with the previous workflow we presented for GitHub Packages registry.
Just like the previous post, this one follows up on Dockly, the open source Node.js command line tool for managing docker containers from the CLI, and shows how to push a Docker image to Docker Hub. You can view the final workflow in Dockly’s GitHub repository.
Create a GitHub Actions workflow
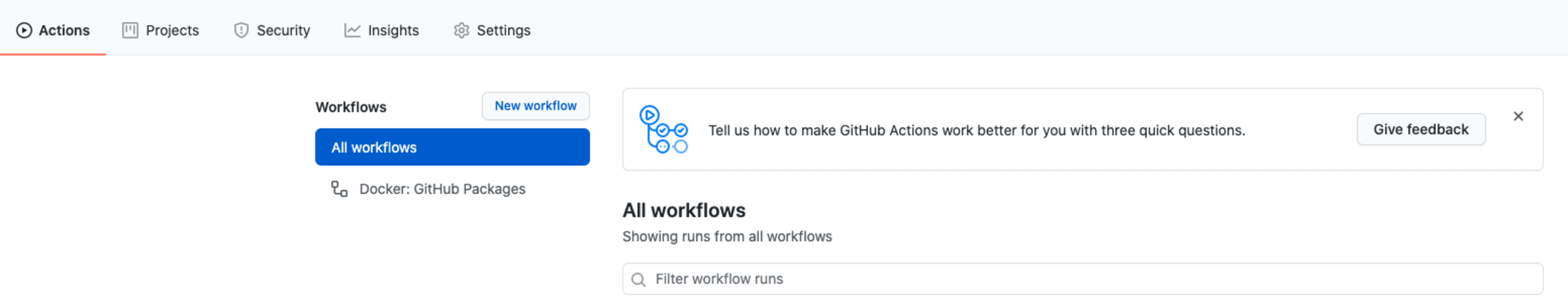
To add a new workflow, you can simply create a new file in the .github/workflows/ directory, or browse to your open source repository on GitHub, click the Actions tab, and then click on New Workflow and begin a new workflow:
Choose the filename for the Docker Hub publish workflow file, such as docker-publish-to-dockerhub.yml.
If you’re doing this from the GitHub UI, it may pre-populate the workflow file, in which case just remove it and add the following:
We have outlined each of these in detail in the previous article, but to recap:
This Docker Hub workflow will run on every push, tags release, and pull request made to the main branch of the repository.
The global environment variables define the
REGISTRYtodocker.iowhich means our images will be pushed and available from Docker Hub, and theIMAGE_NAMEset to the GitHub username and repository name. If you have a different Docker Hub username, then you might need to tweak this one.
Next, we’ll define our jobs, in which we will establish a process of building the Docker image, and then publishing it.
Login to Docker Hub and build and publish the Docker image
Next, we will need to perform the following actions:
Login to Docker Hub, for which we will need to create a token in Docker Hub and set it up as a repository secret in the GitHub repository settings.
Extract metadata of the Docker image that we build, so it is available to the build process of the image.
Push the Docker image that was built to Docker Hub.
The above is established with the following code snippet, which needs to be added to the workflow contents that we created in the previous step:
Once you applied the workflow file and merged it to the main branch, you should hopefully end up with a successful build that results in a new Docker image pushed to the Docker Hub registry:

A known caveat is that, at this point in time, the Docker Hub repository that you publish the image to doesn’t automatically populate with a proper description and README contents, because this is not available in the official docker/build-and-push GitHub Action.
If you’d like to seek this capability out, the maintainers recommend the marketplace’s GitHub Action Docker Hub Description and point to an example reference in their docs which you can adopt.
Pulling Docker images from Docker Hub registry
To fetch the new Docker image from Docker Hub, all you need to do is run the familiar docker pull command, such as:
Are you pushing vulnerable Docker images?
Why stop here? You can find, monitor, and even fix vulnerabilities in Docker images with Snyk. You can adopt whichever workflow that suits best, whether you prefer the CLI, or import Docker images directly from Docker Hub so you can monitor them for security vulnerabilities.
My colleague Eric Smalling wrote a detailed best practices guide on Developer Driven Workflows – Dockerfile & image scanning, prioritization, and remediation if you want to deepen your knowledge on this.Lastly, there’s a Snyk GitHub Action you can use in the GitHub Actions ecosystem to scan for security vulnerabilities in open source libraries, and container images.
Go deeper
If you’d like to further explore best practices for building Docker images, I suggest the following:
10 best practices to containerize Node.js web applications with Docker
Docker for Node.js developers: 5 things you need to know not to fail your security
And if you didn’t read the previous article and would like to publish Docker images to GitHub Packages, then read up on how to publish Node.js Docker images to GitHub Packages registry using GitHub Actions.
Developer-first container security
Snyk finds and automatically fixes vulnerabilities in container images and Kubernetes workloads.
