High severity vulnerability found in libcurl and curl (CVE-2023-38545)
Hadas Bloom
October 4, 2023
0 mins readUpdate: October 11, 2023
Today, at 06:00 UTC, the maintainers of cURL released the 8.4.0 versions of curl and libcurl to mitigate a High severity, heap-based buffer overflow (proof-of-concept and the initial notification) that could impact systems with a specific configuration and preconditions.
This zero-day vulnerability is present in packages from several managed and unmanaged open source ecosystems, including (but not limited to) C/C++, cargo, cocoapods, npm, NuGet, pip, and pub, as well as various Linux distributions such as Alpine, Debian, RHEL, and others.
This is the first high-severity vulnerability found in curl in several years (the last one was in early 2021).
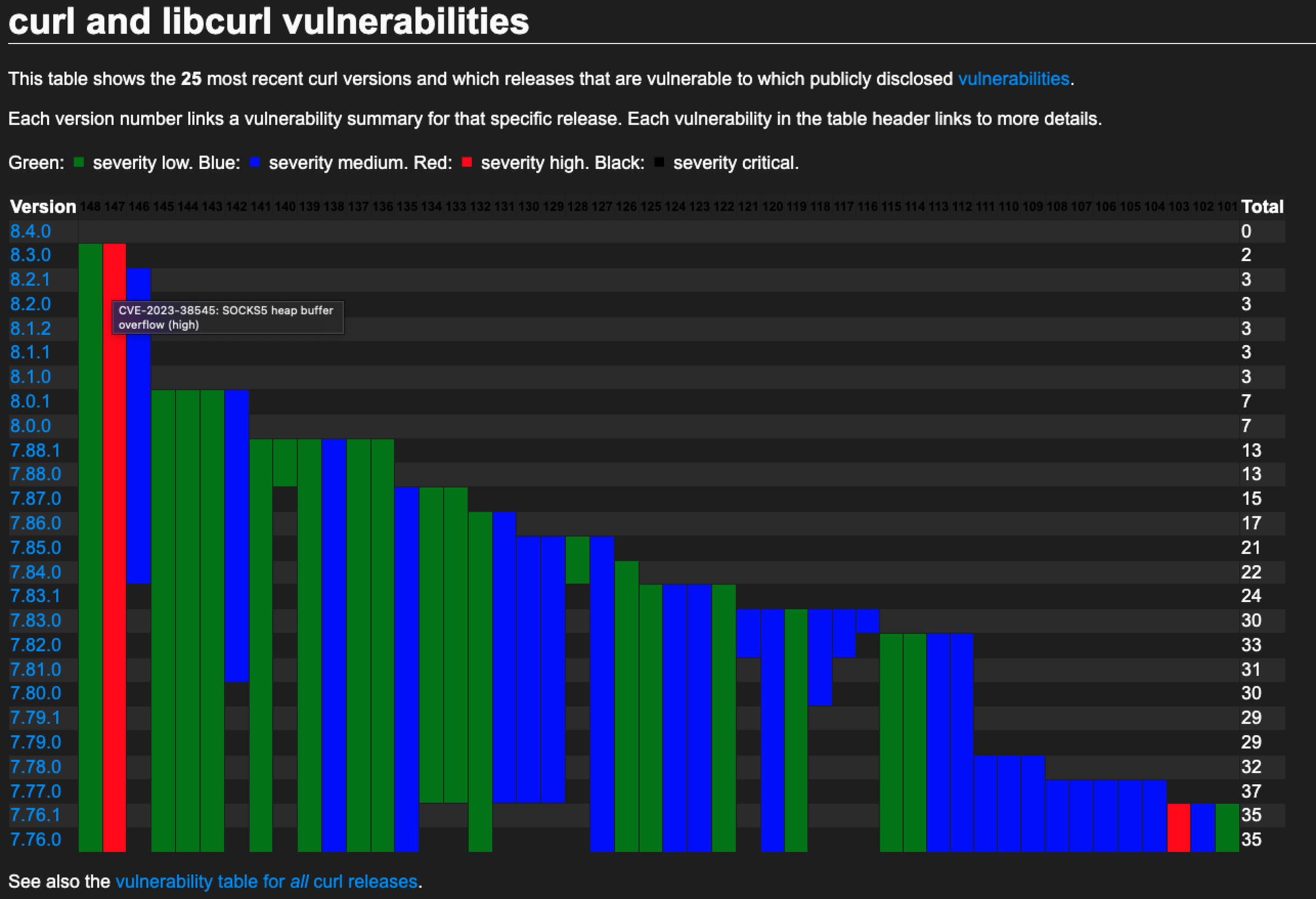
The impacted curl/libcurl versions (since March 2020) are as follows:
The exploit complexity is considered high and can only be triggered in certain scenarios. As explained in the maintainer's post, How I made a heap overflow in curl, the vulnerability requires the vulnerable library to either be contacting an uncontrolled/compromised server (to be exploited via a HTTP redirect), or using an attacker-controlled URL via SOCKS5 proxy with hostname resolution enabled to trigger the vulnerable condition — and even then it's a limited charset heap overflow. Heap overflows in modern systems are extremely difficult to turn into an arbitrary code execution (ACE); hence the high-complexity exploit.
Now that the vulnerability is published and tracked, you can use Snyk's reporting feature to find impacted projects by selecting your org and then choosing Reports in the sidebar. Select +Add Filter under issue details, select CVE, then enter the CVE number: CVE-2023-38545

This blog will be updated with any new information as it comes up.
Update: October 4, 2023
On October 3, 2023, Daniel Stenberg, the long-time curl maintainer and original author, published a note on both LinkedIn and X (formerly Twitter) regarding the shipping of curl version 8.4.0, which will contain a fix for "probably the worst security problem found in curl in a long time." This issue should be taken seriously as curl maintainers have been vocal about downplaying the risk associated with most vulnerabilities reported against curl in the past (a recent example is the article CVE-2020-19909 is everything that is wrong with CVEs), and in this unique case, they are coming out to specifically advertise the risk — adding, "buckle up."
The fixed version, 8.4.0, will be released on October 11, 2023, at around 06:00 UTC, per the maintainers.
Earlier today (October 4, 2023), the CVEs that will be used to contain vulnerability information were announced in a GitHub discussion.
CVE-2023-38545 will be assigned to the High severity issue, affecting both libcurl and curl. An additional Low severity issue assigned to CVE-2023-38546 (that only affects libcurl) will also be fixed.
What we currently know?
cURL is a popular project, providing both the libcurl library (used for URL transfers) and the curl command-line tool (used for getting and sending data using URLs). cURL was initially released 27 years ago and has been used ubiquitously since 1996.
Many, if not all, of the Linux distributions that Snyk supports use libcurl, hence, the potential scope of impact is wide.
How to prepare for remediation
Check your container and package usage ahead of time to gauge your exposure
Identify hosts that have curl installed and determine how it was installed
Check the curl version you are using with
curl --version
Gauge your exposure
Ahead of the release of the fixed version of libcurl, you can use Snyk to quickly find the open source projects and container images that might be impacted.
Navigate to the Dependencies in the Snyk App UI sidebar. Once you're in the Dependencies view, expand the Dependencies filter, and type in "curl". You can select individual versions or tick the Select all shortcut, then click outside of the filter to see the results. This will show you all of the projects that you have that have the libcurl versions you selected. You can further browse the projects and dependencies to gauge your exposure and to prioritize what you should fix first.
Identify hosts that have curl installed
Many operating systems ship with curl installed by default, and where it is installed will depend on the operating system and installation method. You can quickly determine if curl is installed and in your path by running: curl --version
If it returns without an error, it will show the version of curl that was first found in your path. Note that it may be installed in more than one location. For example, on recent Apple computers, it's shipped by default in /usr/bin/curl, but may have also been installed via homebrew. You can determine where the version in your path is by running which curl. Some other locations to look on macOS/Linux-based operating systems would be:
/bin/curl/usr/bin/curl/usr/local/bin/curl/opt/homebrew/opt/curl
Make sure that you find all the occurrences that need to be updated in preparation for the new version.
How to respond once the update is released
On release day — planned for October 11, 2023 around 06:00 UTC — be prepared to update to version 8.4.0. Once the new version is available, Snyk will have more information and publish additional information about the vulnerability to this blog (and link any follow-up blogs here as well).
Update vulnerable packages and containers
Use the information that you gathered in preparation to update your projects and container images to pick up the fixed version of libcurl. Different ecosystems and Linux distributions may wait to upgrade their usage of the affected packages only after this time, and the availability of fixes will likely be staggered. For example, some maintainers may wait for upstream fixes prior to releasing updates to their container images or packages, while others might patch in place. In either case, Snyk can help you find and fix the issues.
Update curl on your devices
Once a fixed version of the curl binary is available, update the versions that you have installed. We'll be posting some helpful tips on getting it updated in a separate post: there are multiple ways curl can get installed, and the updated methods can vary by operating system.
What is Snyk doing?
Snyk has published a placeholder advisory for the High severity upstream issue. The contents on the placeholder will be updated as more is learned.
Snyk security experts are actively following release updates, vulnerability information, social media chatter, and more to give our customers any incoming data. Additionally, research is being conducted to find any additional downstream packages that may be affected. We will update this blog as necessary.