How Snyk helps satisfy White House cybersecurity recommendations
Jason Lane
March 23, 2022
0 mins readOur modern digital world has proven that global tensions between countries are not contained to the battlefield. As international cyberattacks and protestware proliferate, the Biden-Harris administration (White House) instructed US institutions, large and small, to be more vigilant about malicious cyber activity. In retaliation to massive economic sanctions the US and other world leaders instituted on Russia in March 2022 for the unprovoked invasion of Ukraine, new intelligence suggests Russia may be considering options for potential cyberattacks.
In their statement, the White House provided a fact sheet that included a long list of security best practices that all public and private organizations should “execute with urgency” to enhance cybersecurity and protect data and critical infrastructure.
Use multi-factor authentication on all systems
Implement the latest threat detection technologies
Ensure systems are secure and change passwords frequently
Schedule recurring offline data backup processes
Create and test disaster recovery plans
Encrypt all critical data to prevent it from being used if stolen
Educate employees on common cyberattack tactics such as phishing emails
Establish relationships with the FBI and visit the CISA website
Breaking down the best practices
The fact sheet also made the below software security recommendations. Since Snyk’s mission is to help companies secure their software, we thought it would be helpful to show how our product capabilities align with each recommendation.
1. Build security into your products from the ground up — “bake it in, don’t bolt it on” — to protect both your intellectual property and your customers’ privacy.
When building software, it’s important to monitor every phase of the software development lifecycle (SDLC). Software vulnerabilities can be introduced and discovered at any point during the process. Snyk provides integrations into the most popular IDE, CI/CD, and Git tools, a robust CLI, and the ability to monitor live containers in any environment. This enables developers and DevOps engineers to seamlessly build secure applications from the start.
2. Develop software only on a system that is highly secure and accessible only to those actually working on a particular project. This will make it much harder for an intruder to jump from system to system and compromise a product or steal your intellectual property.
In addition to your organization's endpoint security systems and password policies, Snyk’s Business and Enterprise products support single sign on (SSO) to ensure only the people you assign will have access to your projects.
3. Use modern tools to check for known and potential vulnerabilities. Developers can fix most software vulnerabilities — if they know about them. There are automated tools that can review code and find most coding errors before software ships, and before a malicious actor takes advantage of them.
Snyk is a modern application security platform that makes it easy for developers and security professionals to automatically find, fix, and monitor for vulnerabilities in their software.
Unlike traditional static application security testing (SAST) products in the market, which were primarily designed for security teams to test applications post-development, Snyk Code uses a revolutionary approach designed to be developer-first, extremely accurate, and fast enough to enable real-time workflows. It gives teams the ability to uncover common software vulnerabilities in custom first-party code like the OWASP Top Ten.
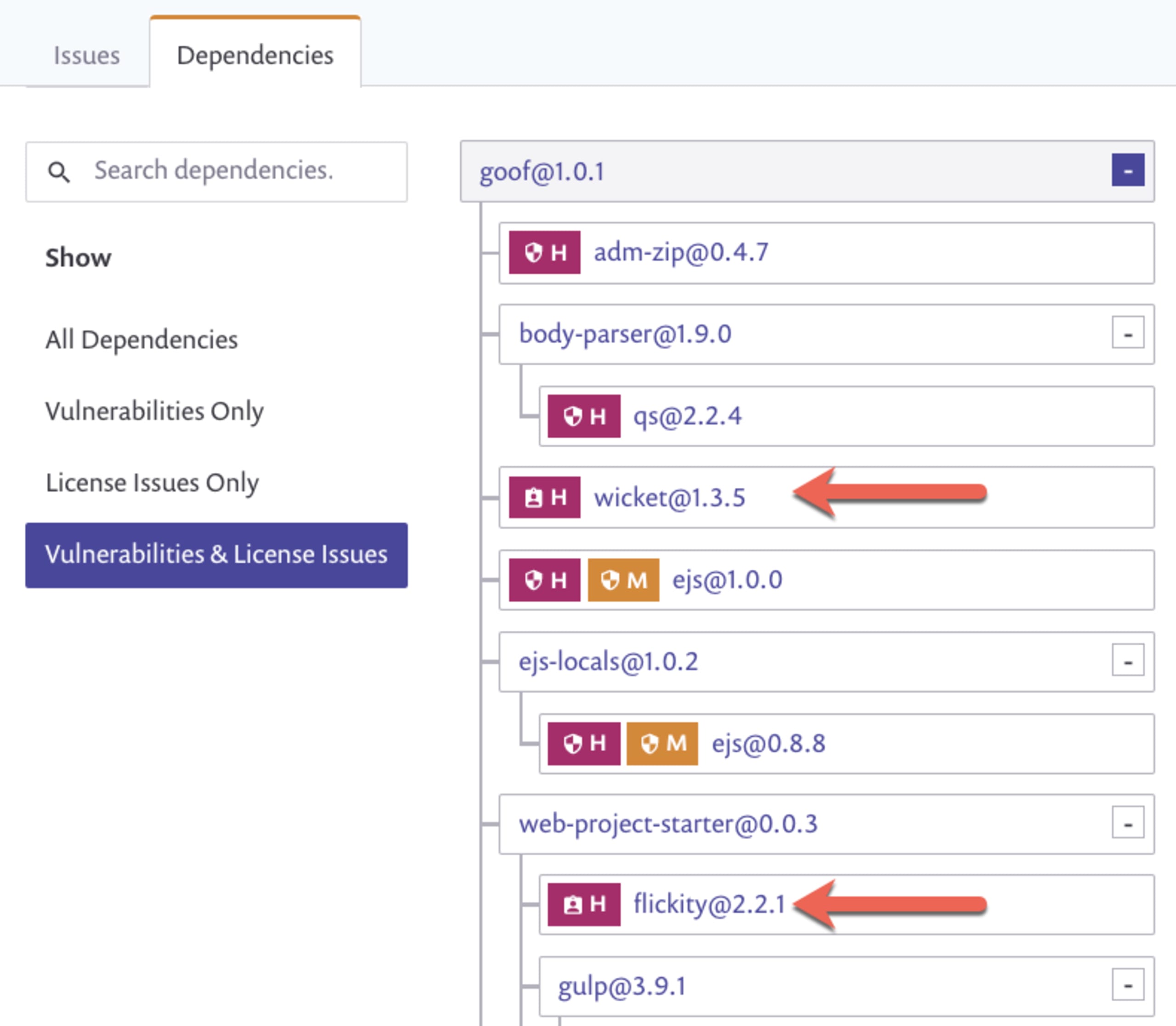
Snyk Open Source and Snyk Container are both software composition analysis (SCA) products that scan for open source dependencies and flag any packages that are vulnerable. Snyk scans for direct and transitive dependencies and shows them listed as a dependency tree with all the packages and their corresponding versions. Any vulnerabilities discovered will be prioritized using a best-in-class database that includes an array of different factors, including social trends, CVE scores, exploit maturity, and more. This data helps provide a priority score so developers can focus on fixing the most important vulnerabilities first.
Snyk Infrastructure as Code (Snyk IaC) helps developers write secure HashiCorp Terraform, AWS CloudFormation, Kubernetes, and Azure Resource Manager (ARM) configurations before touching production. Snyk’s developer-first approach meets developers where they work and provides fixes that can be directly merged into code.
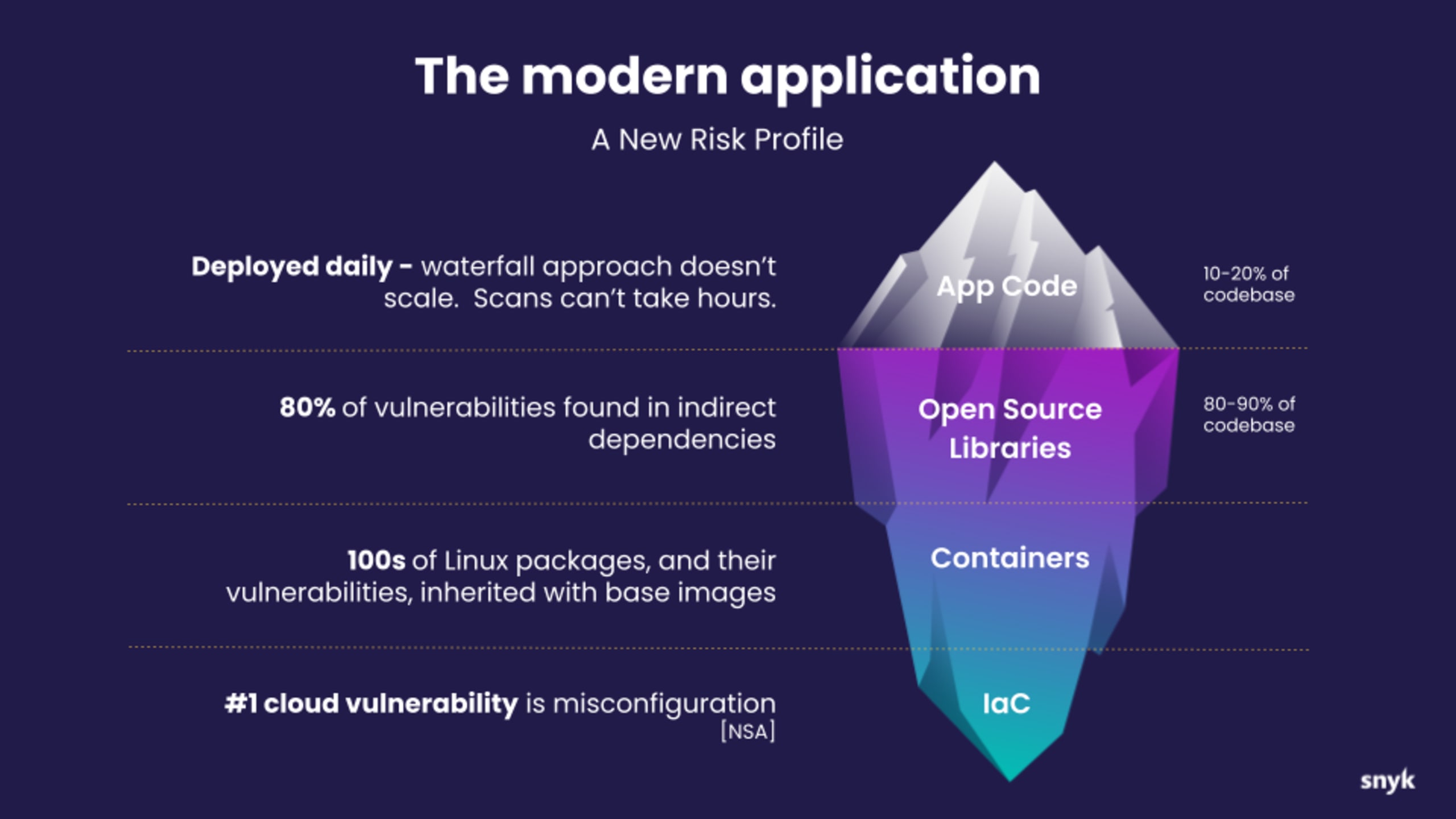
4. Software developers are responsible for all code used in their products, including open source code. Most software is built using many different components and libraries, much of which is open source. Make sure developers know the provenance (i.e., origin) of components they are using and have a “software bill of materials” in case one of those components is later found to have a vulnerability so you can rapidly correct it.
When it comes to finding the right open source packages, Snyk Advisor guides developers by giving them an easy way to proactively search for secure packages. The database currently has over 1 million open source packages and continues to grow. Here are some of the key criteria used to evaluate packages.
Popularity - Understand the prevalence of an open source package using metrics such as downloads and source code repository stars to measure popularity.
Maintenance - Get insights about an open source dependency health and assess the sustainability of the project.
Community - Is the community thriving for an open source package you use in your project or has it gone stale? Gauge the status with project metrics.
Security (only vulnerabilities and licenses today) - Quickly assess the security posture of an open source project and its past versions. Further, connecting your project with Snyk will offer fix advice and automation that enable security at scale and speed.
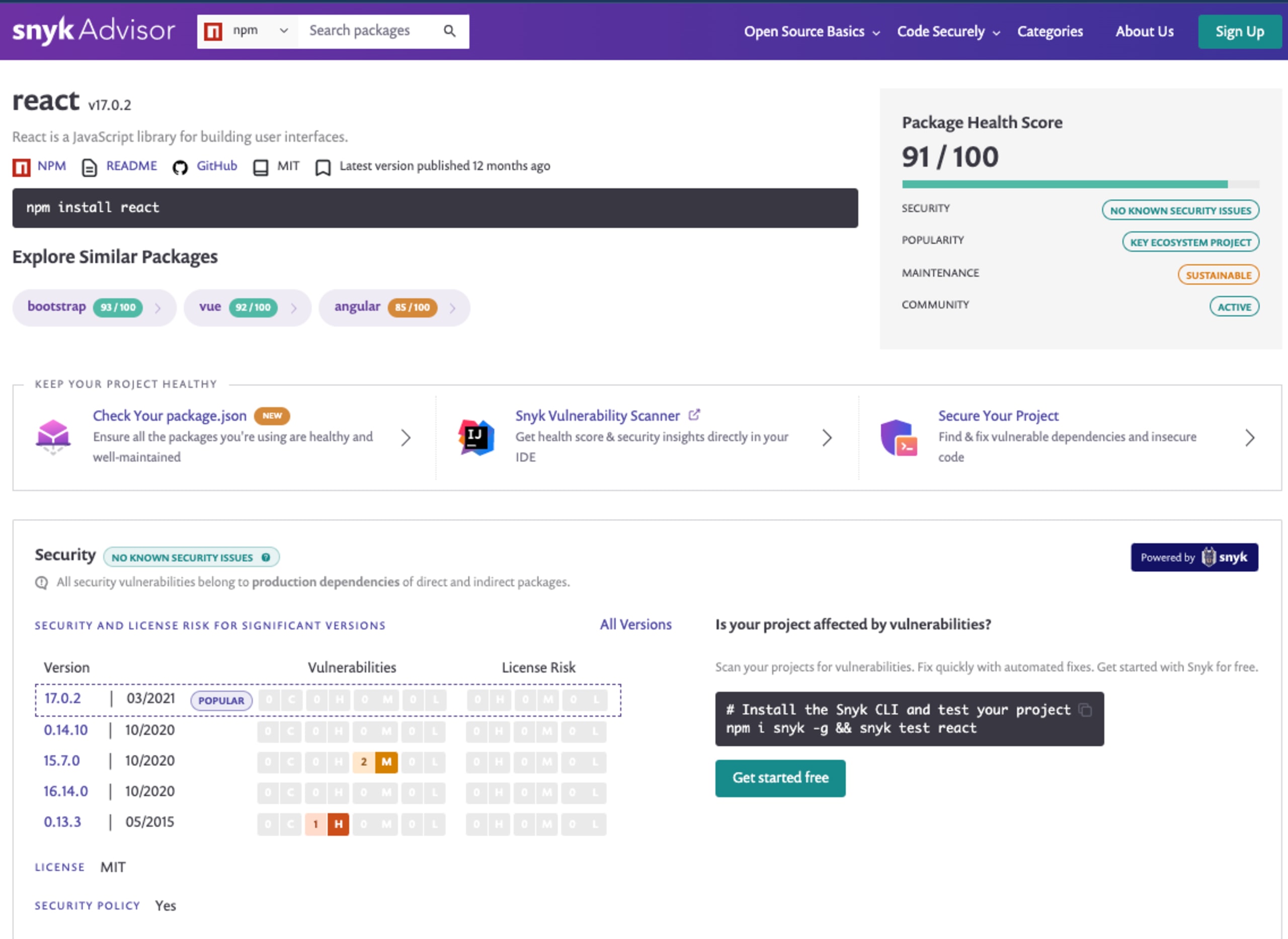
The Snyk dependency graph provides the entire list of direct and transitive open source dependencies included in an application. This list can be viewed in the user dashboard, CLI, or even exported into a standard SPDX file format when a customer or partner needs to see the list of ingredients in your software. Snyk also has an experimental project called snyk2spdx that customers can use.
5. Implement the security practices mandated in the President’s Executive Order, Improving our Nation’s Cybersecurity. Pursuant to that EO, all software the U.S. government purchases is now required to meet security standards in how it is built and deployed. We encourage you to follow those practices more broadly.
After the EO was released in 2021, we addressed each area in detail including SBoMs, Secure development environments and processes, open source integrity, developer empowerment, SDLC automation, code security, attestation, and component-level reporting.
Stay vigilant against cyberattacks
Now more than ever, it’s important that organizations around the world secure their services and infrastructure from cyberattacks. Global security is going to take a global effort, with contributions coming from large enterprises down to solo open source contributors. So use the best tools, follow the best guidance, and stay vigilant and secure.
Snyk stands by the President's order and we’re here to help everyone do their part to secure their organizations’ software and protect the world from one of the most defining threats of our time. Sign up for free.
