Infrastructure as Code in a DevSecOps World
This article will discuss infrastructure as code (IaC), what it is exactly, and the security implications of using IaC in the real world.
What Is Infrastructure as Code?
Infrastructure as code (IaC) is the process of provisioning and managing resources in public clouds such as AWS, GCP, and Azure via a set of editable text files that describe how and where infrastructure resource configurations are deployed.
These input scripts are ingested by Infrastructure as Code tools which then automatically create, update, or delete resources to ensure that the cloud infrastructure complies with the state defined in the IaC file. IaC tools are designed to manage the implicit and explicit dependencies between cloud infrastructure resources so that the creation, maintenance, and removal of resources is performed logically and takes into account these resource dependencies.
Before Infrastructure as Code (IaC) existed, resources were typically provisioned manually or, at best, through simple scripts like shell scripts or Python. Configuration management tools were very efficient when it came to configuring an instance once it was up and running, but had a gap in the ability to create the instance in the first place.
IaC emerged to help bridge this gap by automating resource provisioning and thus move away from snowflake servers. The introduction of high-level declarative languages to define a desired state, along with the IaC tools that automatically implemented those declarations, was a big leap forward within the industry.
Infrastructure as code (IaC) brought many benefits, among them:
Speed and standardization: Allowing your desired state to be written in scripts for perfect reproducibility.
Version control: Enabling these scripts to be saved in Git, thus allowing you to maintain a history of your infrastructure, as with application code.
Documentation: Allowing the scripts to serve as documentation and a single source of truth.
Efficiency: Extending the possibility of continuous deployments to the provisioning and management of the resources themselves.
The three major public cloud providers all offer their own custom IaC solutions, which work only for their own respective platforms:
Amazon Web Services offers AWS CloudFormation.
Microsoft Azure’s platform is the Azure Resource Manager.
Google Cloud Platform uses Google Cloud Deployment Manager.
Terraform is the most widely used cloud-independent IaC software and offers the advantage of supporting many cloud vendors. In fact, smaller cloud providers, such as DigitalOcean and Rackspace, tend to rely on Terraform instead of an in-house IaC product.
The automated configuration management software vendors, including Puppet, Chef, and Ansible, have also been working to expand their capabilities and today, offer some level of support for creating, updating, and deleting resources in public clouds. However, they were not designed as IaC from the ground up.
What Is IaC Security?
Infrastructure as Code (IaC) security is the practice of securing cloud, infrastructure and app configurations by scanning IaC files and the cloud deployment for compliance against a codified ruleset.
IaC security can prevent misconfigurations from reaching live cloud environments and thus reduce the risk of data breaches, downtime, and deployment failures. The consequences of IaC scripts that do not uphold security principles can be severe, including unsecured storage buckets that expose sensitive data or an instance that is inadvertently publicly accessible and acts as an attack vector for hackers.
Some IaC security best practices include the principle of least privilege, network segmentation so that the resources and their related dependencies are all secured within a private subnet, and the encryption of data in-transit and at-rest.
The principle of least privilege is important for mitigating damages from poorly configured resources or maliciously modified scripts and applies to Infrastructure as Code (IaC) at three levels:
Defining who is and is not authorized to run the scripts.
Limiting the permissions of authorized**IaC**usersto what is necessary to perform their tasks.
The IaC scripts should ensure that the permissions granted to the various resources it creates are limited to what is required for them to perform their work.
Most of the remaining IaC security aspects relate to the resources created by the scripts themselves. For example, a properly segmented network architecture can contain damage from internal or external attacks. Including an encrypt = true line in your Infrastructure as Code (IaC) scripts protects data at rest, while invoking managed services such as AWS Certificate Manager can protect data in transit. Other best practices to follow include setting up the usual protection mechanisms against DDoS and common HTTP attacks, such as a web application firewall.
What Is IaC in DevSecOps?
In the context of infrastructure as code, DevOps entails close cooperation between developers and DevOps engineers as well as employing IaC as part of continuous deployment. “DevSecOps,” also coined the “shift-left approach,” is the integration of security aspects into DevOps. When it comes to IaC, DevSecOps means to integrate security right from the start of the project and keeping a tight grip on security at all times. It also means using the appropriate tools for your workload as well as automating security (sometimes called security as code).

DevSecOps Adoption: Integrating Security into the CI/CD Pipeline
DevSecOps is as much about the organizational culture (in particular, the free flow of information between diverse teams) as it is about technology. DevSecOps, as part of the DevOps worldand where culture and technology converge, pushes for automation at all levels. IaC is a fundamental aspect of DevOps, as it seeks to automate entire deployments. The DevSecOps aspect of IaC is about automating security best practices and using the tools adapted to the specific workload in order to improve security.
Infrastructure-as-Code Security Tools
In reality, there are few security tools out there specifically designed to apply security best practices at the DevSecOps Infrastructure as Code level. Third-party security tools such as DataDog, Splunk, Jaeger, and others can be used outside the IaC scripts. And there are cloud-native security services that can be enabled from IaC scripts (such as Amazon GuardDuty, Amazon Macie, and Amazon Inspector).
Snyk IaC Security, however, is one of the few tools that has been designed with developers _and_security teams in mind to secure Terraform, Kubernetes, CloudFormation, Azure Resource Manager (ARM) and more.
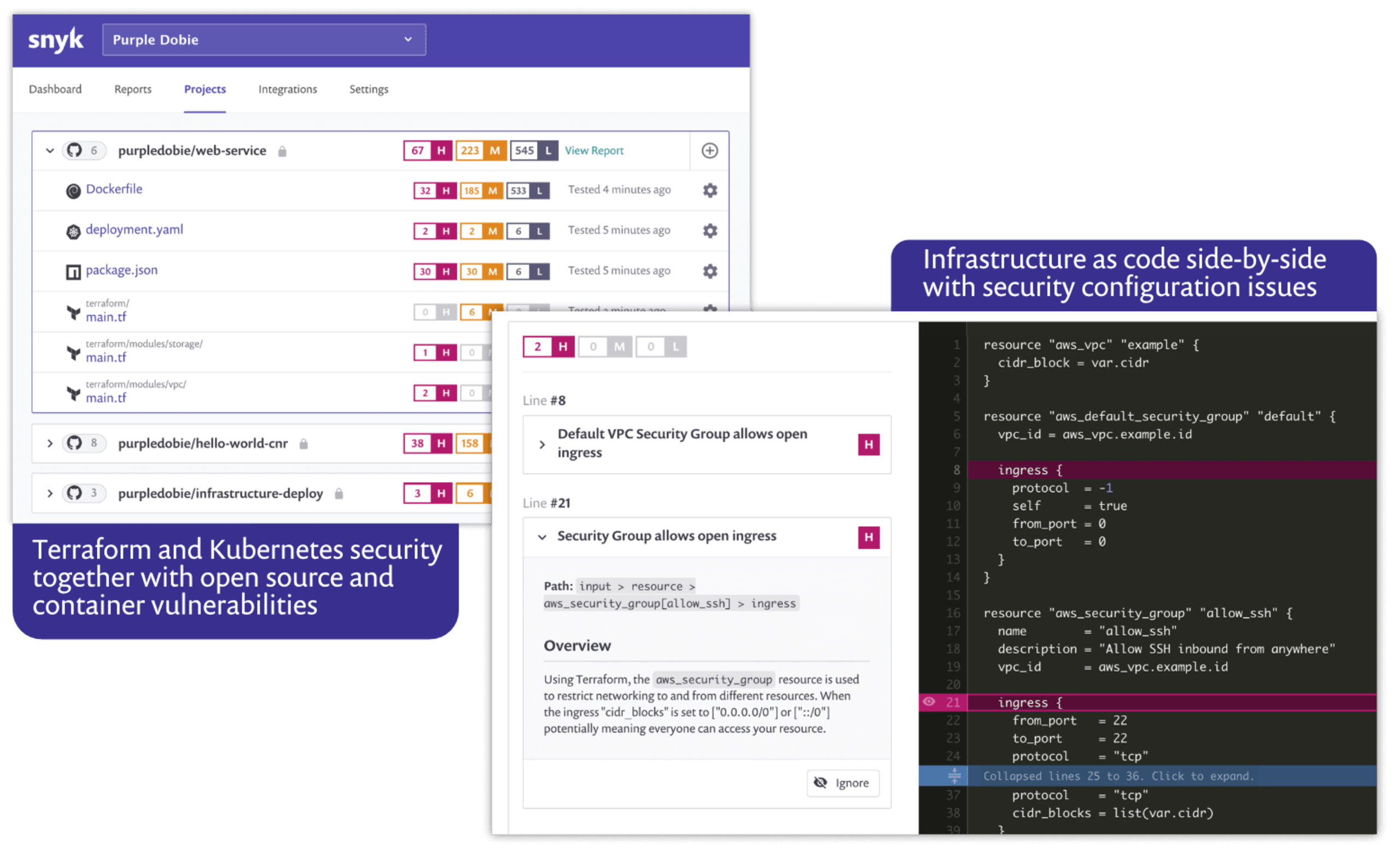
Snyk IaC secures your configurations throughout the entire infrastructure lifecycle by integrating seamlessly into developer workflows and enforcing best practice IaC security policies from code to cloud:
Stand up security best practices and compliance: evolving, built-in ruleset based on industry best practices, CIS benchmarking , and threat-modeling exercises by Snyk security. Embed security and ace your code review.
Keep developers in their preferred workflow: continuous testing of IaC for misconfigurations with both options for testing locally via the CLI and integrations into IDEs, Source Code Management (GitHub, GitLab, etc), and Terraform Cloud. Maximize developer adoption and minimize downtime or distractions.
Fix the riskiest issues faster: issue severity, impact and structured fix guidance, highlighted in-line with code so developers can quickly fix issues and ensure secure configurations are always upheld.
Secure for your specific scenario: write or import custom rules in Open Policy Agent’s high level language Rego, adjust severity settings of predefined rules.
Secure throughout the entire infrastructure lifecycle: detect issues of infrastructure drift and unmanaged resources in live cloud environments. Report issues direct to engineers with context on the resource to drive quicker fixes and bring unmanaged resources under control.
Snyk Infrastructure as Code is an integral part of the Snyk platform that embeds and upholds security best practices across the entire cloud native application stack, including open source, containers, and Kubernetes—in addition to infrastructure as code.
Secure infrastructure from the source
Snyk automates IaC security and compliance in workflows and detects drifted and missing resources.
Conclusion
With infrastructure as code sitting at the top of the orchestration layers, security is made more manageable and easier to maintain. While there are many solutions out there that can be enabled by IaC, only a mere few allow you to apply security best practices at the IaC level. Finding the right tools as well as staff training and education that fosters cooperation among teams is another crucial element. Apply security best practices to IaC code when using Terraform, Kubernetes, CloudFormation, Azure Resource Manager (ARM), and more. Register for free to secure your projects with Snyk.