5 tips to supercharge app security from code to cloud
August 8, 2023
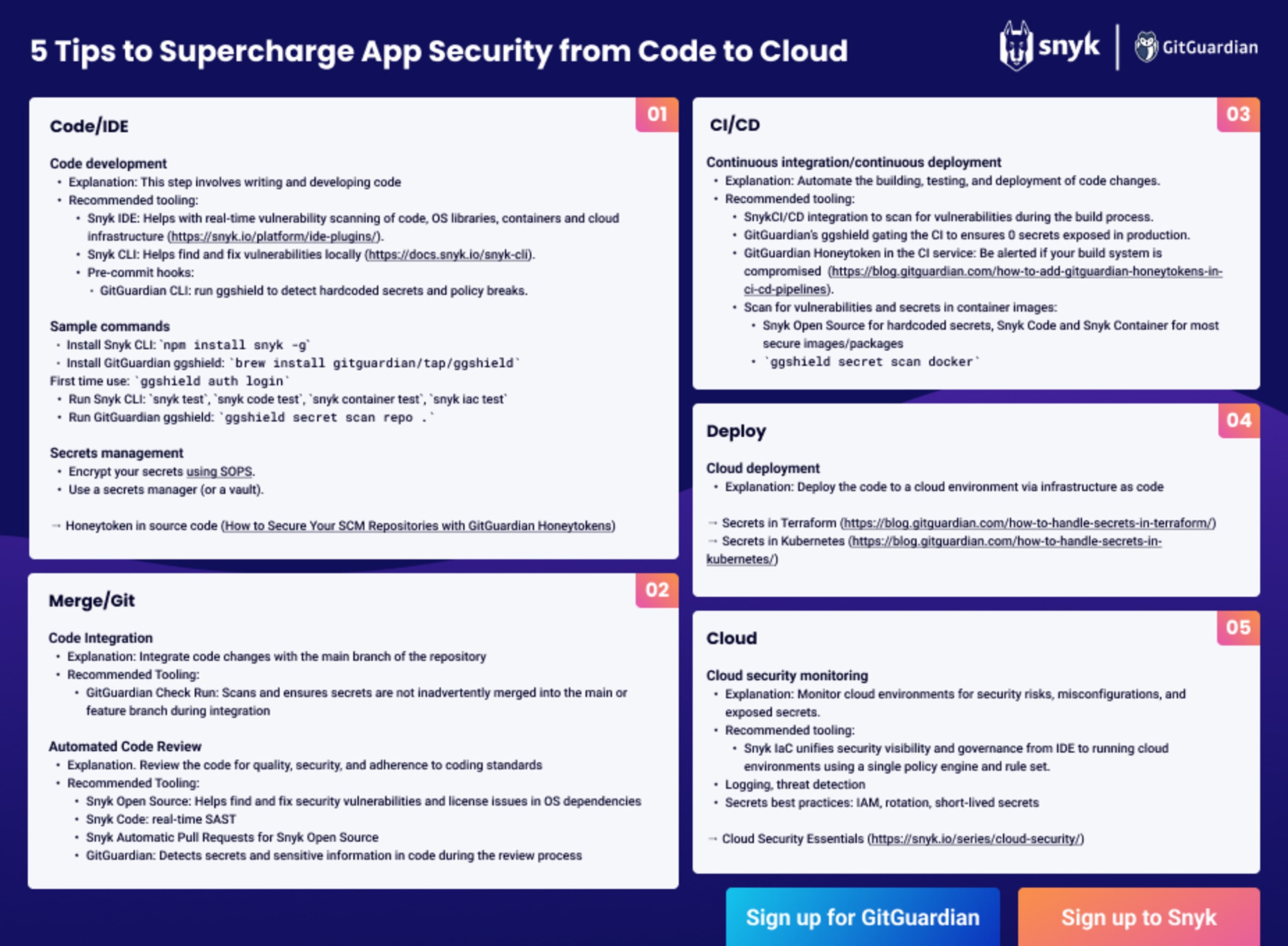
0 mins readAs the partnership between Snyk and GitGuardian continues to grow, we’ve collaborated on a new cheat sheet that identifies key security considerations and tools that can help you mitigate risks and protect your code.
The journey from code to cloud and back to code necessitates a holistic approach to security. Organizations can build secure and resilient applications, protect sensitive data, and establish a strong AppSec culture by integrating security throughout the software development lifecycle. With the aid of tools like Snyk and GitGuardian, DevSecOps practices can be strengthened, allowing for more efficient and secure software development processes.
Our new cheat sheet will help you use GitGuardian to manage your secrets while continuously monitoring your code and dependencies for vulnerabilities using Snyk.
Integrating security in the software development lifecycle empowers developers to take ownership of security, enables proactive risk mitigation, and establishes a culture of security within the organization.
It is of paramount importance due to several key reasons:
Proactive risk mitigation: Integrating security practices from the early stages of the software development lifecycle helps minimize the risk of security breaches, data leaks, and other security incidents.
Cost and time savings: Fixing security issues in later stages of development or during production can be significantly more time-consuming and costly.
Compliance and regulatory requirements: Many industries have strict compliance and regulatory requirements for security, such as the GDPR, HIPAA, PCI DSS, and ISO 27001. Integrating security throughout the software development lifecycle ensures that the necessary security controls and measures are implemented to meet these requirements.
Enhanced trust and customer confidence: Security breaches can have severe repercussions on an organization's reputation and erode customer trust. Organizations demonstrate a commitment to safeguarding sensitive data and protecting their customers' information by prioritizing security throughout the software development lifecycle.
Shift-left approach: Integrating security practices early in the software development lifecycle follows the shift-left principle. This means addressing security concerns as early as possible — ideally starting from the requirements and design phases — and empowering developers to take ownership of security and collaborate with security teams to build more secure applications from the outset.
Improved software quality: Integrating security practices in the software development lifecycle leads to improved software quality. Organizations enhance the overall reliability, stability, and performance of their applications.
Rapid response to emerging threats: Integrating security practices throughout the software development lifecycle enables organizations to respond quickly to emerging security threats. Developers can promptly implement security patches, updates, and countermeasures.
Code security
Code security is a critical aspect of application development as vulnerabilities in code can lead to security breaches, data leaks, and other malicious activities. Some common challenges in code security include:
Vulnerable dependencies
Applications often rely on open source libraries and frameworks to expedite development and leverage existing functionalities. However, these dependencies may have their own vulnerabilities. If these vulnerabilities are not identified and addressed, they can become entry points for attackers. The challenge lies in keeping track of the dependencies, staying updated with security patches, and ensuring that the versions used are free from known vulnerabilities.
Insecure coding practices
Insecure coding practices can introduce vulnerabilities into the code base. Developers may unintentionally use insecure functions or techniques that can be exploited by attackers. Examples include using outdated encryption algorithms, not properly validating user input, or neglecting to implement proper access controls. Insecure coding practices often arise from a lack of security awareness or inadequate training.
Lack of code review
Insufficient or inconsistent code review processes can result in undetected security issues. Without thorough code reviews, vulnerabilities may go unnoticed, leaving the code base susceptible to attacks. Code reviews should encompass functional and security aspects, ensuring that security best practices are followed, potential vulnerabilities are identified, and secure coding standards are maintained. Regular and comprehensive code reviews are essential to minimize the risk of security breaches.
Addressing these core security challenges requires a multi-faceted approach that includes secure coding practices, continuous education and training for developers, robust dependency management processes, secure coding guidelines, regular code reviews, and automated tools to identify vulnerabilities and potential weaknesses.
Using Snyk and GitGuardian for code security
Developers and organizations can enhance code security within the software development lifecycle by leveraging the capabilities of Snyk and GitGuardian. These tools offer a comprehensive set of features and integrations that help identify vulnerabilities, secure dependencies, analyze code, and detect exposed secrets — improving the overall security posture of applications.
Snyk command-line interface (CLI)
The Snyk CLI is a versatile tool allowing developers to integrate Snyk into their development workflow seamlessly. It provides a flexible and customizable approach to running security scans and automating vulnerability detection. By incorporating the Snyk CLI into build scripts or CI/CD pipelines, developers can automatically scan their code and dependencies for vulnerabilities. The Snyk CLI supports multiple programming languages, package managers, and integration options, making it a valuable tool for integrating security checks into the development process.
You can install the Snyk CLI globally by running npm install snyk -g. This allows you to run various commands such as snyk test, snyk code test, snyk container test, and snyk iac test to scan your code, dependencies, containers, and infrastructure as code for vulnerabilities and misconfigurations.
Learn more about the Snyk CLI here.
Snyk integrated development environments (IDEs).
Snyk offers plugins and integrations for popular IDEs such as Visual Studio Code, IntelliJ IDEA, and Eclipse. These integrations bring Snyk's vulnerability detection capabilities directly into the developer's coding environment, providing real-time feedback on security issues as code is being written. With IDE integrations, developers receive immediate alerts and suggestions for remediation, empowering them to address vulnerabilities on-the-fly and follow secure coding practices during development.
Learn how to install the plugin on your favorite IDE here.
Snyk Open Source
Snyk Open Source is a powerful tool that scans open source dependencies for vulnerabilities. It analyzes the dependencies used in a project and identifies any known vulnerabilities present in those libraries or frameworks. Snyk Open Source helps developers stay informed about the security risks associated with their dependencies and guides remediation steps.
Snyk Code
Snyk Code is a tool that analyzes code repositories for security flaws. By leveraging static application security testing (SAST) techniques and cutting-edge, hybrid AI, Snyk Code examines the codebase for potential security vulnerabilities, insecure coding practices, and common security pitfalls. It provides developers with actionable insights and recommendations to remediate the identified issues. Snyk Code integrates with popular version control systems, allowing developers to analyze code for security flaws within their existing workflows seamlessly.
GitGuardian
GitGuardian complements Snyk's offerings by focusing on detecting secrets and sensitive information in code repositories. It scans repositories for exposed API keys, passwords, tokens, and other credentials that, if leaked, could lead to security breaches. GitGuardian operates at the commit level, monitoring code changes and identifying hard-coded credentials in real time. GitGuardian helps developers and organizations proactively address security vulnerabilities and prevent unauthorized access or misuse of sensitive information.
Learn more about GitGuardian here.
Cloud security
Cloud environments introduce unique security challenges due to their distributed nature, shared responsibility model, and the complexity of managing various cloud services. Some common cloud security challenges include:
Data breaches
Cloud environments store vast amounts of sensitive data, making them attractive targets for cyber attackers. Data breaches can occur due to vulnerabilities in cloud services, weak access controls, or insider threats. Breached data can lead to financial loss, reputational damage, and legal repercussions.
Misconfigurations
Improperly configured cloud resources can expose sensitive data or provide unauthorized access to attackers. Misconfigurations can happen at various levels, such as storage buckets, network configurations, virtual machines, or access control policies. Inadequate security configurations can result from human error, lack of knowledge, or insufficient automation.
Insider threats
Insiders with privileged access to cloud resources, such as employees or contractors, can pose a significant security risk. Insider threats can be intentional, where individuals misuse their access for personal gain or malicious activities, or unintentional, where they inadvertently expose sensitive data or fall victim to social engineering attacks.
Insecure APIs
Cloud services rely on APIs for communication and interaction. Insecure APIs can be exploited by attackers to gain unauthorized access, manipulate data, or launch other types of attacks. Vulnerabilities in APIs can include insufficient authentication mechanisms, weak authorization controls, and inadequate input validation.
Compliance and regulatory requirements
Cloud environments often host sensitive data subject to various compliance and regulatory requirements, such as the GDPR, HIPAA, or PCI DSS. Ensuring compliance with these regulations and maintaining data privacy and security within the cloud infrastructure is essential. Failure to meet compliance standards can result in penalties, legal issues, and loss of customer trust.
Identity and access management
Managing user identities, roles, and access controls in the cloud can be challenging. Proper authentication and authorization mechanisms must be implemented to prevent unauthorized resource access. Ensuring strong password policies, implementing multi-factor authentication, and regularly reviewing access privileges are critical for maintaining robust identity and access management practices.
Addressing these cloud security challenges requires a combination of technical measures, such as implementing security controls and encryption, as well as organizational practices, such as security training, incident response plans, and regular audits. Additionally, leveraging developer security tools like Snyk can enhance the security posture of the cloud infrastructure.
Snyk Container
Snyk Container helps secure containerized applications by scanning container images for vulnerabilities. Containers, such as those created with Docker, have become popular for deploying applications in the cloud due to their portability and scalability. However, container images can contain vulnerable components or outdated dependencies — which can be exploited by attackers.
Snyk Container integrates seamlessly into the container build process, allowing developers and operations teams to identify and remediate vulnerabilities early on. Snyk Container detects vulnerable packages, libraries, and frameworks. It provides actionable insights, such as specific vulnerability details, severity levels, and recommended remediation steps.
Snyk IaC
Snyk Infrastructure as Code (IaC) helps secure the cloud environments that manage and provision cloud infrastructure using code templates. Tools like Terraform, AWS CloudFormation, and Azure Resource Manager allow developers to define infrastructure resources programmatically. However, misconfigurations or security vulnerabilities in these infrastructure definitions can severely affect cloud environment security.
Snyk IaC offers the capability to analyze IaC templates and identify security issues and misconfigurations. It scans the code and provides insights into potential vulnerabilities, insecure settings, or compliance violations. Organizations can remediate them before the infrastructure is provisioned by detecting these issues early in the development or deployment cycle. Snyk IaC also helps enforce security best practices and ensure compliance with industry standards and regulatory requirements, reducing the risk of misconfigured or insecure cloud infrastructure.
These tools provide automated scanning and analysis capabilities, allowing for early detection and remediation of vulnerabilities and misconfigurations. Integrating Snyk into the cloud deployment pipeline enables a proactive approach to security, ensuring that containerized applications and infrastructure templates are secure and compliant.
Going back to code: A continuous feedback loop for developers
A continuous feedback loop is an essential component of a successful DevSecOps practice. It provides developers with real-time insights and feedback on security issues, enabling them to effectively address vulnerabilities and improve code security. Here are the key elements of a continuous feedback loop for developers:
Automated security testing
Integrating automated security testing into the development workflow allows for continuous scanning and analysis of code and dependencies. Tools like Snyk and GitGuardian can be incorporated to perform static code analysis, vulnerability scanning, and secrets detection. Automated security testing ensures that security checks are conducted consistently, reducing the chances of vulnerabilities slipping through.
Real-time notifications
Developers should receive immediate notifications when security issues are identified. These notifications can be delivered through various channels like email, chat platforms, or integrated development environments (IDEs). Real-time notifications enable developers to respond promptly to security findings and take necessary actions.
Detailed reports and remediation guidance
Security tools should provide comprehensive reports that detail identified vulnerabilities, their severity levels, and recommended remediation steps. These reports enable developers to understand the context of the security issues and provide guidance on how to fix them effectively. Clear and actionable remediation guidance helps developers address vulnerabilities efficiently.
Collaboration with security teams
Collaboration between developers and security teams is crucial in the continuous feedback loop. Developers can work closely with security experts to understand the security findings, receive guidance on best practices, and discuss remediation strategies. This collaboration fosters knowledge sharing, enhances the overall security awareness within the development team, and ensures that security measures are aligned with organizational goals.
Iterative improvement
The continuous feedback loop should be iterative, allowing developers to incorporate feedback, make necessary improvements, and iterate on their code. By continuously addressing security issues and learning from them, developers can enhance their understanding of secure coding practices and incorporate security into their development mindset.
The continuous feedback loop helps developers stay informed about security issues, take prompt action, and build a proactive security culture within the development team.
Addressing security issues found by Snyk and GitGuardian
When tools like Snyk and GitGuardian detect security issues, it is crucial to follow a systematic approach to address them effectively. Here are the key steps to address security issues found in Snyk and GitGuardian:
1. Prioritization
Not all security issues have the same level of severity or impact. It's essential to prioritize the identified issues based on their criticality and potential impact on the application's security. Critical vulnerabilities or exposed sensitive information should be addressed with the highest priority, followed by lower-severity issues.
2. Remediation planning
Once the issues are prioritized, developers should collaborate with security teams to devise a remediation plan. The plan should outline the steps required to fix each identified issue, such as code changes, dependency updates, configuration modifications, or infrastructure adjustments. The plan should also consider any potential dependencies or impacts on other parts of the codebase or infrastructure.
3. Code review and testing
After implementing the necessary changes, conducting a thorough code review and testing is crucial to ensure that the fixes effectively address the security issues without introducing new problems. Code reviews help identify any missed vulnerabilities or weaknesses, while testing, such as unit testing, integration testing, and security testing, helps validate the effectiveness of the remediation efforts.
4. Continuous monitoring
Security is an ongoing process, and it's essential to monitor for new security issues or regressions continuously. Tools like Snyk and GitGuardian provide ongoing monitoring capabilities that can be leveraged to identify any newly introduced vulnerabilities, misconfigurations, or exposed secrets. Developers can maintain a proactive security posture throughout the development lifecycle by continuously monitoring and addressing security issues.
5. Collaboration and knowledge sharing
Addressing security issues found by Snyk and GitGuardian requires collaboration between developers and security teams. Developers should work closely with security experts to understand the nature of the vulnerabilities, receive guidance on secure coding practices, and discuss remediation strategies. This collaboration fosters knowledge sharing and ensures that developers have the necessary skills and knowledge to prevent similar security issues in the future.
A collaborative approach to secure coding practices
Adopting a collaborative approach to secure coding practices is crucial for building a strong security culture within development teams.
Continuous learning and improvement
Emphasizing a culture of continuous learning and improvement is key to staying ahead of evolving security challenges. Organizations should provide resources for developers to stay updated on the latest security trends, attend security conferences or webinars, and engage in security communities. Encouraging developers to share their knowledge and experiences can foster a culture of learning and collaboration within the development team.
Security training and education
Providing comprehensive security training and education to developers is essential. This includes raising awareness about common security vulnerabilities, secure coding practices, and the latest security threats and techniques. Developers should have the knowledge and skills to write secure code, implement secure design principles, and follow security best practices.
Security champions and advocates
Designating security champions within development teams can help drive the adoption of secure coding practices. These champions are developers with a strong understanding of security principles and serve as advocates for security within the team. They can provide guidance, mentorship, and act as a liaison between developers and security teams, promoting security awareness and best practices.
Conclusion
Snyk and GitGuardian provide powerful tooling to enhance DevSecOps practices. With the aid of tools like Snyk and GitGuardian, DevSecOps practices can be strengthened, allowing for more efficient and secure software development processes.
By leveraging Snyk and GitGuardian together, organizations can bolster their security posture, mitigate risks, and maintain a robust defense against evolving security threats.
