Announcing Snyk’s developer-first prioritization capabilities
Daniel Berman
July 22, 2020
0 mins readWe’re excited to unveil Snyk’s developer-first prioritization capabilities, helping development and security teams prioritize fixes for security vulnerabilities in their open source dependencies and containers more effectively!
Organizations today are overwhelmed by growing amounts of vulnerabilities. Since they cannot fix each and every issue instantly, they must prioritize. Effective prioritization helps organizations to stay focused on the vulnerabilities that pose the greatest risk, maximizing the value of time and effort spent and helping to rapidly strengthen the overall security posture of the organization.
But effective prioritization is challenging.
Vulnerabilities are not born equal and their risk variance is influenced by a long list of objective and subjective factors. To prioritize well, deep context is required.Knowing about the existence of a mature exploit, for example, or determining whether the vulnerable function is actually being called by the application, will result in more accurate risk assessment. Even time plays a part—risk diminishes as time passes since the publication date of a new vulnerability.
With this announcement, Snyk is providing a comprehensive suite of developer-friendly prioritization tools to enable organizations to effectively prioritize fixes for the vulnerabilities in their open source dependencies and containers, including instant prioritization, deep application context, and governance at scale.
Accelerate triaging with instant prioritization
The common method used today for prioritizing fixes is using CVSS. While this is a good starting point, this approach also has some limitations. The standard is difficult to decipher and will sometimes result in misleading scores. Even after filtering by severity, organizations still face a long list of vulnerabilities that require prioritization. More fundamentally, severity does not equal risk—or the actual level of exposure to that risk within a given project. To prioritize well, organizations first require an easy and quick way to gain a comprehensive understanding of the risk vulnerabilities pose.
Priority Score
We’re excited to announce Snyk’s new Priority Score—an advanced, built-in scoring system for helping developers prioritize issues quickly and easily.
In order to calculate a score, Snyk’s Priority Score is powered by a proprietary algorithm that processes a wide array of factors, such as CVSS score, the availability of a fix known exploits, how new the vulnerability is, and whether it is reachable or not (more on reachability below!). The score, ranging from 1-1000, is calculated for both security vulnerabilities and license issues and can be used in a number of ways in the Snyk UI and via the API.
On the Projects page within Snyk, the score is displayed at the top-right corner of each issue card. A new option has been added to enable you to filter project vulnerabilities based on the score.

On the Reports | Issuespage in the UI, issues are sorted by default to display the vulnerabilities with the highest score at the top of the list.

To sort through a large number of vulnerabilities more easily in your reports, you can use the new Priority Score filter.

Priority Score is available through all Snyk plans, with reporting and API supported in Standard plans and above.
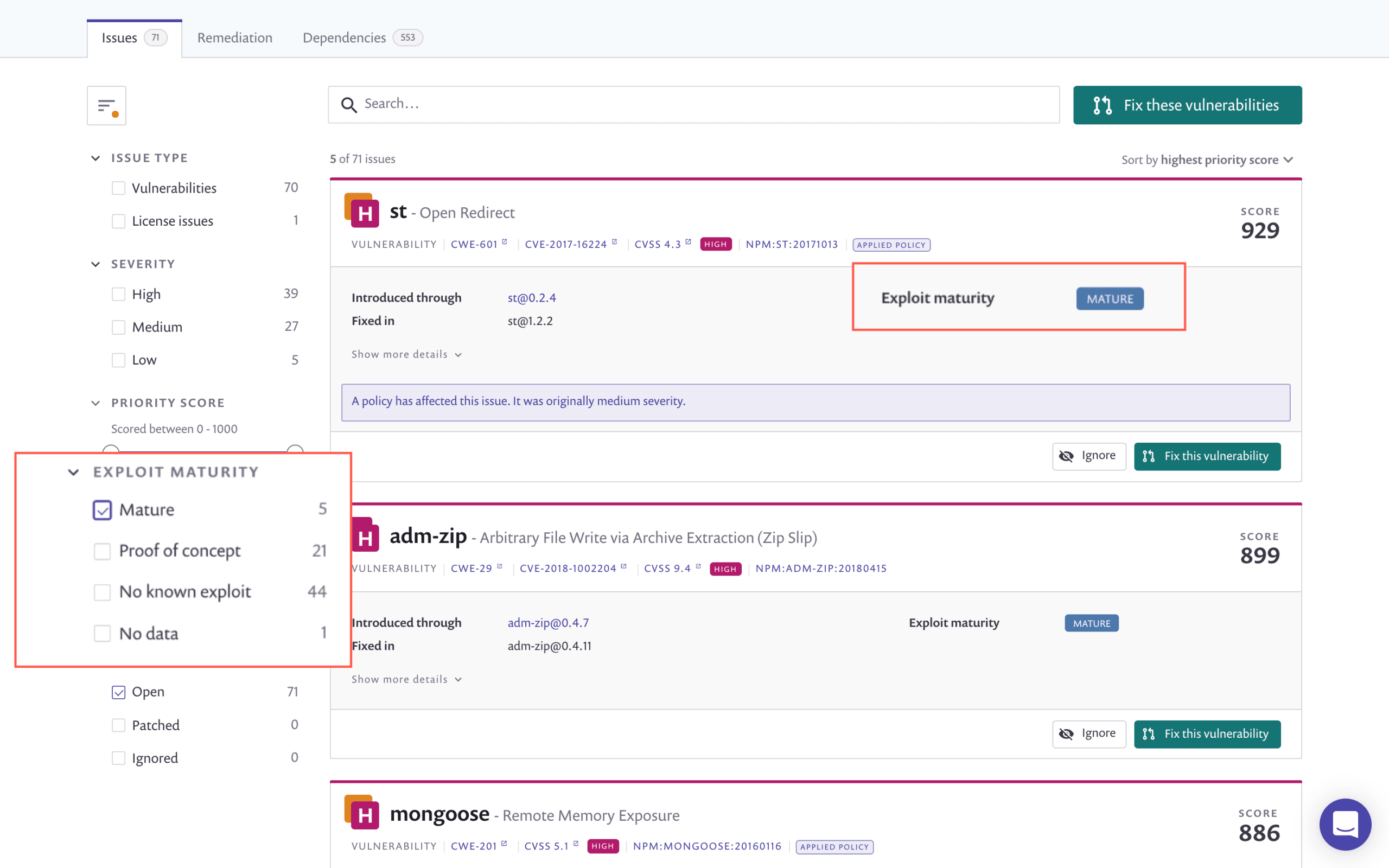
Exploit Maturity
Snyk’s Exploit Maturity—now also supported in Snyk Container—provides another powerful tool for effective prioritization.
Vulnerabilities with an “exploit in the wild” have a higher chance of being exploited and should, therefore, be prioritized over other vulnerabilities with no known exploit. But exploitability is not binary and taking this into consideration, Snyk’s Exploit Maturity not only indicates whether an exploit exists or not but also differentiates between different maturity levels:
Mature: a published code exploit that can easily be used for this vulnerability is available.
Proof of concept: a published, theoretical proof-of-concept or detailed explanation that demonstrates how to exploit this vulnerability is available.
No known exploit: neither a proof-of-concept code nor an exploit were found for this vulnerability, or are not publicly available.
So, just how effective is prioritizing based on exploit maturity? Very! 10% of Java vulnerabilities, for example, have an exploit. But a deeper analysis reveals that only 36% of these exploits are actually “mature”, pose a real and present significant danger, and should, therefore, be placed on the top of the priority list.
This deep security insight—which, as mentioned, is now available for Linux vulnerabilities in Snyk Container as well—is easily accessible within the Snyk UI and via API. Using filters, you can triage issues and create granular reports based on Exploit Maturity.
Prioritize using deep insight into how your applications run
Vulnerabilities are ultimately subjective. Exploiting the same vulnerability in two different applications will have a very different impact. To be effective, prioritization cannot rely on objective characteristics alone and requires deep contextual information about the application and how it is running. Snyk now provides you with an easy way to get this context and make accurate prioritization decisions.
Reachable Vulnerabilities
Providing deeper, application-level context on vulnerabilities, we’re excited to announce the beta of Reachable Vulnerabilities.
Helping you determine whether a vulnerable function is reachable as part of the application’s execution path, Reachable Vulnerabilities complements our runtime monitoring agents that help determine whether a vulnerable function is actually being reached during runtime.
A vulnerability in one part of your code does not necessarily mean that the entire library is vulnerable. Vulnerabilities that are not reachable by your application as part of the execution flow don’t usually compromise the application as a whole and therefore pose less risk compared to vulnerabilities that are reached.
Snyk’s Reachable Vulnerabilities analyzes the application’s proprietary code and its specific interactions with open source dependencies, and maps out a call graph. Correlating the call graph with Snyk’s vulnerability database, Reachable Vulnerabilities determines whether there is a data flow leading through the application to the vulnerable function or package.
Analysis with Reachable Vulnerabilities is initiated via the Snyk CLI, with results displaying the number of vulnerabilities found to be reachable. A reachability level is displayed in adjacence to the vulnerability, and a path from the application’s code to the vulnerable function is displayed below.

Within the Snyk UI, users can use new Reachable Vulnerabilities filters to prioritize based on whether a vulnerability is reachable or not, as well as detailed information on the exact call paths to the vulnerable functions for a faster fix.

Reachability information is also available on the Reports -> Issues tab. You can sort the issues list according to reachability level as well as filter the list using a newly added filter.
Additional information on Reachable Vulnerabilities will be available in a following article, so stay tuned!
Reachable Vulnerabilities is available in beta for all paid Snyk plans: Standard, Pro and Enterprise, and supports Java (Maven) projects only.
Kubernetes prioritization
Poorly configured Kubernetes workload configurations can expose you to risk and should, therefore, be taken into account when prioritizing fixes. Snyk is now happy to provide you with Kubernetes-specific prioritization!
Snyk’s integration with Kubernetes enables you to import and test your running workloads and identify vulnerabilities in their associated images and configurations that might make those workloads less secure. Once imported, Snyk continues to monitor those workloads, identifying additional security issues as new images are deployed and the workload configuration changes.
The Kubernetes workload configurations Snyk tracks, such as CPU and memory limits, permissions and dropped capabilities, are now processed together with vulnerability data to calculate Snyk’s Priority Score. This gives you deeper context into issues identified in your workloads and helps you make more context-informed prioritization decisions.
Kubernetes configuration is available for all paid Snyk Container plans: Standard, Pro and Enterprise.
Automate prioritization across your organization
At scale, it becomes challenging to control prioritization across different projects and teams. Developers need to be able to easily prioritize fixes within boundaries set in place by the security team, preferably in a way that is automated and frictionless.
Enabling organizations to automatically prioritize and de-prioritize vulnerabilities across the board, Snyk is happy to announce the beta of Security Policies!
Organizations can now outline their prioritization strategies in a security policy and apply them to different teams and projects as they see fit. Each policy contains a rule, or a set of rules, that define exactly how vulnerabilities should be handled.

Rules trigger actions based on conditions. Currently, rules can change the severity for vulnerabilities based on their type (for this we use CWE—a common standard for categorizing vulnerabilities based on common characteristics) and Exploit Maturity. A policy might contain one rule, for example, raising the severity for all XSS (cross-site scripting) vulnerabilities and with mature exploits and another rule lowering the severity for RCE (remote code execution) vulnerabilities.
We will gradually be adding more granularity to these rules to support additional actions and conditions, as well as the ability to assign a policy to specific projects using tags and attributes.
Security Policies is available in beta for Snyk Pro and Enterprise plans.
Making it easy to prioritize well
In an ideal “zero-risk” world, organizations would have the time and resources to remediate all the vulnerabilities in their backlog. This, of course, is not possible. Prioritizing fixes is the only available solution but doing this well is a challenge in itself. To be effective, prioritization requires security expertise and deep context to inform accurate decisions.
Providing instant prioritization for accelerated triaging, deep application context to help drive data-informed prioritization decisions, and governance at scale to help organizations manage prioritization at scale, Snyk’s developer-first prioritization capabilities make it easy for development and security teams to prioritize well and, ultimately, reduce risk more effectively.
Get started with Snyk’s prioritization capabilities now!
Get started in capture the flag
Learn how to solve capture the flag challenges by watching our virtual 101 workshop on demand.