Helping Python developers shift security left with a new PyCharm plugin
Daniel Berman
September 8, 2020
0 mins readWe’re happy to announce Snyk’s brand new PyCharm plugin, helping Python developers find and fix security and license issues in their open source dependencies as early as their first lines of code!
Tackling vulnerabilities within the IDE is an important part of shifting security left and enabling developers to take on more responsibility for security as part of their existing workflows. The 2020 “Modern Application Development Security” report by ESG highlights this capability as one of the 10 key elements of an effective AppSec program.
This new PyCharm plugin complements Snyk’s existing list of IDE integrations for IntelliJ and Eclipse, providing developers with wide coverage across a variety of ecosystems and enabling them to shift security as far left as possible.
Snyk for Python
As one of the most popular programming languages used today, it should come as no surprise that Snyk monitors thousands of Python projects a month. Helping our Python users—and the Python community as a whole—to keep their applications secure and compliant is a top priority for us and we’ve continuously invested in introducing new capabilities and enhancing existing ones.
Python applications can be tested via CLI or using our Git-based integrations for GitHub, Bitbucket, and Gitlab. Earlier this year, we added support for automated remediation, helping Python developers not only find vulnerabilities but also quickly fix them with the help of automatic fic pull requests triggered when a new vulnerability is found.
Providing a native integration for PyCharm was the next step. Being the most popular tool for Python development (with a 54% combined share for PyCharm Professional and Community editions, according to the JetBrains 2020 State of Developer Ecosystem survey), we wanted to ensure Python developers had the ability to easily integrate security and license compliance testing into their favorite development tool.
PyCharm plugin key features
Snyk’s PyCharm plugin identifies security vulnerabilities and licenses compliance issues in your open source dependencies. It runs automatically and highlights the issues within the IDE so they can be fixed quickly.
Easy to use: the plugin can easily be installed either from within PyCharm itself or via the marketplace.
Comprehensive and actionable: results show both security vulnerabilities and license issues, together with contextual and actionable remediation information. The plugin supports Pip, pipenv, and PyPi.
Accurate: the plugin is based on the Snyk CLI, which in turn scans your dependencies and correlates finding with the Snyk Intel vulnerability database—the most comprehensive, timely, and accurate vulnerability database in the market.
Getting started
The Snyk PyCharm plugin is free but to use it you need to be a Snyk user.
Before you start, make sure you are signed into the Snyk app and that your Python dependencies have been installed.
To install the plugin from within PyCharm, go to Preferences Plugins, and search for Snyk.
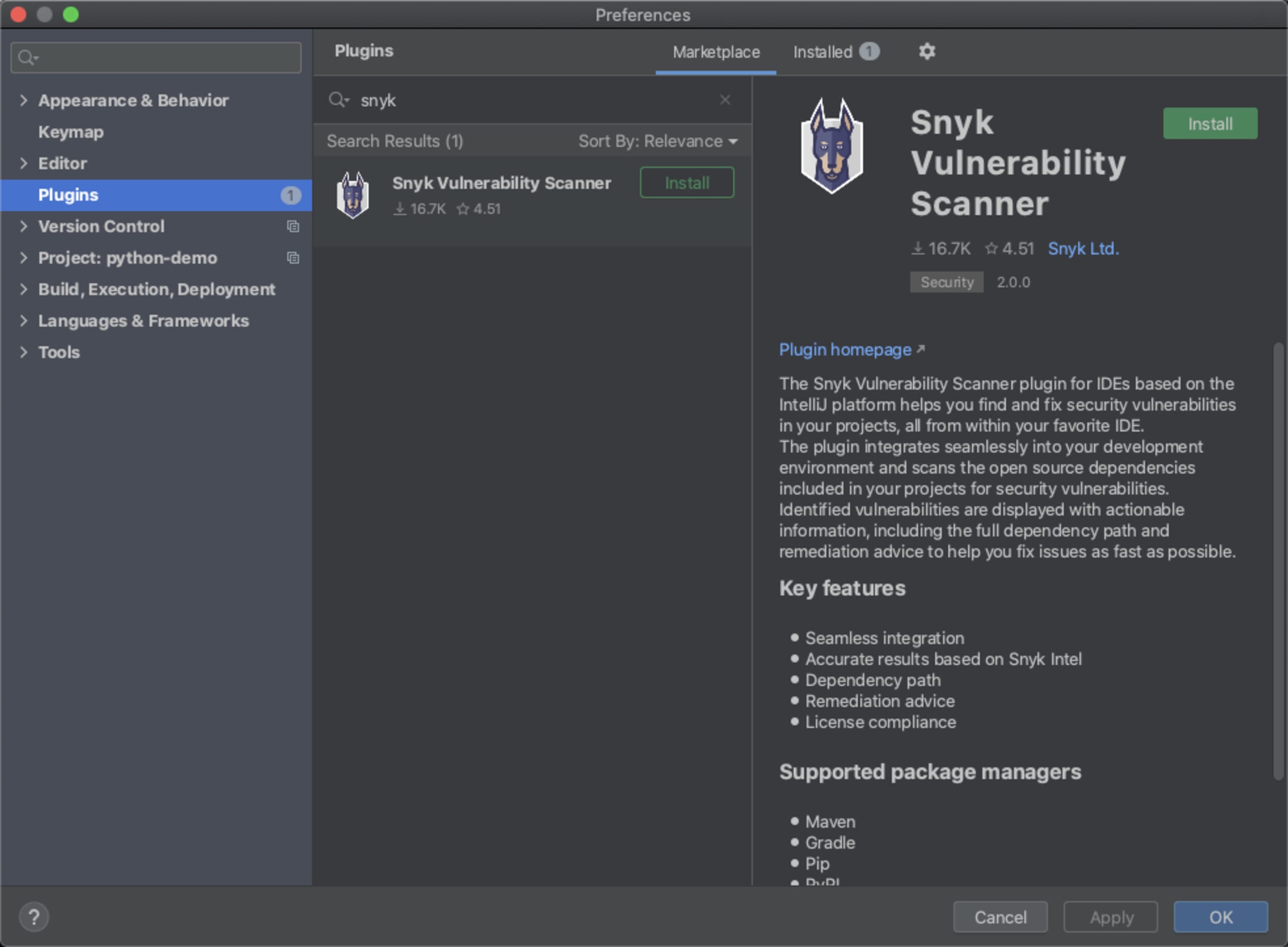
Hit the Install button - PyCharm downloads and installs the latest version of the Snyk CLI and a new Snyk tab appears at the bottom of PyCharm.
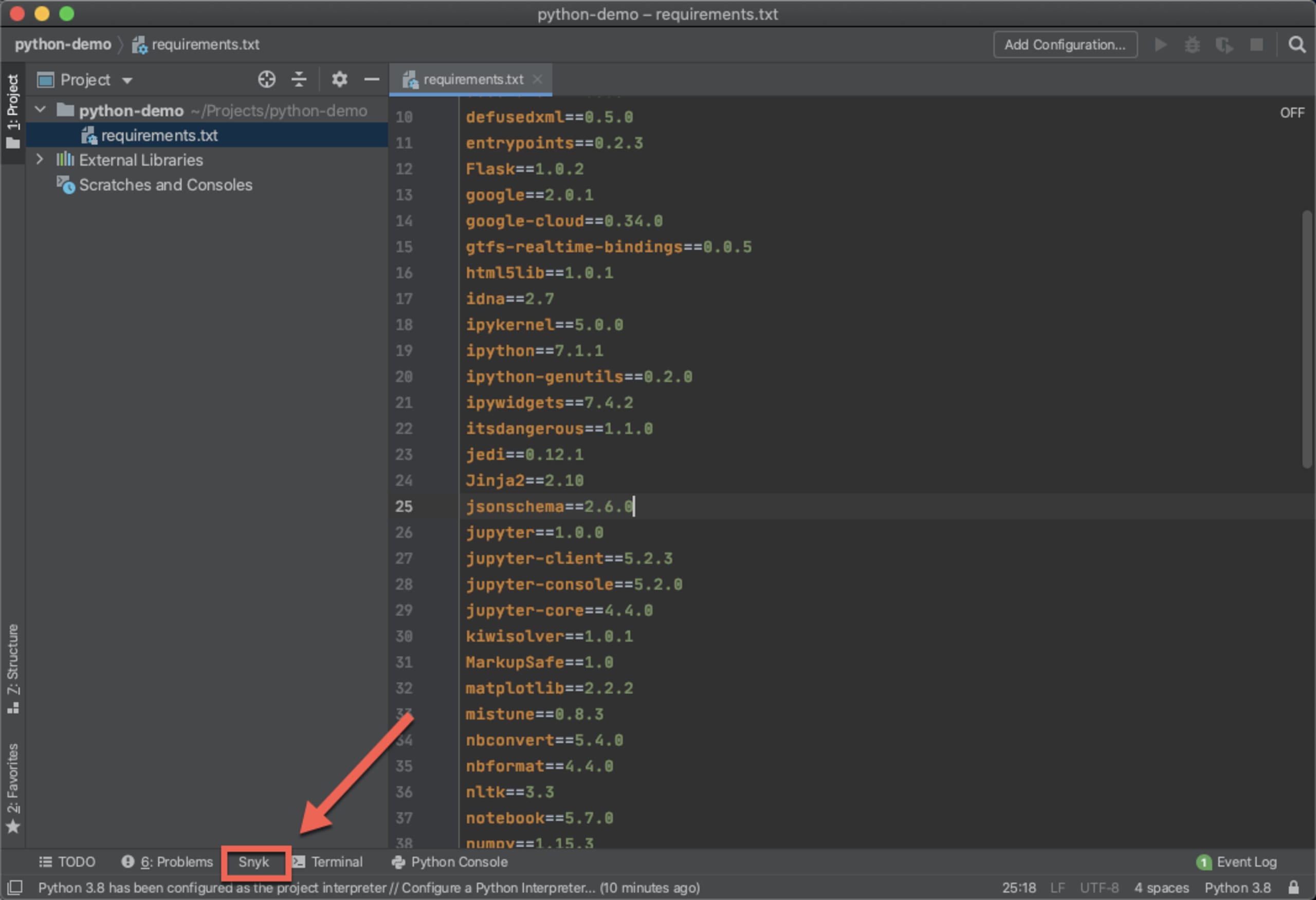
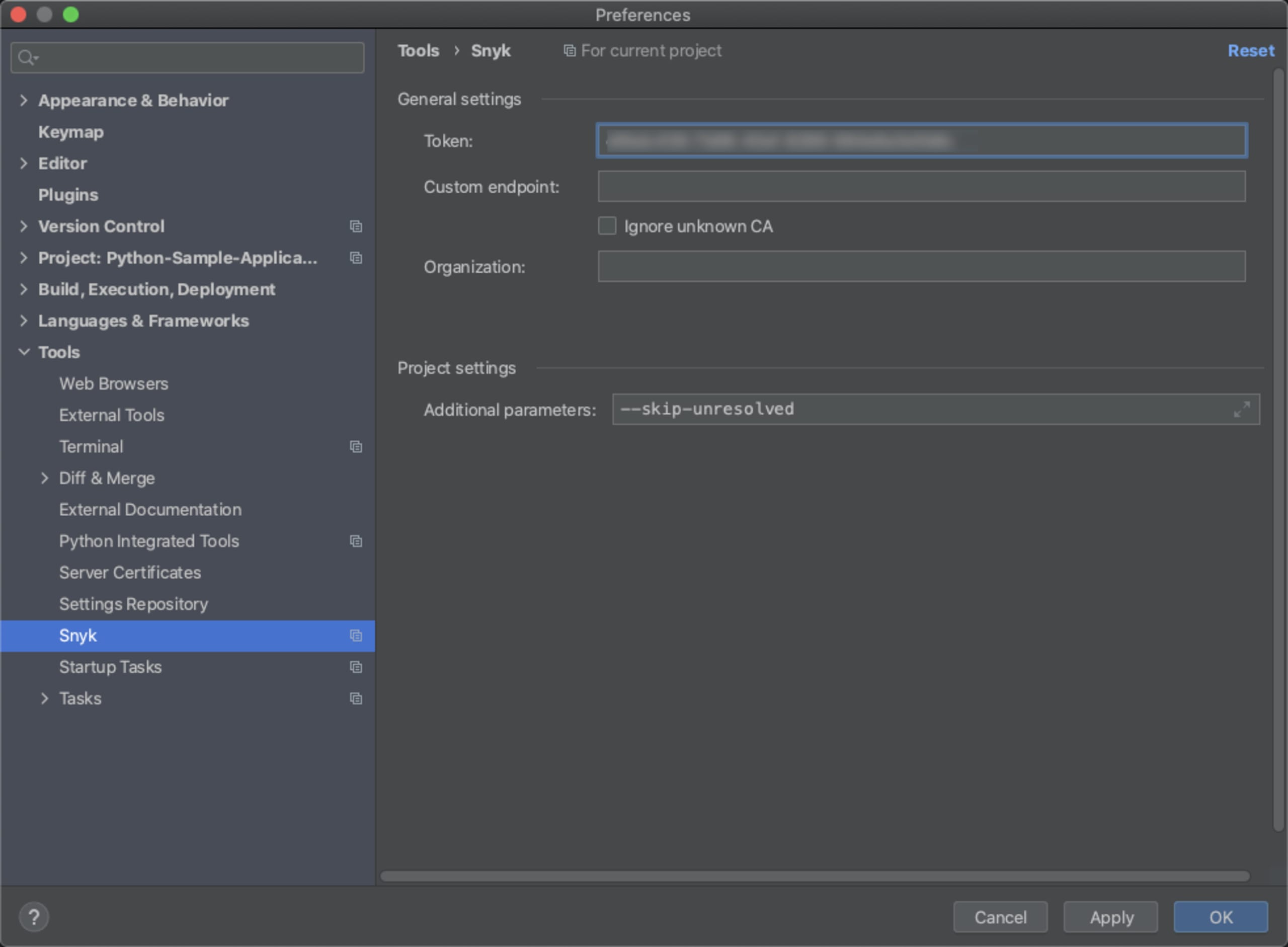
Before you start your first scan, be sure to authenticate your Snyk account. To do this, simply retrieve your API token from within Snyk and add it in the plugin’s settings, at Preferences > Tools> Snyk:
Once successfully authenticated, open the Snyk tab and hit the Scan button to commence Snyk’s security testing. Within a few seconds, should the plugin identify any vulnerabilities, a list of issues will be displayed:
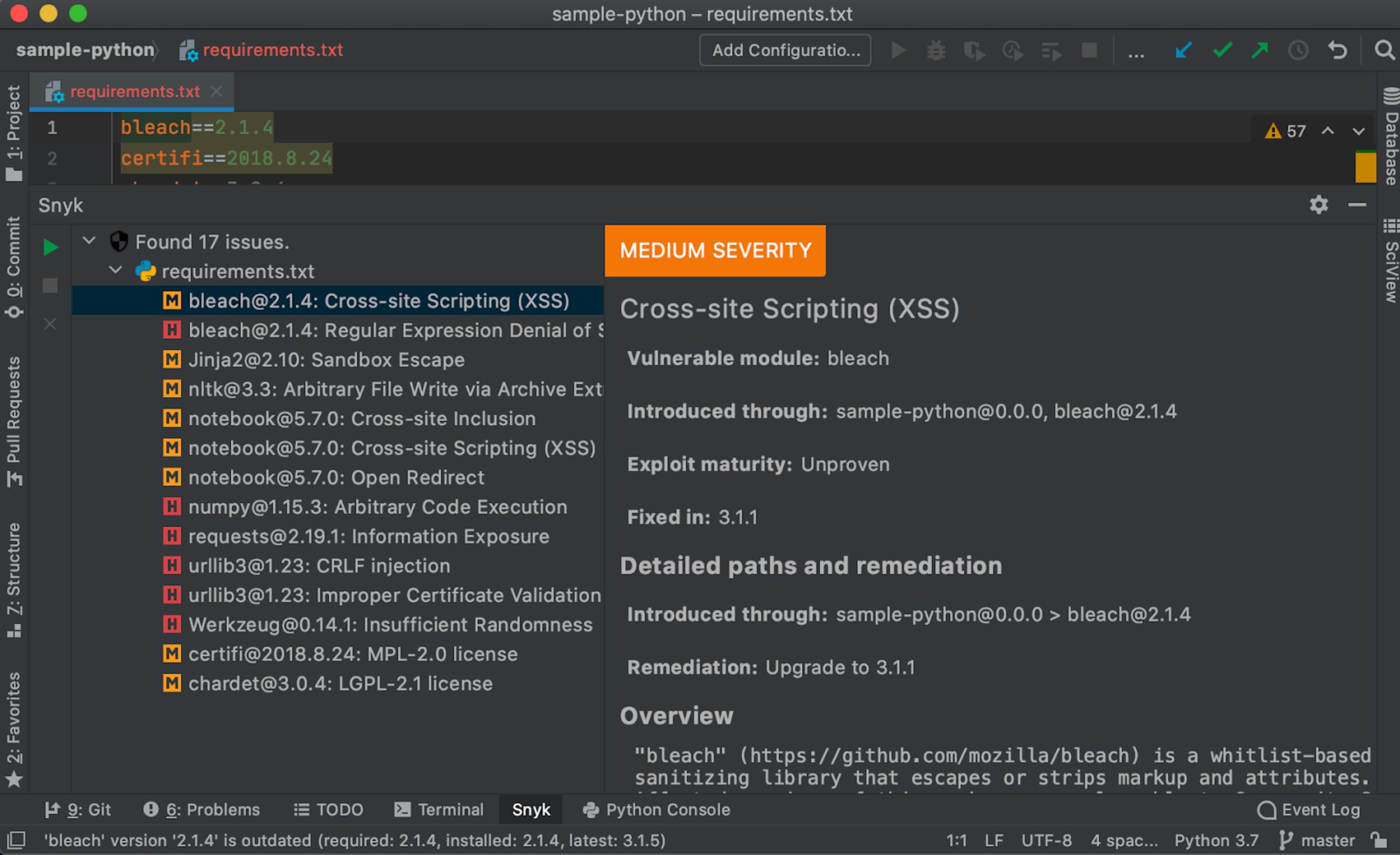
Scan results contain a wealth of information to help facilitate a quick fix, including the severity level for the vulnerability (based on CVSS) and the title/type of vulnerability. Additional details about the vulnerability expose how it was introduced by information on available exploits in the wild while an overview of the vulnerability explains how it can be exploited.
In terms of remediation, the Snyk plugin will help you fix the vulnerability by recommending the upgrade required. Snyk will always recommend the minimal path required to fix the specific issue to ensure minima risk of breakage.
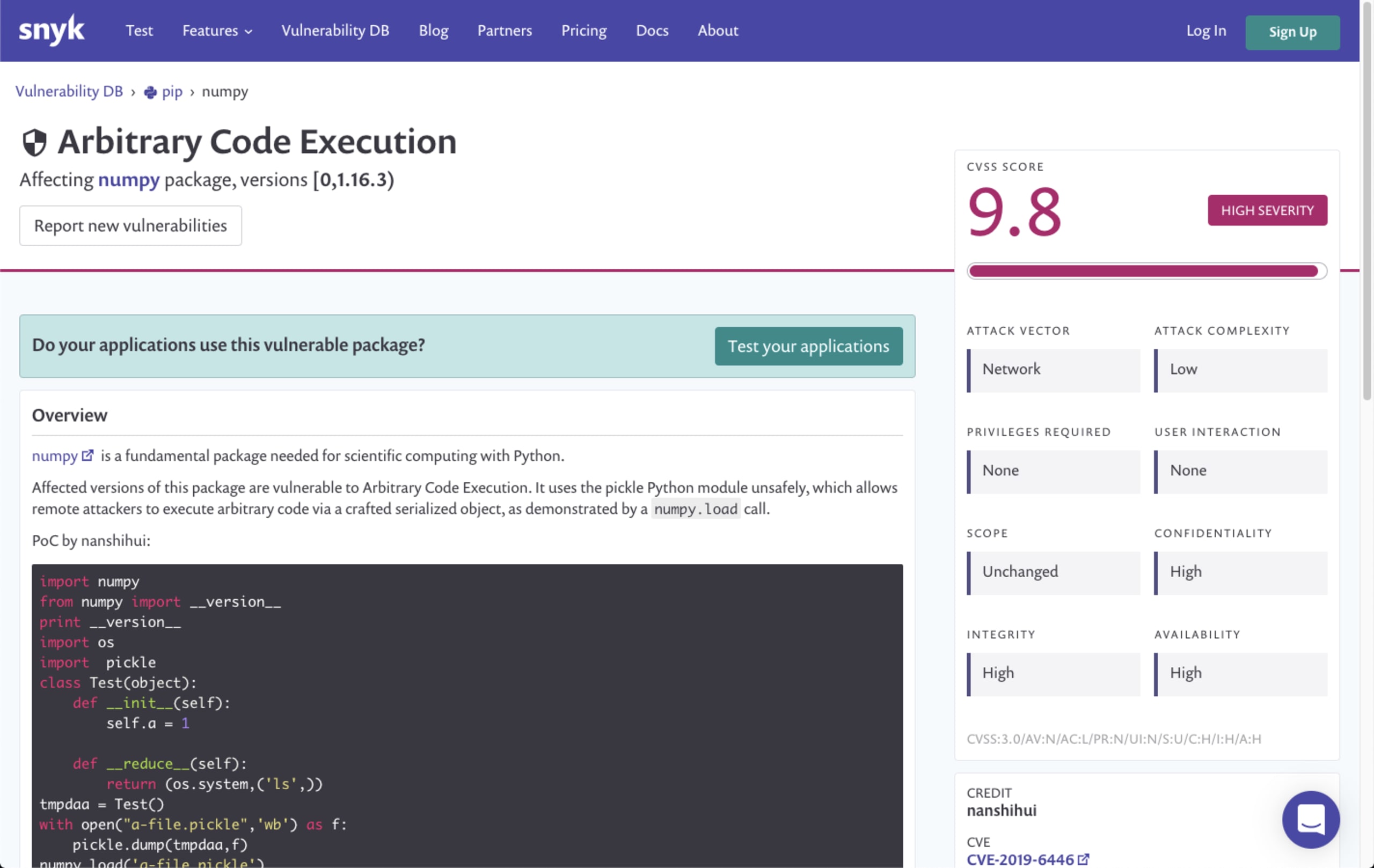
A link at the bottom of the issue details leads you to Snyk’s vulnerability database where you can see additional details on the vulnerability such as its CVE, CWE, CVSS score, and more:
Endnotes
This is the first version of this plugin and we are planning to add additional improvement in the near future. In the meantime, please feel free to send us any feedback you may have so we can prioritize the next set of features!
Happy coding!