Automate container security with Dockerfile pull requests
Danielle Inbar
March 16, 2021
0 mins readIntegration with your source code managers and issuing pull requests to fix issues has been part of Snyk’s success in helping our customers fix application dependencies for several years. Now, we want to help you address container security in a similar way. We’re happy to share that we are extending Snyk Container by helping you automatically fix issues in your Dockerfile to keep an up-to-date base image at all times.

We’ve recently started bringing Dockerfiles to the forefront in Snyk by detecting them automatically from git repos, surfacing their base image vulnerabilities, and advising you on base images you can upgrade to in order to decrease the number of security issues. Now, we want to take it to the next level and do the fix part for you. Starting today, Snyk provides your choice of automatic or manual creation of pull requests containing the needed change in your Dockerfile to use an alternative, less vulnerable base image. This automation continues to improve your team’s efforts in handling large numbers of container vulnerabilities by not only pointing out the container issues early, but also making it simple and fast to mend them as well.
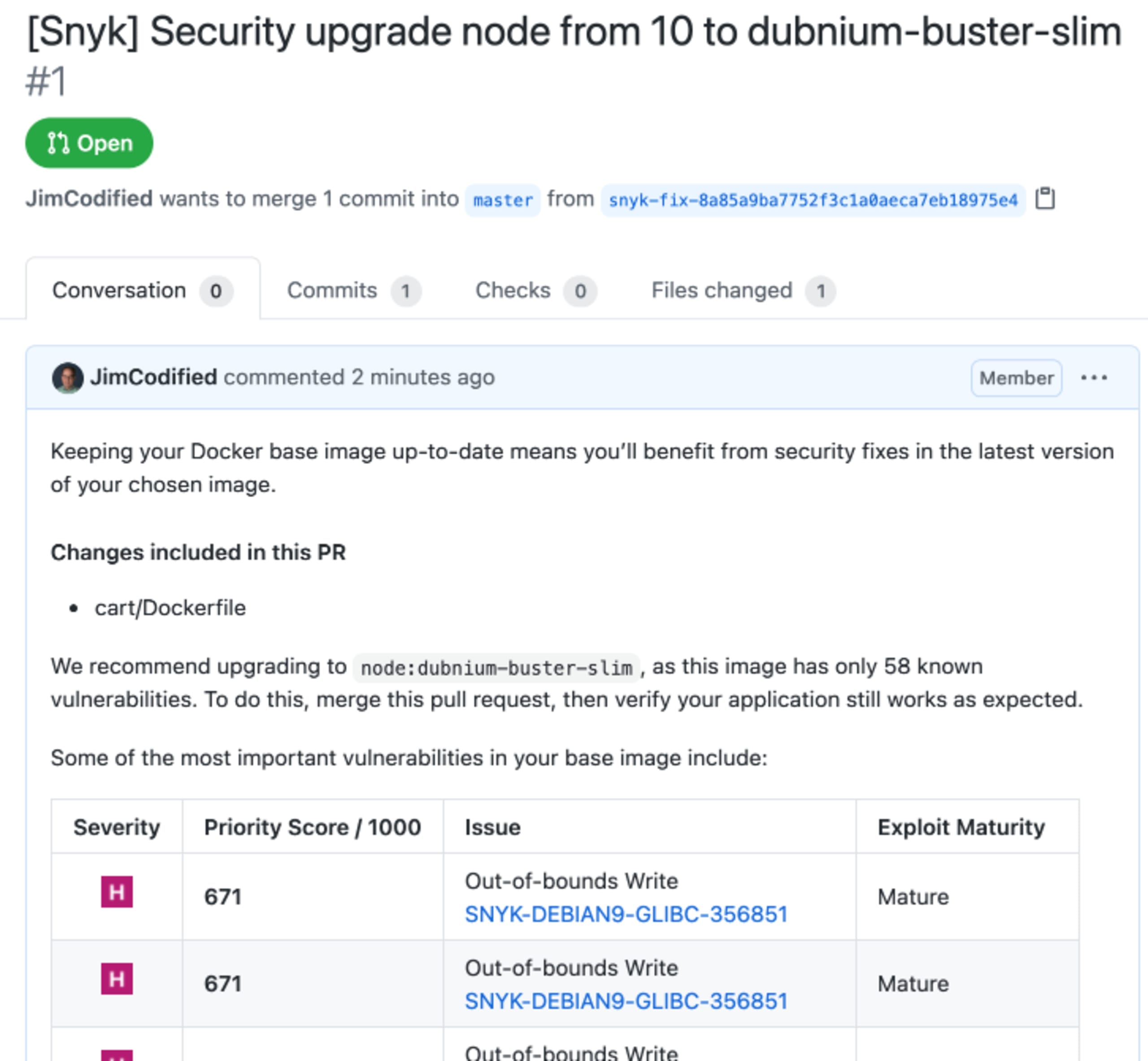
Automated code-level security fixes for containers
Up until now, Snyk provided base image recommendations you could elect to use. In the example shown below, we're using node:10.4.0 as the base image, and Snyk Container shows us that it contains 956 vulnerabilities, out of which 453 are of high severity (as of the time of this writing). For this image, based on data gathered by our security teams, we would recommend using a different base image to lower the security risk. In this example, one of the alternatives will be a minor upgrade to node:10.23.2, which has only 64 high severity vulnerabilities.
The new fix PRs allow you to select other upgrade options, if you prefer, but we also enable fix PRs to be automatically created for minor upgrades.
The new process consists of detecting your Dockerfile and providing you with base image recommendations following the below logic:
Minor upgrade - the safest and best upgrade that does not drastically change the framework versions (Node in our example)
Major upgrades - an option for a major version upgrade that will reduce more vulnerabilities, but with potentially greater risk of application incompatibility due to the major version change
Alternative upgrades - viable alternative image options for replacing your current base image with other, typically slimmer base images that provide an even greater reduction in vulnerabilities, but due to their slim nature they could quite possibly require some additional steps to use
Automated pull requests will be issued for you to review and merge only for the latest minor upgrade base image version. Should you choose to manually open a pull request, you can do so and update to any alternative base-image from our recommendations mentioned above.

Availability
These fix PR features are available now to all Snyk Container users on all plans, including free accounts.
Snyk Container provides base image recommendations and automatic pull requests for Docker Official Images. This curated set of Docker repositories on Docker Hub are designed to provide essential base images that serve as the starting point for the majority of container users and cover a wide range of popular programming language runtimes, data stores, and other services. As part of the Docker Official image program, Docker sponsors a dedicated team that is responsible for reviewing and publishing all content in the official images and this team ensures that security updates are applied in a timely manner. This is particularly important as Official Images are some of the most popular on Docker Hub.
We do have plans to expand beyond Docker Official images and would love your feedback on other sources upstream images you’d like us to cover as well as how you curate your own internal custom images, if that’s part of your process. The new capability is available via the Snyk web UI and API and can be easily configured. We support all git-based repository managers in Snyk, including:
GitHub
GitLab
Bitbucket Server
Bitbucket Cloud
GitHub Enterprise Server
Refer to our documentation for further details.
Let us know what you think
So now you can settle in and let Snyk fix container security issues for you by helping maintain your Dockerfiles with an up-to-date base image. The only thing left for you to do is merge and keep safe!
We are excited to hear what you think so we can keep on improving your experience. If you have any feedback or specific use cases you think should be addressed, let us know.
Developer-first container security
Snyk finds and automatically fixes vulnerabilities in container images and Kubernetes workloads.