Go security: announcing enhanced security for Go applications
Daniel Berman
December 16, 2020
0 mins readWe’re happy to announce enhanced support for Go security in Snyk Open Source and Snyk Container, enabling development and security teams to find and fix vulnerabilities in their Go applications more efficiently!
Go developers can now test and monitor their Go projects across the different stages of the SDLC—starting as far left as their first lines of code within their IDE, using the Snyk CLI in CI/CD pipelines, —and now, also as part of their git-based workflows with the beta availability of Go Modules support in Snyk’s SCM integrations.
It’s all Go!
In this year’s StackOverFlow’s survey, Go was listed as one of the top five most loved and most wanted languages, a ranking it has managed to maintain over the past few years. The number of Go users has been increasing too, reflected in GitHub’s State of Octoverse, and at this point, it’s GitHub’s #4 language, by pull request.
What explains this popularity? Well, Go was purposely designed to be more practical and easy to use. It provides optimized performance, overall lightweight architecture, and a simplistic syntax (there are no classes in Go!). The concurrency provided by Go’s goroutines is an example of why Go is considered an “efficient” language—Uber leveraged this capability to build a service that back in 2017 was Uber’s highest queries per second service. Uber, of course, is not alone. All of the reasons above have made it “the programming language of the cloud”, used by companies like Google, Netflix, and Salesforce, and powering projects like Docker and Kubernetes.
And so, it is not surprising that these trends are reflected in Snyk as well. We are witnessing a steady increase in the number of Go projects being tested and monitored for security vulnerabilities and license issues.
Go security in Snyk
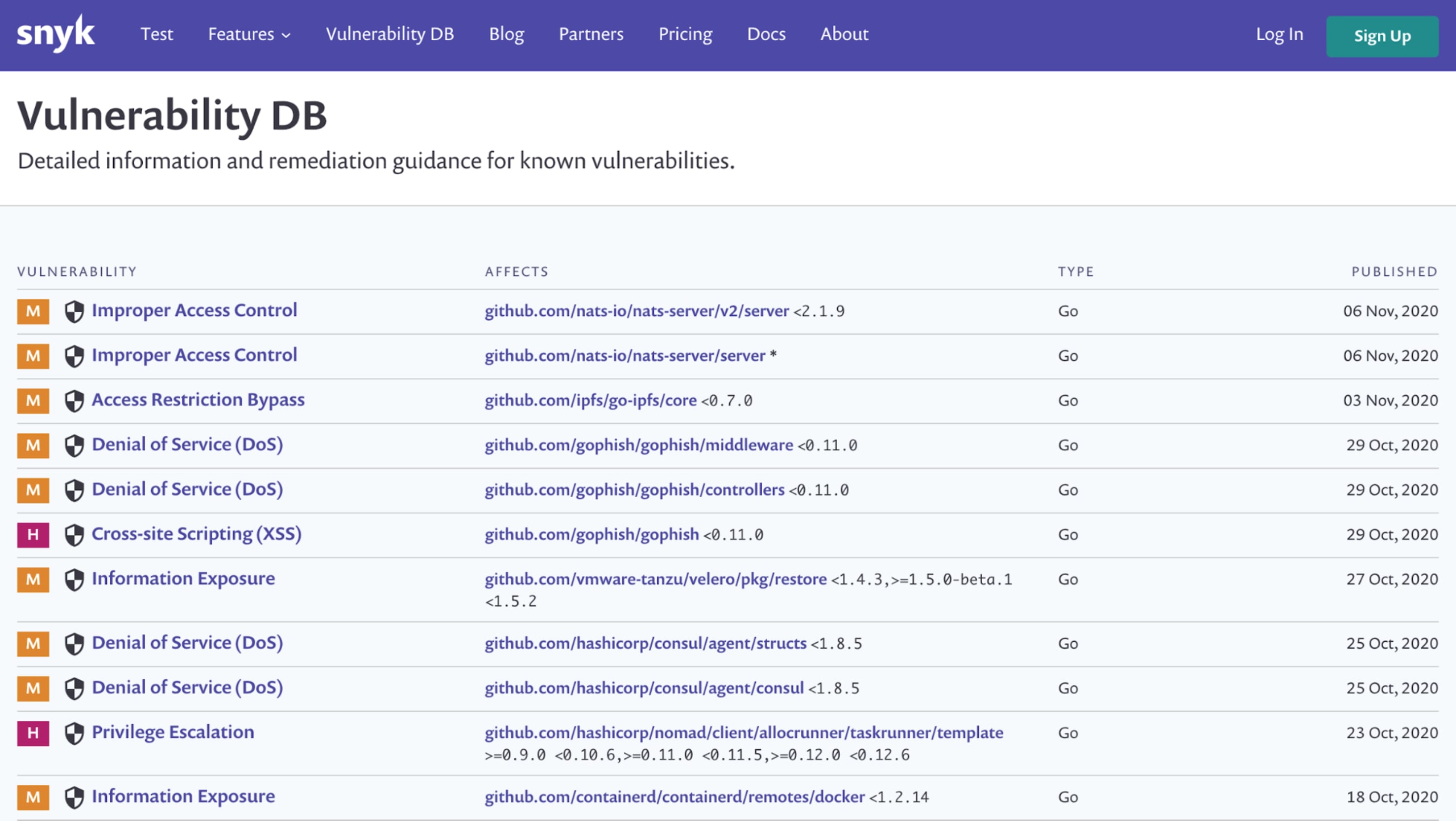
Despite being a relatively new language (Go has been around for just over 10 years), the number of known security vulnerabilities associated with Go packages is steadily growing and so is the risk from pulling in these packages.
According to the 2019 Go community survey, 75% of Go developers state security as being extremely important for them and are satisfied with security in Go. The Go team has also announced future investment in vulnerability curation and testing. These are very positive signs, but just as with more established ecosystems, the risk introduced by pulling in open source dependencies requires management and mitigation.
Snyk provides development and security teams trying to stay secure when building their Go applications with a solution that is easy to implement, facilitates quick fixes, and is powered by accurate security intelligence:
Developer-friendliness - Snyk seamlessly integrates with existing development workflows, scans projects in a matter of seconds (even projects the size of Kubernetes!), and is extremely easy to use, ensuring high adoption and maximized productivity.
Comprehensive coverage - Snyk will identify both security vulnerabilities andlicense issues across the different stages of the SDLC, supporting Go Modules applications, including those running inside containers.
Security depth - Since 2019, Snyk has added hundreds of Go security vulnerabilities to the Snyk Intel vulnerability database. Most of these vulnerabilities are proprietary, are not found in NVD, and are a result of the uncovering work done by Snyk’s security research team.
Go security testing using the Snyk CLI
The Snyk CLI provides you with command-line functions to test, monitor, and remediate known vulnerabilities in your Go open source packages you are pulling into your application. You can use it in an ad-hoc manner, as you develop your application, or as part of your CI (Build) system. The way Snyk scans dependencies, relying on DepGraphs, guarantees that testing even large projects will take seconds.
To use the Snyk CLI, you will need to first install it, and then authenticate it with a Snyk account to get an API token. It’s free!
The snyk test command can then be used to test your local project for known vulnerabilities and will then provide details on any identified issues—their severity, types and descriptions, the number of vulnerable paths, remediation actions, and more.
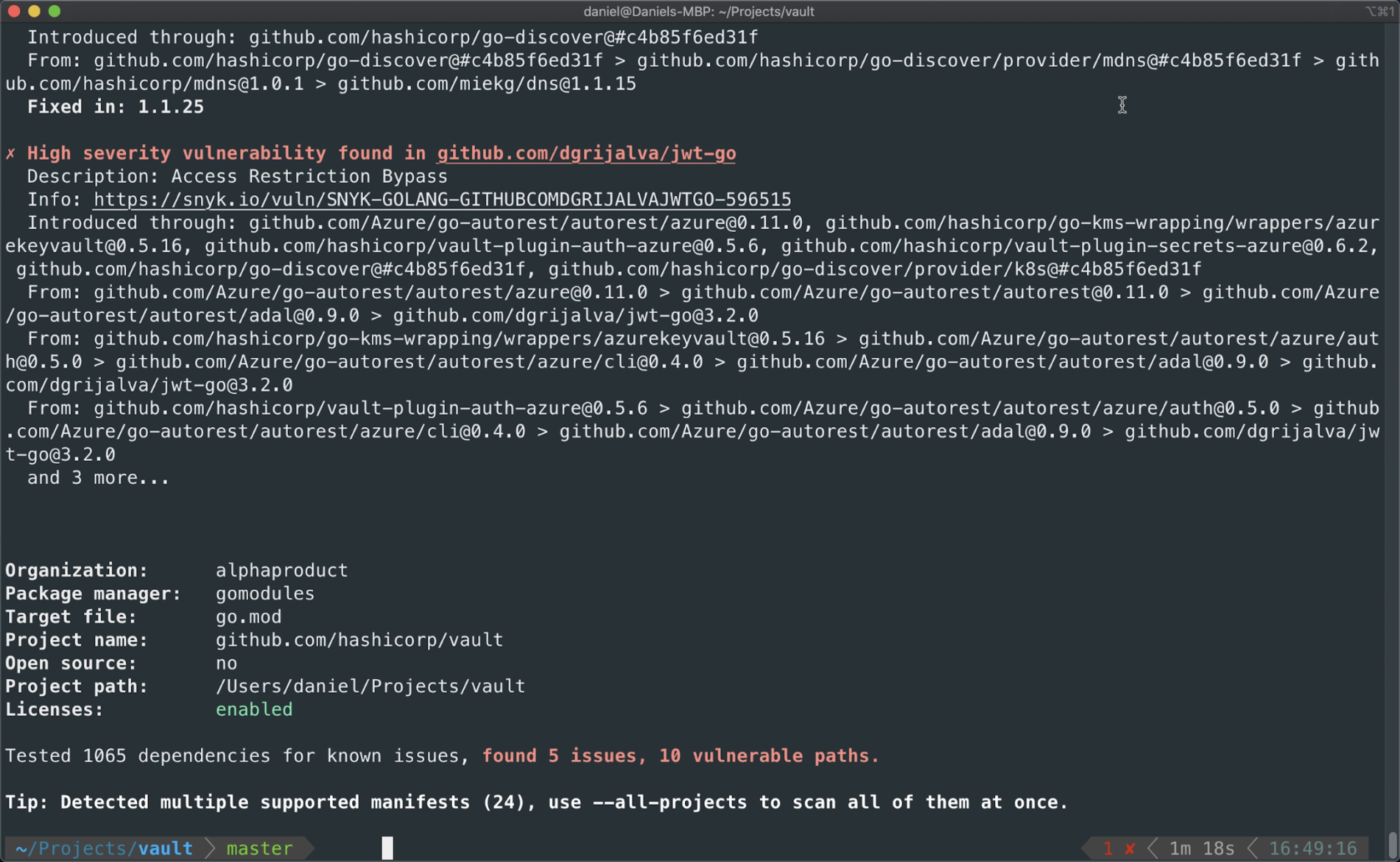
The snyk monitor command also runs snyk test, but takes a snapshot of your Go project and uploads the results to the Snyk app/UI. Don’t worry, we only take a snapshot of your dependencies, not your source code! Your project is then monitored by Snyk, and you will be notified when any new vulnerabilities or fixes are found.
Similarly, if you wanted to test Go applications packaged in a container—perhaps you have containers from a third party where you can’t directly test the source code—you will soon be able to scan them in a single pass as part of your container scans, by either importing an image from a container registry or by using the container functionality of the Snyk CLI. Doing so will indicate both the container vulnerabilities and the Go module vulnerabilities detected. While this type of container scan would detect container and code issues in a single pass, you can still see the results as separate projects, which is helpful where the team responsible for fixing the container issues might be different from the team responsible for the code, and help with reporting on container issues and code issues separately.
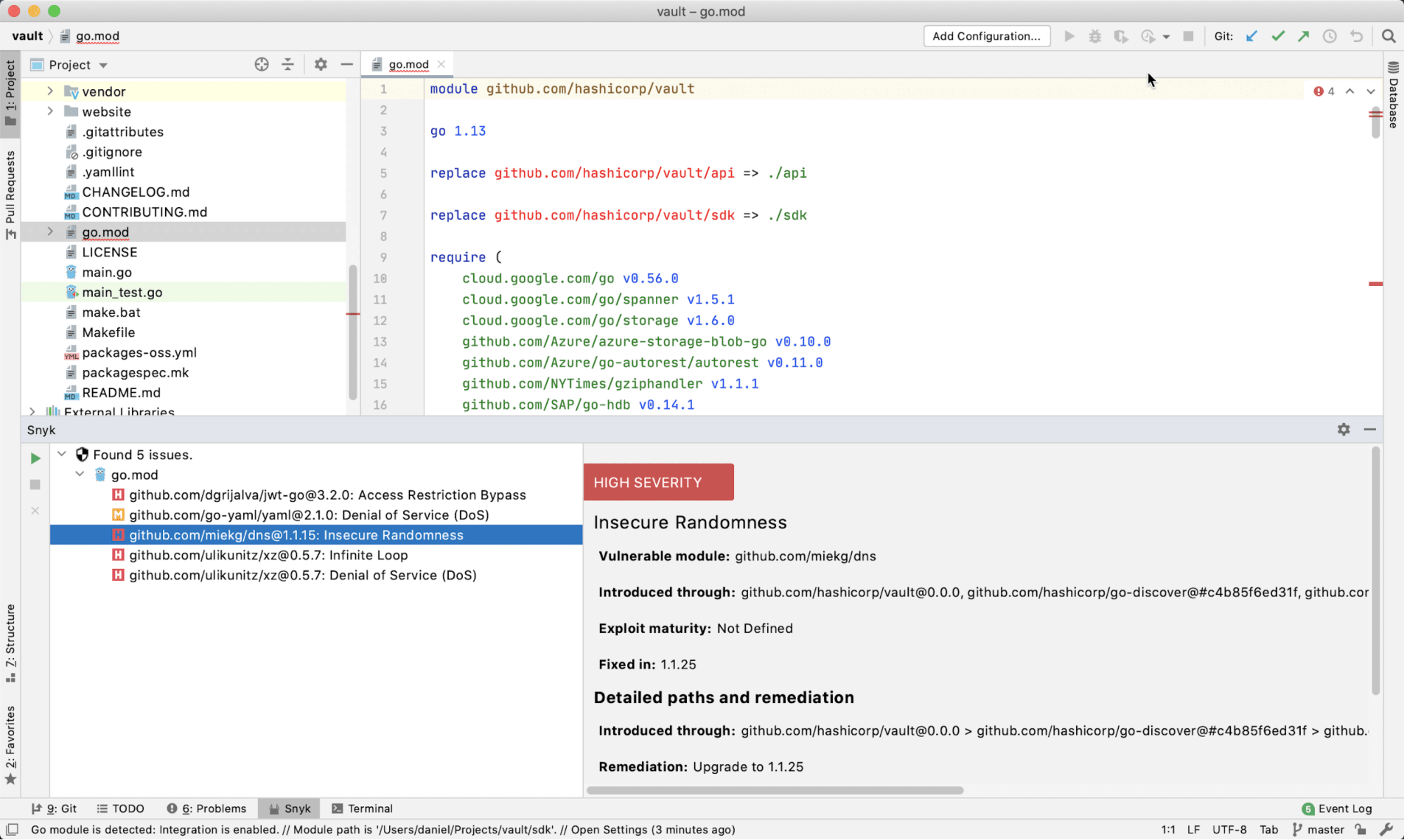
Shifting security for Go projects into your IDE
The further left you can shift security testing, the less costly the fix. Go developers can find and fix vulnerabilities as early as their first lines of code and while using their favorite development tool with a long list of IDE plugins that Snyk provides. This includes a plugin for JetBrain’s GoLand, the second most popular IDE used by Go developers after VSCode according to the same developer survey cited above.
To use the Snyk plugin, they just need to download it from within GoLand, via Preferences, then Plugins.

Once installed, the plugin will download the latest version of the Snyk CLI and once that process is complete, a scan can be performed with results showing within a few seconds. In the example below, a scan of Hashicorp’s Vault project revealed a small number of security issues which we can take a closer look at to understand how to fix them:
New! Integrating Go security testing into your git workflows (BETA)
The latest improvement we are announcing here—the ability to test and monitor Go Modules projects in your repositories—makes security and license testing with Snyk even more efficient.
Snyk's source code management (SCM) integrations allow you to continuously perform security and license scanning across all your integrated Go Modules repositories and detect security vulnerabilities and license issues in the open source dependencies.
After setting up your GitHub or Bitbucket integration and importing your Go Modules project, you will be able to track issues on the Projects page within the Snyk UI:
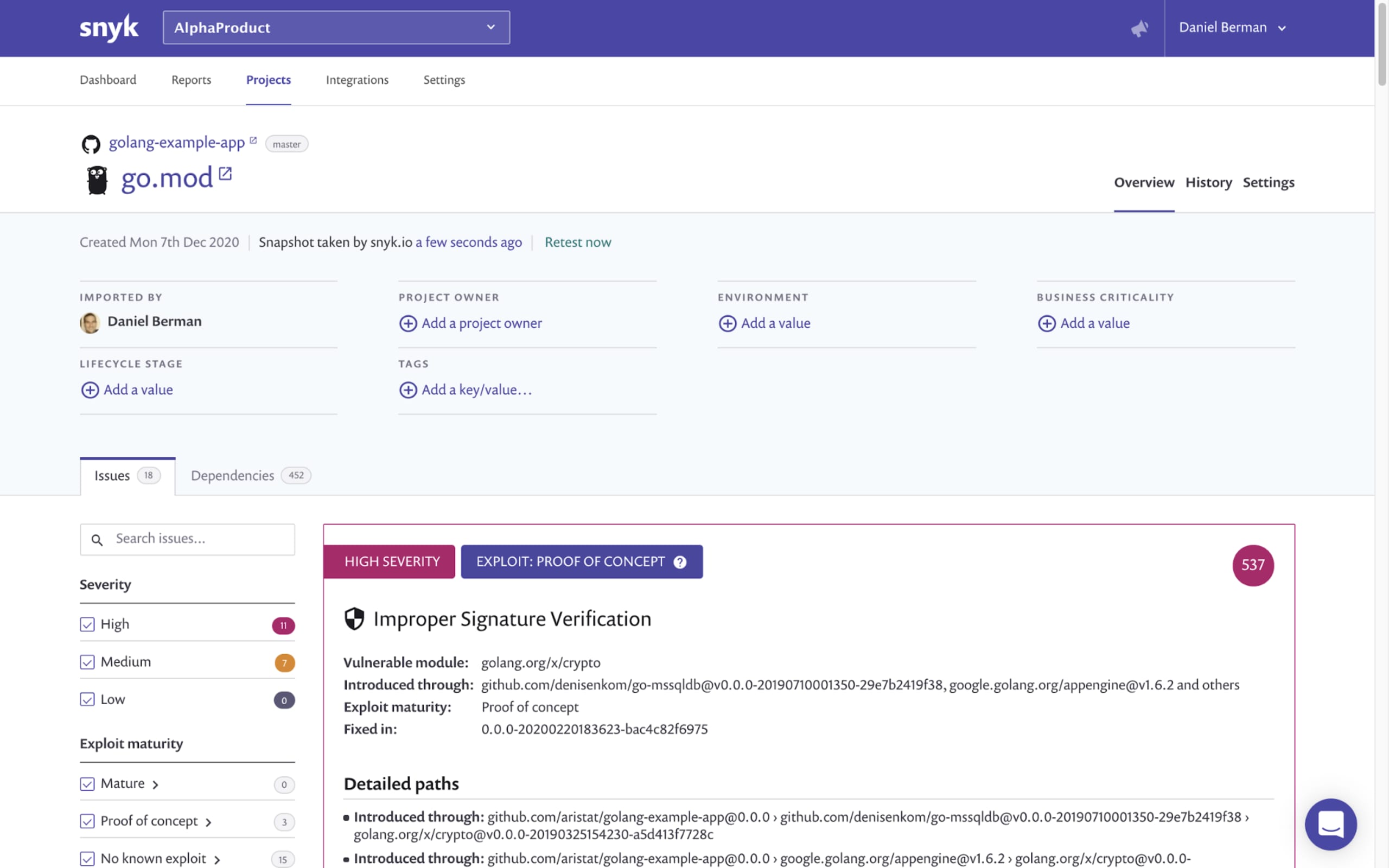
This capability is currently still in beta and will be gradually rolled out. If you want it enabled for your Go projects, please feel free to reach out to our support team!
In case of newly disclosed vulnerabilities identified in your Go dependencies, or when a previously unavailable patch or upgrade path is created, Snyk will notify you via the notification channel you configured.
Ready, set...Go (securely)!
This latest enhancement follows recent improvements made to the performance of security testing for Go projects via the Snyk CLI and augments Snyk’s developer-friendly, comprehensive and security-deep solution for securing Go applications.
Given the growing popularity and rapid adoption of Go, and to comply with the growing needs of our own users, we are committed to improving our support of this ecosystem. Looking into 2021, we will also be enhancing remediation workflows to make it easier to automatically fix Go vulnerabilities.
Using Go and want to get started? Try Snyk for free!
Get started in capture the flag
Learn how to solve capture the flag challenges by watching our virtual 101 workshop on demand.
