2018 Year in Review
December 31, 2018
0 mins readFirst and foremost we would like to wish you a Happy New Year and sincerely thank you for championing open source security and helping us make the world a little safer!
A security retrospective
2018 has seen its significant share of severe security incidents across the different ecosystems.
Snyk’s security research team publicly disclosed a critical arbitrary file overwrite vulnerability back in June that affects thousands of projects including ones from Amazon, Apache, Pivotal, and many others. You’re welcome to read our research paper about the critical Zip-Slip vulnerability that may potentially result in a remote command execution vulnerability.
A community effort in November unraveled the mystery of a malfunctioning package which led to the discovery of a malicious dependency tricking its way into the popular event-stream package if only to execute a sophisticated targeted cryptocurrency attack. If you missed it, check out our post-mortem on this incident.
Moreover, JavaScript developers may recall another incident back in July of a malicious version of eslint-scope which compromised a maintainer’s account and resulted with npm staff resetting all access tokens prior to the incident across the board.
Other security incidents that made the news in 2018:
A critical vulnerability found in Kubernetes
A critical vulnerability in Spring Boot
Attacking FTP clients for path traversal affecting multiple vendors
Did you know you cancrash an e-mail server with just… sending an email?
Keeping you informed
- How many are using Java SE 8 in production?
- Is Spring Boot catching up in popularity?
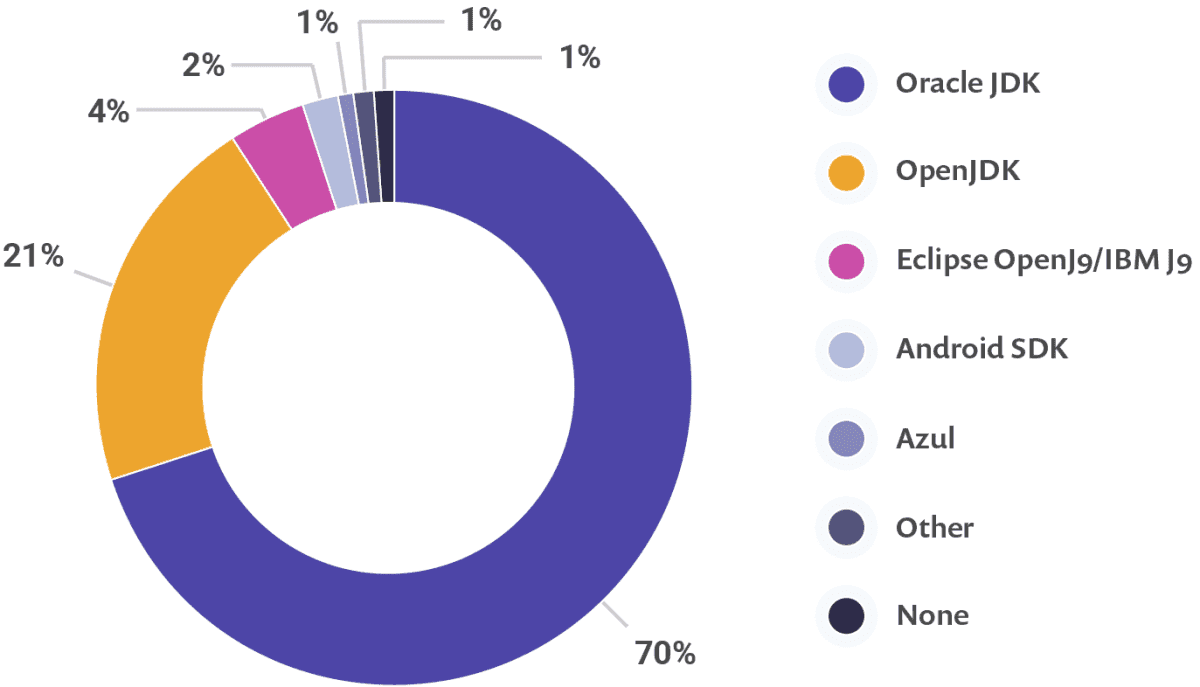
You’re welcome to find out all about the JVM ecosystem in astate of the JVM Ecosystem 2018 report that we released earlier this year. It surveyed over 10,000 participants to reflect about the JDK, your toolbox, platform and applications.
Make 2019 even better by getting ahead and using one of the several cheat sheets we wrote:
Snyk features you might have missed in 2018
For all Docker fans: you can now use the Snyk CLI to scan for vulnerabilities in your Docker images. Snyk’s docker image remediation advice will also recommend base images based on your Dockerfile with fewer system libraries vulnerabilities to keep you more secure!
As with regular projects, you can monitor the docker image for new vulnerabilities being disclosed and we will track it for you in Snyk’s projects page to let you know.
You can take Docker scanning for a test drive in your open source projects as part of the free tier of up to 100 tests. Check it out:
Our new Runtime Monitoring will help you prioritize security fixes by detecting vulnerable code in your application during runtime. Once we’ve detected an invocation of a vulnerable function, we will indicate it in the issue card, which also shows the vulnerable paths so you can take immediate action to mitigate the security issue.
The feature is currently in closed beta and available for Java and Node.js projects, but we’re offering early access. If you’d like to try it out, please email us at runtime@snyk.io!

What else we've been up to this year:
Our API is available for paid plans and has been extended to allow you to query for all the security issues in a project so you can build your own dashboards, reports, or other integrations. You can even bulk import all of your projects through the API.
We integrated with Google’s Lighthouse tool toinform you of vulnerable frontend libraries in your web application. If you’re usingMicrosoft’s Sonar we've got your back, too!
Enthusiastic IntelliJ developers might be happy to explore ourSnyk IDE Plugin.
Our source control integration is not new but we wanted to remind you how easily you can connect your projects on GitHub, BitBucket Server or GitLab to receive automatic Pull Requests updates with fixes.

Growing Stronger
We had an amazing year featuring two investment rounds totaling nearly $30M and saw immense growth in our product adoption:
More than 200k developers choose Snyk to keep open source security in check
The Snyk CLI is downloaded more than 500k times every month
We open more than 10,000 Pull Requests every month to secure projects dependencies
We were humbled and honored to have Gartner name Snyk as a 2018 Cool Vendor in Application and Data Security, and see ThoughtWorks highlight Snyk in the recent Technology Radar edition.This further amplifies the support of the community and the importance of helping developers bridge security early on.

The size of our team tripled in 2018 and there might be a spot for you if you want to be a Snyker too! All in all 2018 was a great year, and we’re looking forward to making 2019 an even more secure and better one!
Thanks for your support!
- The Snyk team
Get started in capture the flag
Learn how to solve capture the flag challenges by watching our virtual 101 workshop on demand.





















