How to integrate ASPM with your application security program
November 28, 2023
0 mins readApplication security posture management (ASPM) enables AppSec teams to continuously monitor, manage, and improve the security health of software applications throughout their lifecycle. It provides a framework for ensuring that applications are built securely from the start, maintained with security in mind, and continuously monitored for vulnerabilities that introduce significant risk to the business. With ASPM, we get aggregated data in a unified dashboard. It keeps a constant watch, ensuring apps are secure from when they're made to their daily use. Check out our explainer article for an introduction to ASPM.
ASPM has the ability to consolidate a wealth of security-related data into a single, accessible dashboard. ASPM helps organizations prioritize and manage the AppSec resources efficiently. Organizations can easily get a bird's eye view of their software's security status without sifting through disjointed pieces of information across the different R&D groups in the organization. Acting like a vigilant sentinel, ASPM never takes its eye off the applications, ensuring that at every stage of their life, from creation to daily operations, they remain fortified against potential security breaches.
ASPM is more than just industry jargon or a buzzword in high-level meetings. It's a paradigm shift in how security teams operate. Rather than using security terminologies to intimidate or create a sense of urgency, ASPM provides a structured and actionable plan. It empowers security professionals to define, implement, and manage security standards proactively. As a result, not only does the software development process become more secure, but it also becomes more streamlined, bridging the often-discussed divide between development and security teams.
Key components of ASPM
Visibility throughout the application lifecycle
ASPM provides a complete view of every software asset from code to cloud, integrating data from security tools and runtime environments. AppSec teams, developers, and business leaders are able to share a common understanding of the applications and their business importance, which translates to a shared understanding of security risk and, ultimately, to leading an effective AppSec program.
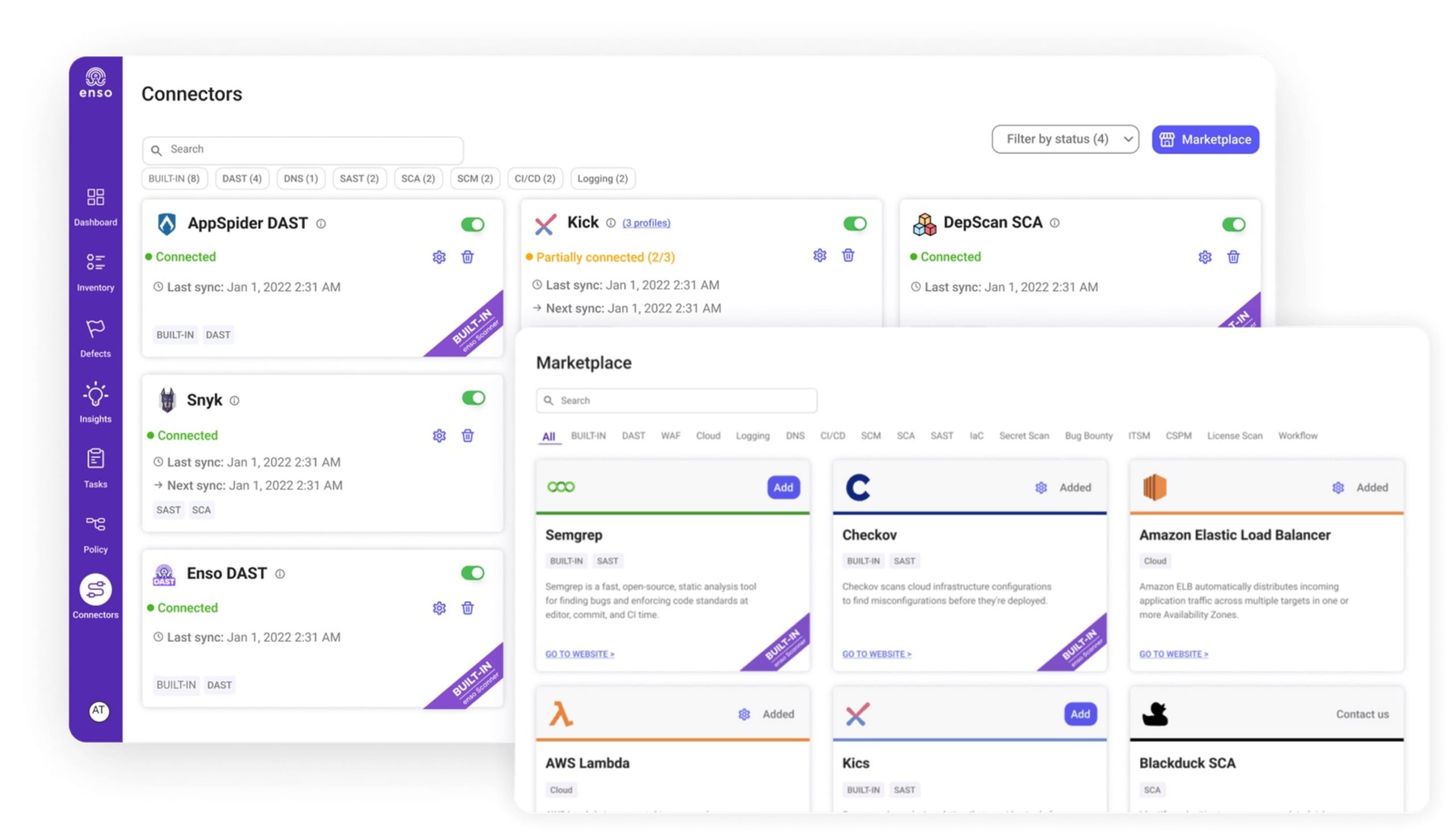
Govern and manage security coverage
With ASPM, AppSec teams can define the controls required for each application based on its business importance and threat profile and implement automated policies to be certain those controls are applied consistently and correctly across the organization's application landscape. They will also be able to set guardrails for developers to ensure the correct tools are in place and to guide them to prevent issues early in development and identify and fix serious new issues as they are disclosed.
Prioritize based on risk
The app's visibility from code to cloud and integration of additional runtime data and controls provide the AppSec team with the complete picture of risk for all their applications. With these insights, ASPM enables AppSec teams to guide and focus developers on the handful of issues that truly matter.
Snyk, in partnership with Enso, now offers an ASPM control center that gives AppSec teams increased visibility into the assets, more control over vulnerabilities, and governance tools to ensure their programs effectively reduce risk. You can learn more at our ASPM solutions page.
How ASPM fits into the lifecycle of application security
Software development isn't just about writing code and deploying it. There's a whole lifecycle to it, from the moment an idea sprouts to the time it's actively used by people. During each of these stages, security plays a crucial role.
Let's break down the software development lifecycle (SDLC) and see where application security posture management (ASPM) comes into play.
Planning and analysis: Security teams can map out their planned assets and identify potential risks right from the start. They can also establish security requirements the software must meet.
Design: Security should be baked into the design. This is the phase where you decide on secure coding practices, consider potential vulnerabilities in the architecture and its associated assets, and plan for secure user interactions.
Implementation (or coding): As code is written, it should be regularly scanned for vulnerabilities. ASPM tools can catch issues like weak encryption or potential unauthorized access points. ASPM's magic lies in its ability to identify business-critical assets and prioritize vulnerabilities affecting them.
Testing: Alongside functional tests, security testing is crucial. ASPM can help aggregate data from security-specific testing tools, checking for vulnerabilities in business-critical assets that might have been missed during coding.
How ASPM makes organizations more secure
Proactive defense
Instead of just finding vulnerabilities, ASPM focuses on maintaining a strong security posture. ASPM solutions constantly monitor the applications to ensure they adhere to best security practices. Instead of waiting for periodic security audits or scans, ASPM ensures real-time surveillance of application security. This constant vigilance means potential threats can be identified and neutralized before they escalate into bigger problems.
For instance, consider a situation where a development team inadvertently uses a library known to have vulnerabilities. In a reactive model, this vulnerability might only be discovered during the next scheduled security audit, which could be weeks or even months away. However, with ASPM, the use of this vulnerable library could be flagged immediately, allowing the team to replace or patch it before it becomes an exploitable weakness.
Reduced attack surface
By identifying and remedying vulnerabilities or misconfigurations early. ASPM helps identify vulnerabilities or misconfigurations as soon as they are introduced, allowing for immediate remediation. This rapid response ensures that potential entry points for attackers are minimized.
Consider a cloud-based application that mistakenly exposes a database to the public due to a misconfiguration. In a traditional setup, this misconfiguration could go unnoticed until a breach occurs or a routine security check flags it. With ASPM, the moment such a misconfiguration happens, it's identified, alerting the responsible teams to rectify it, thus minimizing the time the database remains exposed.
Informed decision-making
ASPM offers decision-makers clear insights into the application security landscape, facilitating risk-aware decisions. Armed with a clear understanding of the application's security landscape, organizations can mitigate risk, prioritize remediations, and allocate resources more effectively. This isn't just about identifying weaknesses. It's about understanding the broader security context, including potential threats, the relevance and criticality of identified vulnerabilities, and the implications of proposed changes or additions to the application.
For example, when integrating a new third-party service into an application, decision-makers can utilize insights from ASPM to understand potential security implications. If the ASPM tool indicates that this service has had several security-related incidents in the past or that its integration would greatly expand the application's attack surface, the organization can weigh these factors against the benefits of integration, leading to a more informed and risk-aware choice.
Level up your security with ASPM
Application security posture management (ASPM) is crucial as software drives most business functions. A robust ASPM strategy not only protects the business from potential cyber threats but also ensures continuity, builds customer trust, and aids in regulatory compliance. As threats continue to evolve, the role of ASPM in safeguarding applications becomes even more pivotal.
ASPM is like our digital bodyguard for all the apps and software we rely on. It ensures everything runs smoothly, keeps the bad guys out, and helps us follow industry-specific rules. As the digital world keeps growing, ASPM's role in protecting our apps becomes increasingly crucial. ASPM isn't just a tool you use at one point in the SDLC. It's a constant companion, ensuring that security remains a top priority at every stage.
Unlock DevSecOps with Snyk
Overcome application complexities and AI hallucinations while fostering collaboration between dev and sec teams with insights from Snyk and Accenture.