Find and fix vulnerabilities in Artifactory container repositories
February 8, 2020
0 mins readWe’re excited to share that you can now scan container images stored in JFrog Artifactory with Snyk Container. Snyk Container helps you find and fix vulnerabilities in your container images and integrates with Artifactory as a container registry to enable you to import your projects and monitor your containers for vulnerabilities, as is fully described in our container vulnerability management documentation. Snyk tests the projects you’ve imported for any known security vulnerabilities found, testing at a frequency you control. Integration with Artifactory is available for our Pro and Enterprise pricing plans.
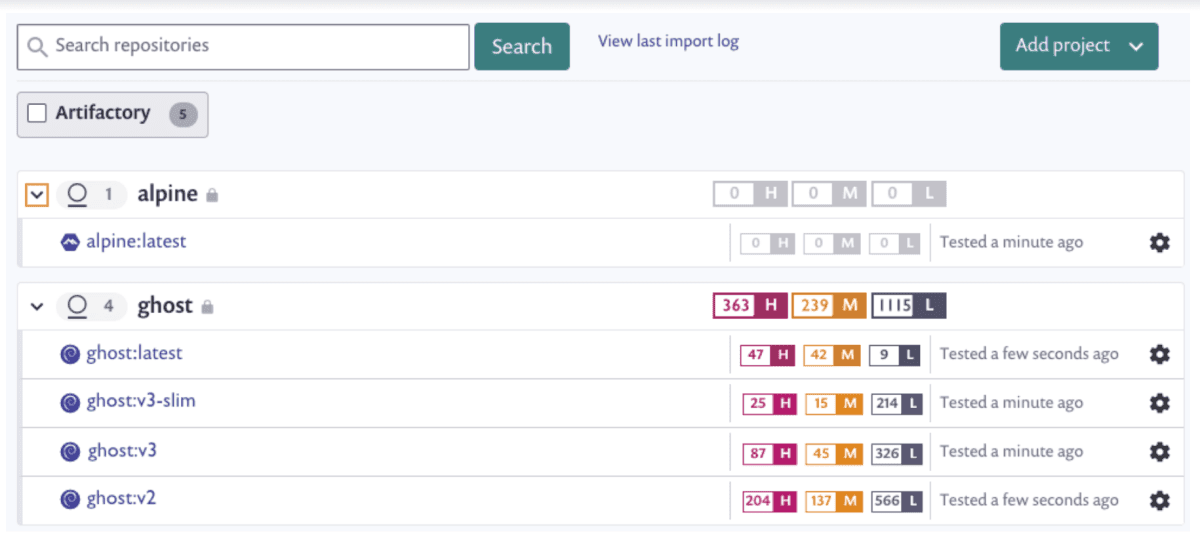
Snyk Container provides base image upgrade recommendations, to help you quickly optimize how you build your containers, and includes Iayer identification features, enabling you to focus your efforts on the problematic lines in your Dockerfile.
Optimize base images
Snyk helps you identify and select alternate base images to help reduce the overall number of vulnerabilities in your container images. Often there are a number of base image alternatives available, especially for popular official Docker images. Snyk Container can determine the base image you’re currently using and provide recommendations for upgrades with fewer vulnerabilities.
The following shows base image recommendations for the `node:10.4.0` image:
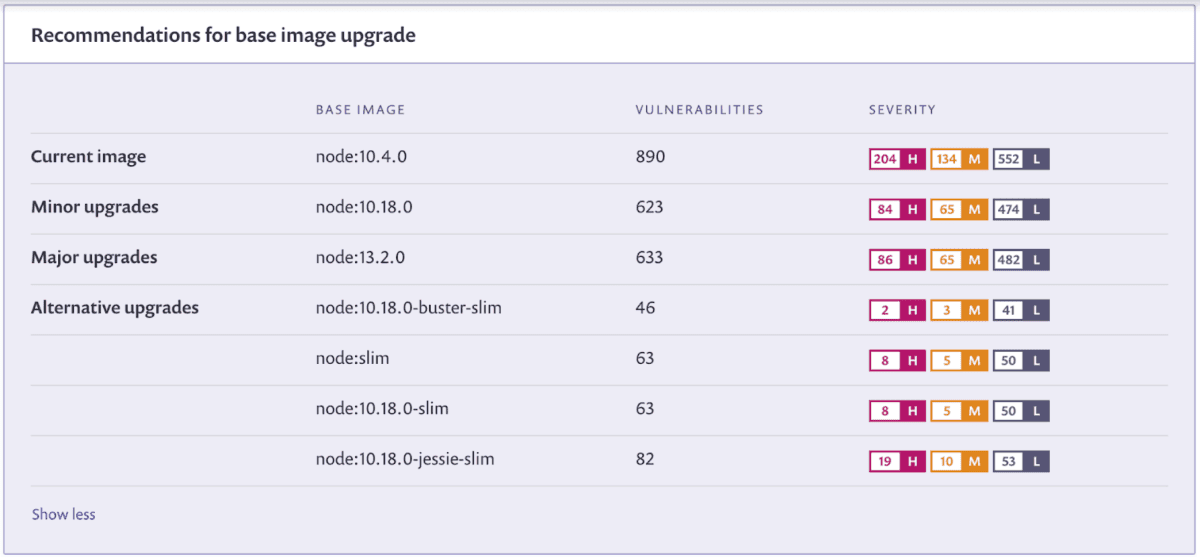
Snyk Container offers the different recommendations that are available based on your project, to enable you to control how you fix vulnerabilities:
Minor upgrades- with the general idea that smaller upgrades are faster and easier to use and less likely to break your build, these are minor upgrade recommendations, enabling you to keep the same major versions of the framework (node, in this example) and the same operating system distribution
Major upgrades - require a move to a newer major version of the framework or operating system distribution
Alternative upgrades - offer alternative suggestions for different images that can be used instead, but which may change both the framework and the distribution. While these alternative options may greatly reduce the number of vulnerabilities, as in the example above, they might also require more testing and consideration to ensure they don’t break your code.
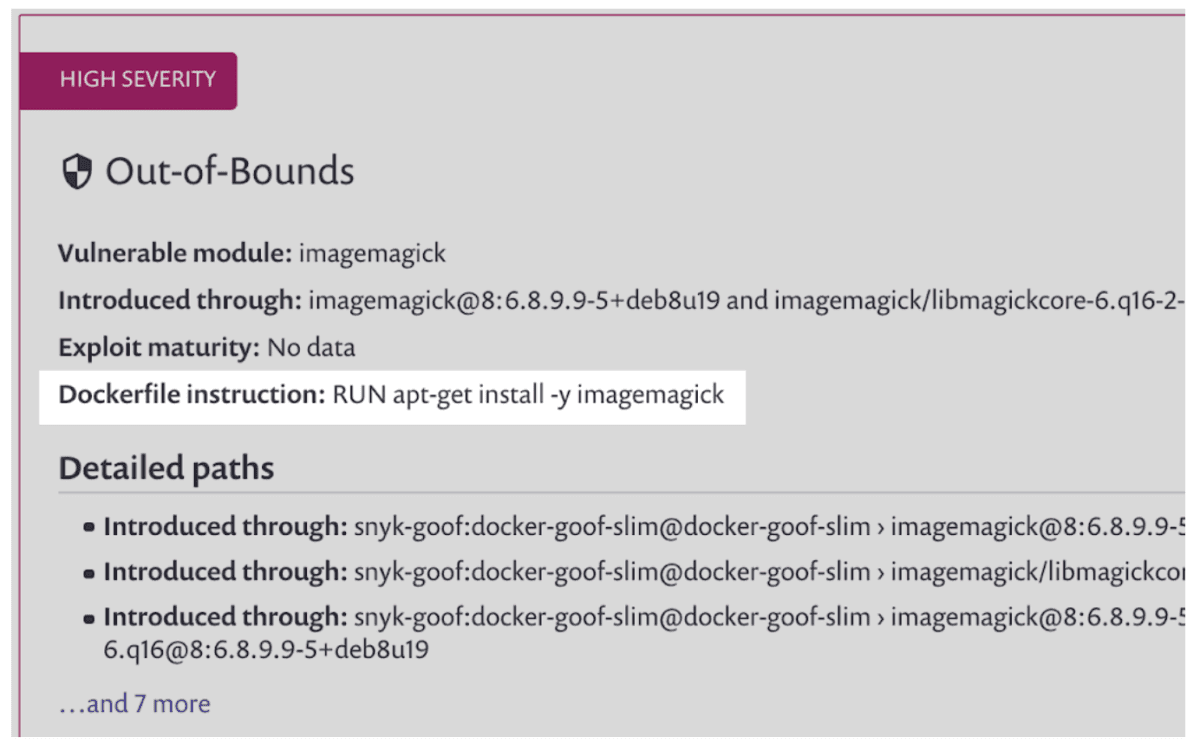
Identify problematic Dockerfile statements
Snyk Container also helps you discover where you might be introducing vulnerabilities in your containers by analyzing your Dockerfile instructions and pinpointing the specific paths through which vulnerabilities are introduced. Use this information to decide whether to install newer packages or even further optimize the container image, when possible, by removing instructions altogether.
In the image below, for example, you can see a vulnerability introduced in the Dockerfile by the instruction `RUN apt-get install -y imagemagick`. Armed with this information, you can determine if `imagemagick` is really something you need in this container; if you do need it, install a later version to fix the vulnerability.
Snyk Container & JFrog Artifactory: centralized code and container vulnerability scanning
Snyk’s integration with Artifactory enables you to find and fix vulnerabilities in both your open source dependencies and your container images all within the Artifactory repositories. Going beyond simply reporting on the number of vulnerabilities, Snyk Container speeds up your efforts to fix container vulnerabilities by providing recommended fix options and prioritized vulnerability details.
Getting started
JFrog Artifactory integration is available now for Snyk Pro and Enterprise plans and works with both on-prem and cloud-based Artifactory repositories. It’s easy to get started. Start scanning your container images by setting up the integration information in the Snyk application console and you’ll be ready to find and fix vulnerabilities in your container images.
Snyk will be a KubeCon EU March 30 - April 2 and a couple of Snyk-ers will be involved in KubeCon presentations:
Hayley Denbraver will be presenting a talk on Helm Chart security, Uncharted Territories:__Discovering Vulnerabilities in Public Helm Charts on April 1 at 10:55.
And Gareth Rushgrove will be part of the panel Kubernetes and Cloud Native Security: A State of the Union on April 1 at 14:55.
We hope to see you there! Stay secure!
Developer-first container security
Snyk finds and automatically fixes vulnerabilities in container images and Kubernetes workloads.
