Using the Snyk Vulnerability database to identify projects for The Big Fix
DeveloperSteve Coochin
16. Februar 2022
0 Min. LesezeitAs developers we all have our morning startup routine: make coffee, check slack/discord/email, read the latest news. One thing I do as part of my daily startup routine is check the Snyk Vulnerability Database for the latest open source vulnerabilities.
It's been especially interesting to see the types of exploits and vulnerabilities that appear in different ecosystems. For example, since May 2021 I’ve been watching the emergence of vulnerabilities in Tensorflow libraries. At the time of this writing, they have appeared again (nearly 2 pages of them!).
One other well-used ecosystem appearing multiple times recently is ElectronJS. It powers many well-used apps, such as Slack, VScode, and Twitch, just to name a few.
I'm going to show you a way to not only help find a project to fix, but also grab one of the special limited edition #thebigfix t-shirts, and help keep users safe from vulnerabilities. Everyone wins!
Getting Started with The Big Fix
The first step is to sign up for a free Snyk account, if you don't have one already. Head over to the getting started page and provide all the usual details (no credit card required). Then go to The Big Fix website and click Register now, fill out your name and email address, and you’re ready to start.
Once you're signed up, the next step is finding things to fix. There are a few ways to do this.
Connect an existing repository
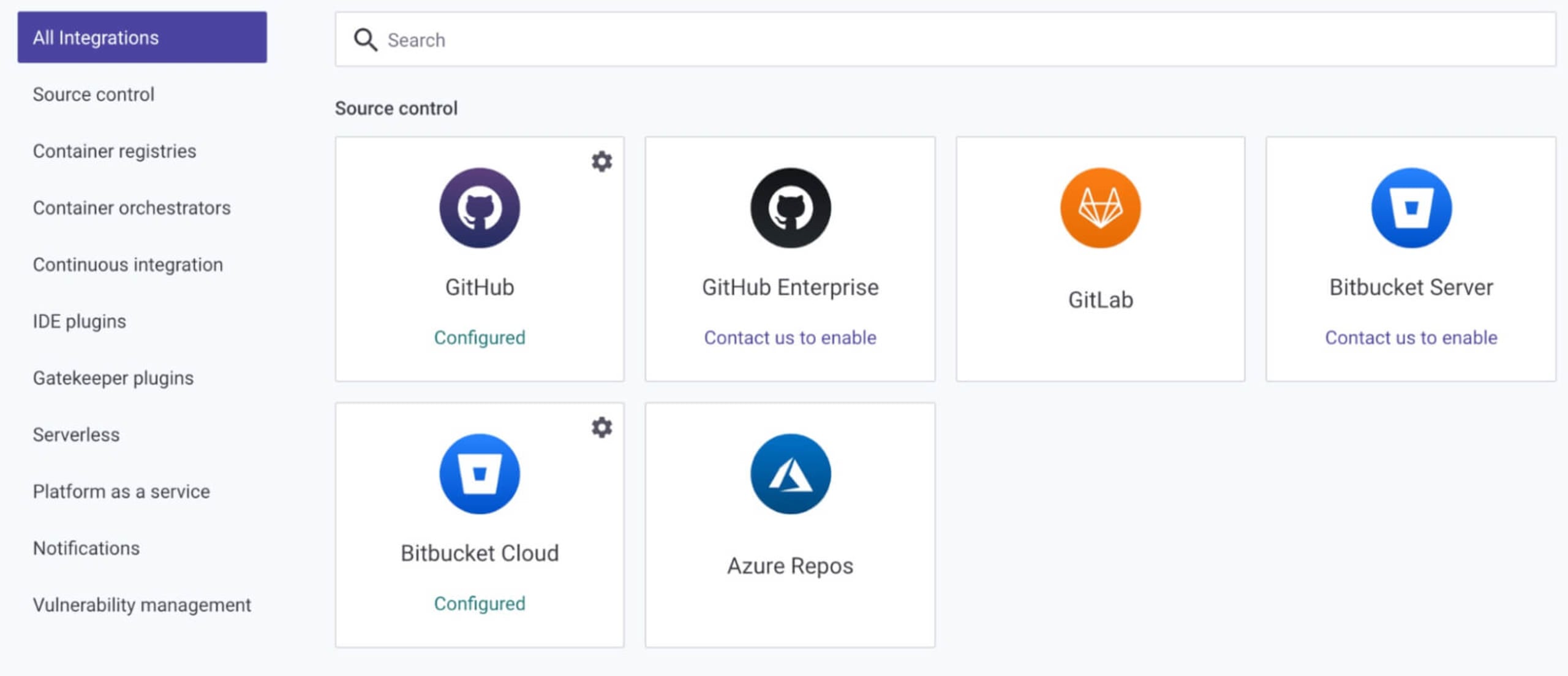
If you already have a project repository in mind, you can connect it quickly and easily. Go to your Snyk dashboard and click Add Project. If your repository of choice is not listed in the quick menu, click Other, which will take you to a comprehensive list of integration options.
Select your repository of choice and follow the steps to connect and configure.
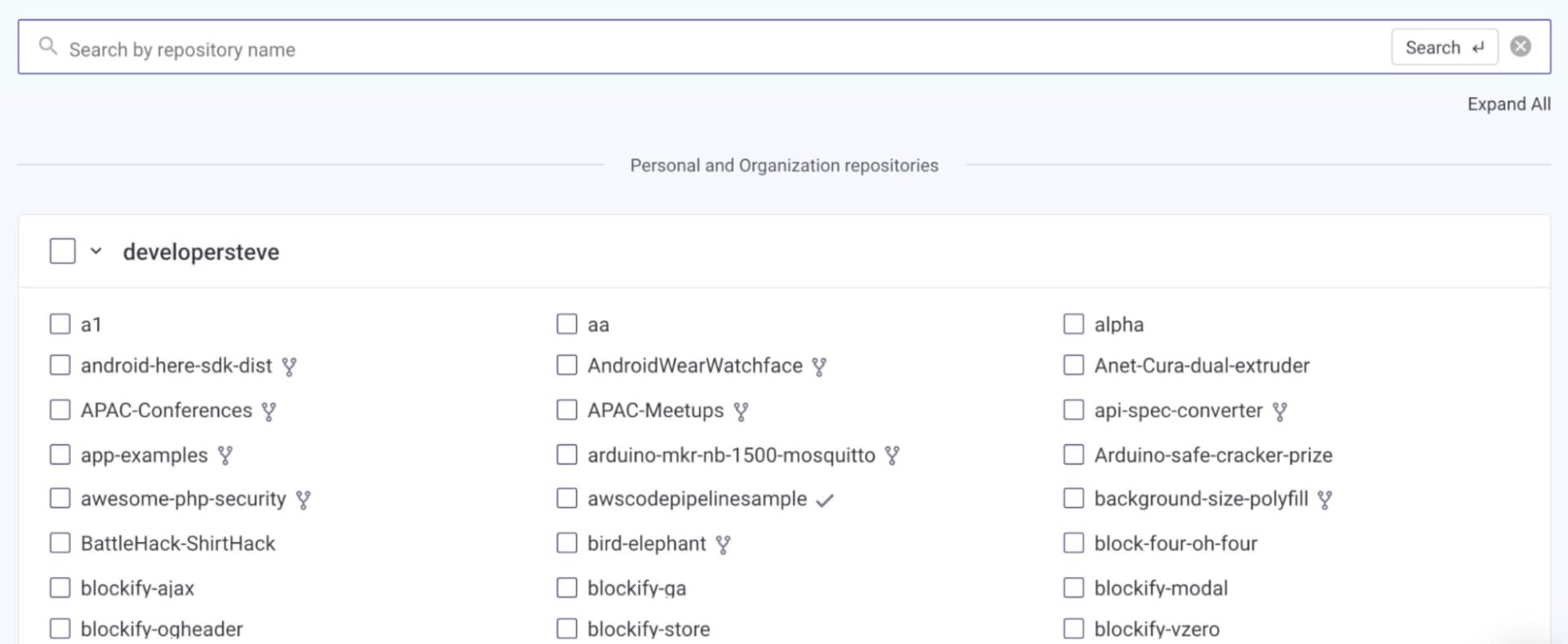
Once connected, click Add Project again and select the repository where you want to do an open source vulnerability scan. You can even scan private repositories.
When connected to Snyk Open Source, the scan will identify vulnerable packages in the connected package manifest. It will even identify fixes and potential remediation steps. Snyk Open Source also offers the ability to create an automatic pull request back on the repository with potential fixes — just remember to test the application to verify that everything in the project is working as expected.
Find a project where you can contribute
If you’re looking for a project where you can help fix a vulnerability, you can find one using the Snyk Vulnerability database and look through some of the packages or your ecosystem of choice.
A project I've recently contributed to as part of The Big Fix is one of my favorites from the PHP open source ecosystem: Invoice Ninja. This open source project helps businesses all over the world with invoicing and accounting, connecting into a variety of third party business tools.
First, I forked the main repository into my own account. Then, using the method above, I connected the repository to Snyk Open Source.
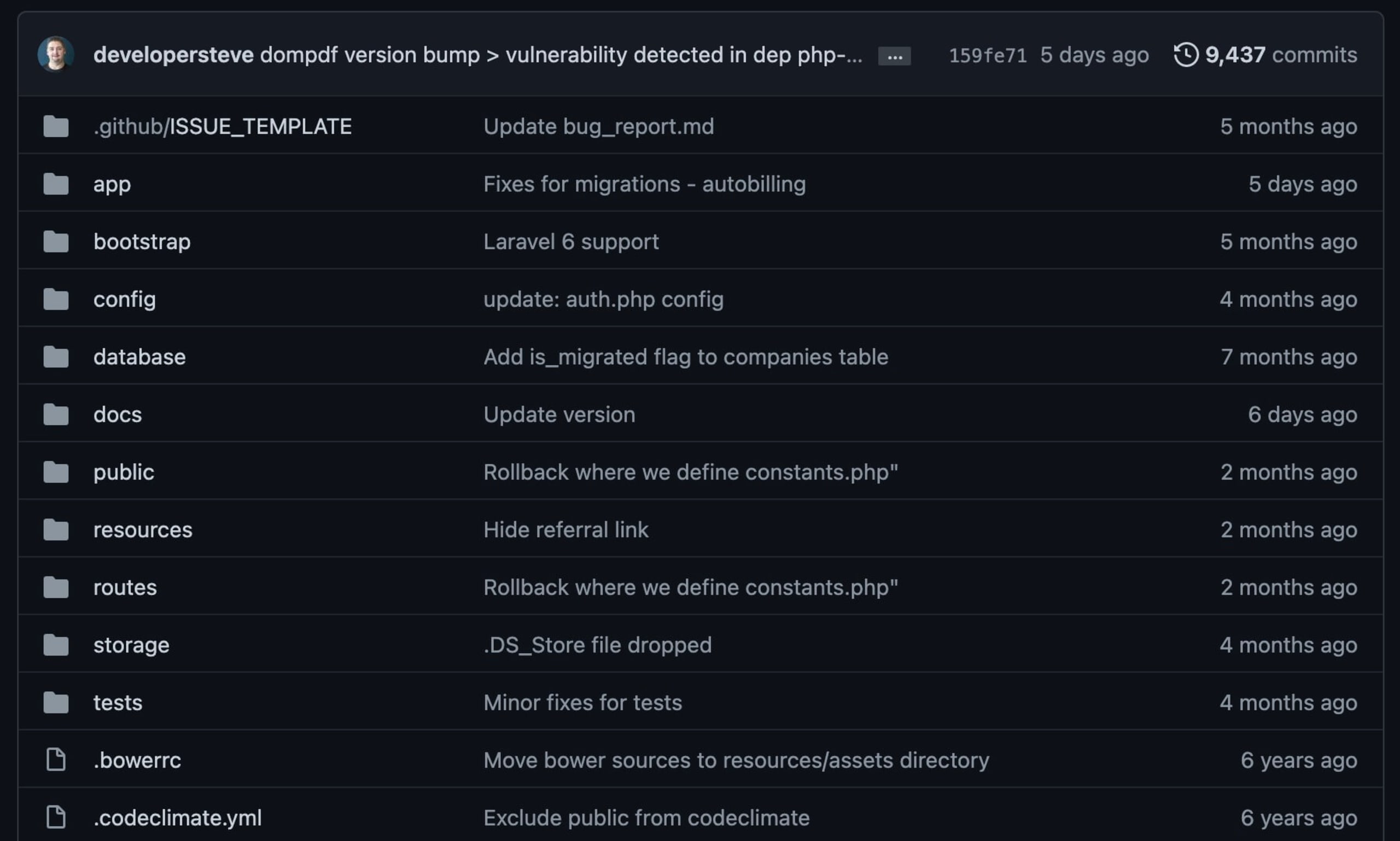
The scan identified a few vulnerabilities in the PHP composer package manifest, one of which was being introduced via DOMPDF 0.6.2 as a dependency library.
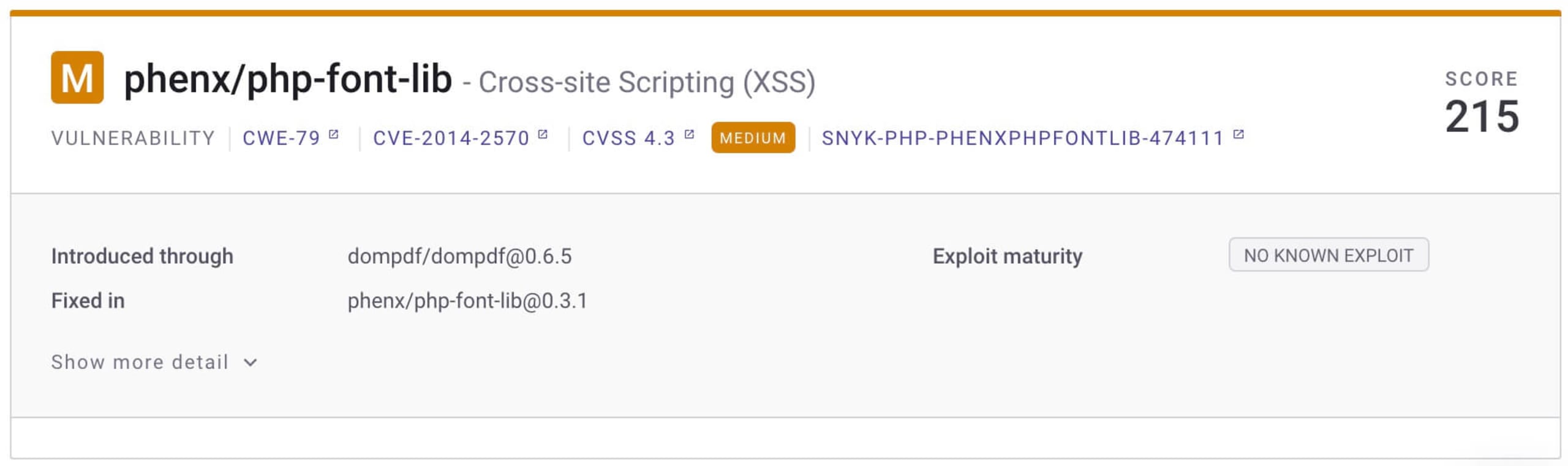
Digging a bit further into some of the findings, I identified a few issues, including a Cross-Site Scripting (XSS) vulnerable path in PHP-Font-Lib — a vulnerability from 2014. Tracing it back through the project helped identify not only the issue itself, but also the necessary fix.
When deploying fixes, you need to keep a few things in mind. Foremost is making sure the overall project still works. This is especially important with library and dependency upgrades. Many people rely on these projects for their day-to-day business, and deploying a breaking change is not something any project wants to see.
I pulled the forked repo into my localhost using a git pull request and launched VSCode, with the Snyk plugin installed. I was able to upgrade the affected packages and debug. Then I ran the code for testing in my localhost using a localhost server (this can also be done using PHP’s built-in server).
Finally committing back to my forked repository, I submitted a git pull request, which was checked and investigated back in the community before being merged.
The elation of completing contributions
I love giving back, especially when I can help keep another community safe and vulnerability-free. As open source community contributors, it’s always important to contribute and help protect all users of a project.
The added bonus: you get a free t-shirt, and your name goes into a drawing for prizes as part of The Big Fix.
Sign up for The Big Fix and get fixing today!
Be a part of The Big Fix
Join the thousands of developers that are currently securing their applications with Snyk.
