SnykCon 2021 recap #1: Snyk Learn, Snyk Apps, developer security, people hacking, security champions, and more
7 de outubro de 2021
0 minutos de leituraWow! What a great SnykCon so far! So many announcements, so many expert speakers, so many ways to make sure applications are developed securely. And how about the dance party from DJ Sam Aaron that he coded live for us on Sonic Pi? Amazing way to start the day!

If you attended today, thank you! We hope you enjoyed yourselves and found the content as helpful and actionable as we hoped you would. If you couldn’t attend, we’ll have the talks up on our SnykCon page after the event for you to watch at your convenience.
In this post, we’re bringing you a recap of all the exciting news announced during the event and a peek into the sessions that took place.
Snyk product updates
SnykCon is always a great place to learn about Snyk’s roadmap. For example, last year we announced Snyk Code, a product that is innovating the world of static application security testing. This year, we had a lot of product updates, and while I highly recommend you watch the keynote when it’s made available on-demand after SnykCon, but here’s a rundown:
Snyk Code: Support for C#, Ruby, PHP and Go added to Java, Javascript, and Python, enabling developers to find and fix security issues in their code.
Snyk Open Source: New language support for Elixir and package managers Yarn 2 and Poetry; Native integrations with Atlassian BitBucket and AWS CodePipeline; Integration of FossID’s C++ scanning support including unmanaged open source, binary detection and best in-class code snippet analysis.
Snyk Container: Expanded container registry support for Quay, Github Container Registry, GitLab, Google Artifact Registry, Harbor, and more. New support for Trivy open source container scanning tool with Snyk’s vulnerability database.
Snyk Infrastructure as Code: New support for detecting configuration issues in Kubernetes manifests in Terraform code with compatibility for AWS, Azure, or GCP.
Snyk API v3: Based on the latest version of OpenAPI, v3 of Snyk’s API is 3x faster, 20x more performant, with new issues, projects, and endpoints also available.
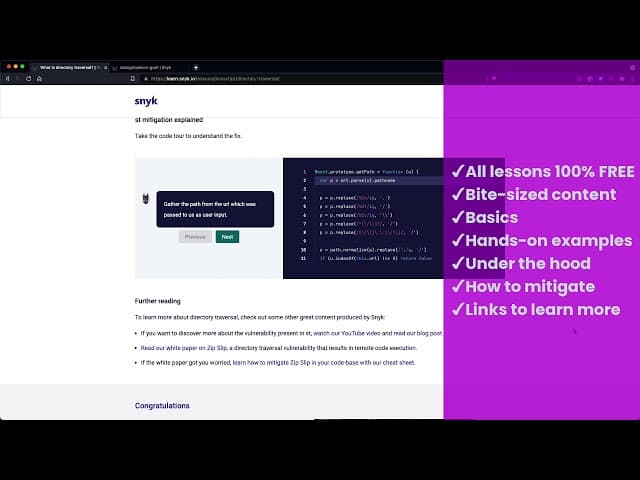
Snyk Learn: Empowering Developers with Security Education
A major announcement we had in the keynote was for Snyk Learn, our free developer security education product. Today’s developers require just-in-time learning experiences as they code and build applications. Snyk Learn is designed to help developers learn about and fix the vulnerabilities they find using Snyk, as well as offer bite-sized security lessons in the coding language or ecosystem of their choice. Snyk Learn puts developers fully in control of their own security education journey.
Snyk Learn includes:
Modular learning content for critical security topics such as SQL injection, directory traversal, prototype pollution and cross-site scripting, with more to come in Q4 2021.
Hands-on, step-by-step instructions and code-driven learning examples.
Detailed tips for preventing and mitigating attacks from happening.
Integration with the Snyk Developer Security Platform as well as Snyk Advisor.
Check out our Snyk Learn announcement blog to learn all about it, or check out this quick video:
Snyk Apps: Build your own custom apps
Another major announcement was Snyk Apps, our new extensibility points that enable you to expand the Snyk platform to easily integrate into your specific workflows. That’s right! You can now build you’re own apps to extend, expand, and automate Snyk’s functionality to fit into your customized environment and workflow. For example, you can create an app that streams Snyk’s security testing results into an incident management tool.
Snyk Apps turn integrations into first-class citizens of the Snyk platform and as such, have the following characteristics:
Snyk Apps are easy to build and use with a great UX for both authors and end users provisioning them.
Snyk Apps are based on the Snyk API. This means that integrations are inherently more stable and safer to use than before. A Snyk app will not, for example, break when a user accidentally deletes their personal API key!
Snyk Apps are more secure. Implementing OAuth 2.0, they have granular permissions that you define so they only get access to what they need.
Learn more by checking out our Snyk Apps announcement blog.
Snyk Impact: Social and environmental impact program
We also announced Snyk Impact, a social and environmental impact program designed to create a more secure, inclusive and sustainable software development and social impact sector. The program is aligned with environmental, social, and governance (ESG) approaches and fully embedded into Snyk’s strategy, operational effort, and governance structures.
To kick off this program, Snyk is contributing 100% of SnykCon sponsorship proceeds as well as matching up to $100,000 raised at SnykCon via the Snyk Community Impact Center to benefit Snyk’s initial cohort of tech nonprofit partners, all dedicated to furthering diversity in the tech industry, including: AIEDU, CareerVillage, DevelopforGood, FastForward, LearningEquality and UPchieve.
In the coming months, specific company commitments will be introduced in order to:
Increase diversity, equity, inclusion and belonging within the developer security community.
Further DevSecOps and broader digital capacity for the global social impact technology sector (nonprofits and certified B Corps in particular).
Following achieving CarbonNeutral certification in 2020, continue to weave sustainability practices into Snyk’s planning, decision-making, business practices and partnering across the entire enterprise.

Visit our Snyk Impact announcement blog to learn more about the good work Snyk is already doing in this realm as well as future plans.
Fetch the Flag CTF
This year we hosted our first ever Snyk-hosted CTF: Fetch the Flag. We weren’t sure how many teams would want to compete, and we were blown away when we capped out at 1,305 teams (nearly 2,700 participants).

Security researcher John Hammond worked with the Snyk Security team to create 24 challenges, including not-hot-dog, Disco Dancer, magician, spanning several categories — web, pwn, crypto, and more. After 10 hours of hands-on hacking, three teams emerged victorious. So let’s put our hands together for…
1st place: WreckTheLine
2nd place: Shisho
3rd place: idek

We had a lot of fun running this CTF, and we’re looking forward to running more in the future. But we’re biased, so let’s see what some of the participants had to say:
Stay tuned for John Hammond’s upcoming CTF writeup video to learn how to solve the challenges.
Customer awards
The SnykCon Customer Awards recognized customer champions who’ve embraced a modern approach to securing application development and the changing cloud native tech stack. They represent models of the industry’s shift and adoption of developer security. These incredibly inspiring customers include:
Innovator Award: Leaders who have championed a cutting-edge approach to security
Influencer Award: Leaders sharing invaluable lessons learned with the community
Pearson: Nick Vinson, DevSecOps Lead
Flo Health: Leo Cunningham, CISO
DevSecOps Award: Leaders whose profound approaches have bridged development, security & ops
Datto: Dave McCheyne, DevOps Engineer
Guild Education: Javier Perez, DevOps Engineering & Dejan Rajkovic, Engineer II, Devops
Security Champion Award: Leaders who fully embrace developer-first approach to security
CVS Health: Amanda Alvarez, Technical Security Product Owner
Keybank: Kathy Peters, Senior Information Security Consultant, Bob Olander, Senior IT Quality Analyst, Ron Matthews, Information Security Consultant, Nacole Beverly, IT Security Consultant, Eric Johnson, Application Security Consultant, Durasia Anderson, Cyber Security Analyst
Patch Award: Leaders who echo Snyk mission of building securely
10x: Gagan Bhatia, Head of Cybersecurity Delivery
Acuity Knowledge Partners: Sameer Goyal, Director, Head of Engineering
Social Impact Award: The leader who drives social or environmental impact
Classy: Chris Himes, CEO

Partner Day
This year, we kicked off SnykCon with Partner Day. During Partner Day, we enabled 100s of our channel and GSI partners around partnerships and integrations Snyk shares with with industry-leading technology vendors like Atlassian, AWS, Datadog, and Docker.
At SnykCon, we were excited to announce new partnerships with DigitalOcean and HashiCorp to further expand its developer security ecosystem. With DigitalOcean, we'll further enable developers to secure containerized applications during development so they can deploy them with confidence. And our integration with HashiCorp Terraform Cloud solves configuration security challenges that arise when delivering infrastructure as code, enabling developers to fix issues before deploying to production environments.
Snyk’s partnerships and native integrations ensure that our mutual customers can easily integrate our security tools into existing workflows and processes. This interoperability enables seamless adoption by our joint customers, and helps organizations build modern applications securely, without compromising agility or speed to bring products to market.
So many great developer security sessions
Let’s take a look at just a few of the great sessions we saw on the main stage and in breakout tracks.
The Human Element of Security: How to Be a People Hacker
Jenny Radcliffe, a Social Engineer and People Hacker, gave a great talk about the human element of security. When it comes to security systems, people are often the weakest link. In fact, Radcliffe revealed that 95% of security breaches are due to human error or manipulation. That’s why Radcliffe has made a career out of penetration testing in real life by breaking into physical premises to discover security flaws.
According to Radcliffe, social engineering is all about manipulating people to do what you want so that you can gain unauthorized access to resources for malicious intent. Through her lifetime of learning the “human element” of security, Radcliffe has learned how to read social cues, techniques for detecting lies, negotiation tactics, and more. And these same concepts apply to hackers and the developers trying to keep them out. “Whenever someone is building a wall, someone else is building a ladder,” said Radcliffe. “Remember that if you’re interacting with people, then people can be hacked.”

Shifting Security Left While Building a Cloud Native Bank
As a cloud architect at Lunar and CNCF Ambassador, Kasper Nisson has invaluable insights into staying agile and secure at the same time. In his talk, Nisson shared his experience with Lunar’s shift from a Fintech startup to a legitimate bank with its own banking license. Throughout the talk, he explained how security was fundamental to this transition process for Lunar.
According to Nisson, security starts with developer onboarding. With the right tools in place, Lunar enabled its developers to make the right security decisions themselves. For example, once Lunar adopted Snyk, developers were empowered to build secure software from the start. In fact, through configuration scanning and other security measures integrated into existing workflows, Lunar’s microservices are secure by default. “Our developers are responsible for vulnerabilities within their services and the dependencies they use,” explained Nissen. “We need to help them handle that responsibility, so we provide actionable advice, automation, and try to integrate with all the day-to-day monitoring tools.”
Your Personal Brand Speaks Louder than Your CV!
Farah Hawa, Application Security Engineer at Bugcrowd gave a great talk where she describes how technology professionals can build an online brand to open doors that their resume (CV) can’t on its own. While most recruitment processes focus on educational background and experience, the InfoSec community is full of people that have entered the industry through non-traditional routes.
Building an online brand is a way to give you exposure to relevant networking opportunities in the tech industry. Hawa practices what she preaches, and actively develops her own personal brand through informative YouTube videos about application security. “Building your brand and showcasing your skills on a wide platform allows you to bypass this process,” explained Hawa. “Your brand becomes a way to directly display your knowledge, passion, and skills to potential employers.”

Building Security Champions
Tanya Janca, CEO & Founder of We Hack Purple, covered ways to scale your security team by using a security champions program to supplement your AppSec team. According to Janca, the primary role of a security champion is to facilitate communication between security teams and developers, while also advocating for security within development teams.
Janca believes an effective security champions program requires six key ingredients: recruiting, engaging, teaching, recognizing, rewarding, and not stopping. “If we want developers to practice a secure SDLC, we need to support them in getting there,” said Janca. “And if we want security champions to sing the praises of security, we need to reinforce those values by coaching them so they can become our evangelists and our advocates.”
Enforcing Developer Intent with eBPF
eBPF is a technology that’s revolutionizing runtime policy enforcement. In her talk, Liz Rice, Chief Open Source Officer at Isovalent explored how eBPF can enforce developer intent as it relates to application security. Rice explained why runtime or network policy enforcement is critical for ensuring applications actually do what they’re supposed to do – or align with developer intent.
She explained how eBPF makes the kernel programmable so that developers can write custom programs and have them run in the kernel without having to write a kernel module. She then showed how modern tools built atop eBPF like Falco, Tracee in Rego, and Kubernetes Network Policies, help developers write custom policy checks using higher-level abstractions. “eBPF is enabling the creation of really powerful tools for unlocking networking, observability, and connectivity solutions across the world of cloud native,” summarized Rice.
Haunted: Chrome's Vision for Post-Spectre Web Development
Maud Nalpas, Developer Relations Engineer at Google, discussed Spectre, a vulnerability that enables malicious actors to break through isolation to access data from other websites or applications. Nalpas likens Spectre to a haunted house because the vulnerability is ubiquitous across most devices and likely won’t be going anywhere anytime soon.
While Spectre is a newer vulnerability, isolation issues like cross-site request forgery (CSRF), cross-site script inclusion (XSSI), and clickjacking have existed for a long time. That’s why Nalpas suggests some general security best practices for developers like isolating resources, isolating windows and frames, and following API changes and deprecations. “Web developers shouldn’t need to understand Spectre in detail in order to protect our applications,” stated Nalpas. “Luckily, there are some security features we can deploy in our web applications that can protect our users from both traditional isolation issues and Spectre.”

My npm package will eat your lunch
Zbyszek “Zb” Tenerowicz, Principal Engineer, Ecosystem Technical Lead at Egnyte, has installed a lot of packages using the node package manager (npm) during his time, including some that had contained vulnerabilities. Tenerowicz said that “not every npm package has to be nice.” It can be surprisingly simple for malicious actors to hide vulnerabilities not within direct dependencies, but much further down the dependency tree via a post-install script.
During his talk, Tenerowicz showed how supply chain attacks with npm work through simple demos. “You would have to go through all of your node modules and figure out which packages have post-install scripts, but don’t worry because there’s an app for that,” explained Tenerowicz. “You can run ‘can-i-ignore-scripts’ and it will compare the list of scripts that your dependencies have with a list of known scripts to offer hints.”
Workshops, product talks, and demos
The day also featured two hands-on workshops, five talks from the Snyk Product team, and 20+ bite-sized demos. The interactive workshops were Applying the Developer Approach to a Fully Automated Security Lifecycle (Oliver Crawford, Skyscanner) and Getting Started with Snyk (Waleed Arshad, Snyk), both of which really drove home the importance of putting security in the hands of developers.
In the Product track, we learned about:
The newly released Snyk API v3
How Snyk Code is breathing new life into SAST
How to automatically secure your container workflows
Securing your .NET ecosystem with Snyk
Staying secure from code to cloud
And all of the demos are going to be replayed tomorrow, so we’re not going to list them all out yet. But if your schedule won’t let you make it to SnykCon, don’t worry. All of these sessions will be shared on the SnykCon page after the event.
Join us for the last day of SnykCon 2021
As you can see, our expert speakers delivered enormous insights into the ever-changing application security space. Don’t forget to join us tomorrow for the final day of SnykCon 2021, where we will have another slew of inspiring talks about supply chain security, the future of cybersecurity, and much more.
And one last reminder that the sessions will be available on the SnykCon page after the event ends.
