Snyk IaC in 2021: Leading infrastructure as code security for developers
Lauren Place
22 décembre 2021
0 minutes de lectureWith great automation, comes great risk. The advent of infrastructure as code brought about automation for the tedium of deploying, provisioning, and managing resources in public clouds with declarative scripts. However, this automation increased the importance of creating secure IaC scripts or configurations with cloud infrastructure misconfigurations being cited as the biggest area of increased concern (58%) from 2020 to 2021 in the 2021 Snyk Cloud Native Application Security report. One IaC misconfiguration — such as an insecure AWS S3 bucket or an instance that is inadvertently publicly accessible — can introduce dozens of vulnerabilities throughout the enterprise.
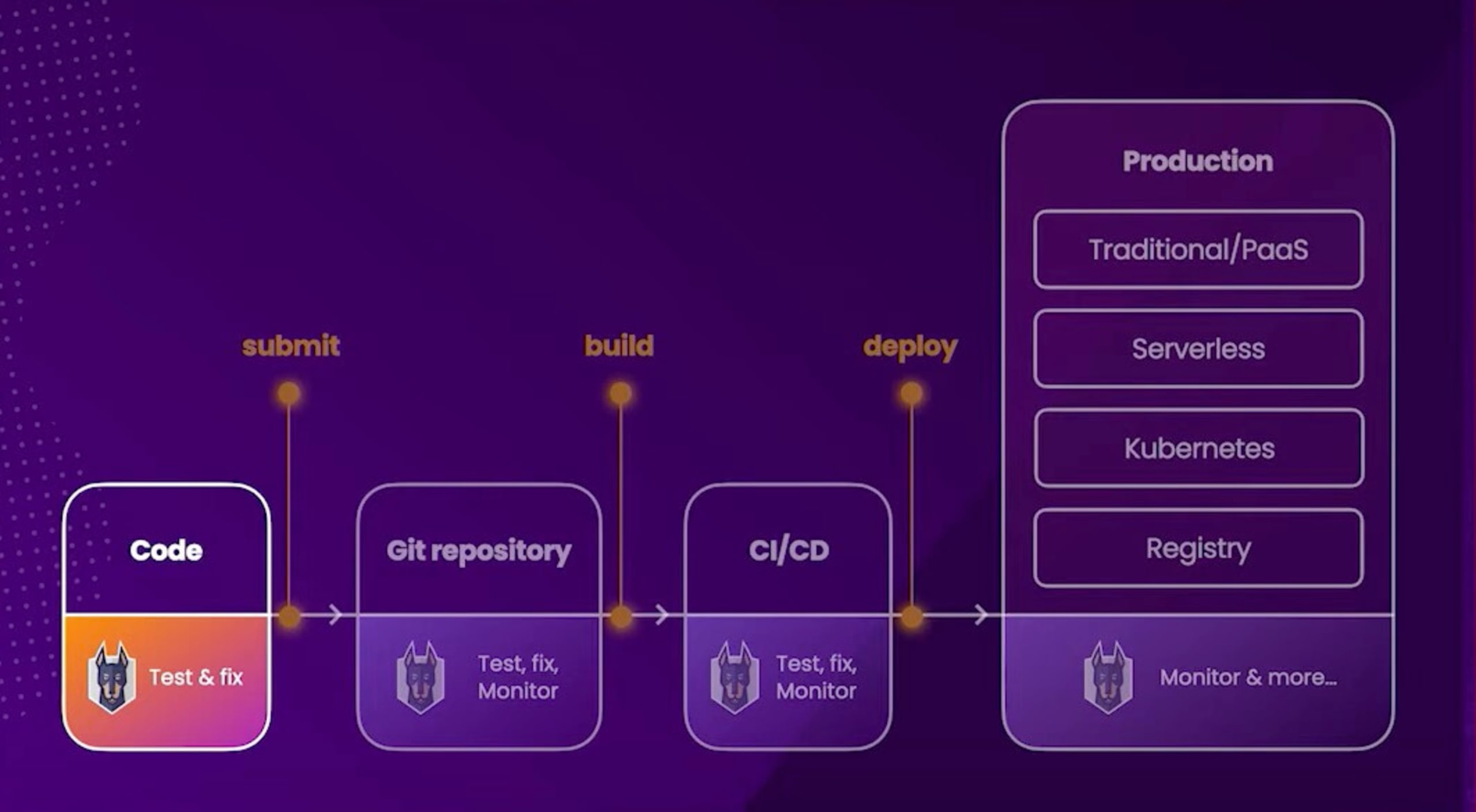
Snyk Infrastructure as Code (Snyk IaC) provides a developer-first solution helping DevOps teams secure their IaC configurations while in development and in CI/CD pipelines. Checking against hundreds of unique, predefined rules mapped to industry best practices, compliance framework, and cloud providers such as AWS, Azure, and GCP, Snyk IaC, embeds security into development teams and helps automate policy enforcement and fix misconfigurations fast.
In 2021, Snyk Infrastructure as Code:
Ran 235M tests from Git repositories alone
Detected over 8 million issues so far this year
Expanded Rule Coverage to a total of 413 unique misconfigurations* across AWS, Azure, GCP and Kubernetes
Improved scan speeds by 20x
Just days away from 2022, we’d like to reflect and recap on the progress Snyk Infrastructure as Code has achieved over the year on the path to becoming the leading developer-first IaC solution on the market.
Without further ado, let’s look at the three key areas where Snyk IaC delivered: more configurations formats and content, an enhanced developer experience, and integrations with developer workflows!
Supporting more infrastructure configuration formats and adding to our unique ruleset
To ensure development and security teams can scan all of their infrastructure, Snyk IaC supports a long and continuously expanding list of configuration formats including Terraform, CloudFormation, Kubernetes (including Helm), and Azure Resource Manager (ARM) templates and more are on the way.
In 2021, we added support for AWS CloudFormation and ARM templates for Azure environment teams to list, ensuring comprehensive coverage across all major cloud environments.
2021 was also a year for continuous improvement regarding our 400+ unique misconfigurations researched, threat-modeled, and mapped to compliance frameworks by our Snyk Security team.
In total we introduced…
66 new policies for AWS
66 new policies for Azure
41 new policies for GCP
133 policies supporting Cloudformation format
119 policies supporting Azure Resource Manager format
41 policies supporting Terraform Kubernetes provider format
Altogether improving the number of unique misconfiguration issues Snyk IaC finds for your organizations across all major Cloud providers as well as Terraform and Kubernetes formats and offloading the intensive process of researching and writing hundreds or thousands of rulesets and policies from security teams.
"We wanted comprehensive coverage to help us find issues that could result in infrastructure vulnerabilities in the runtime environment [without manual review]. Snyk was a great way for us to get visibility into all the different IaC repositories."


Charlotte Townsley
Director, Security Engineering, Natera
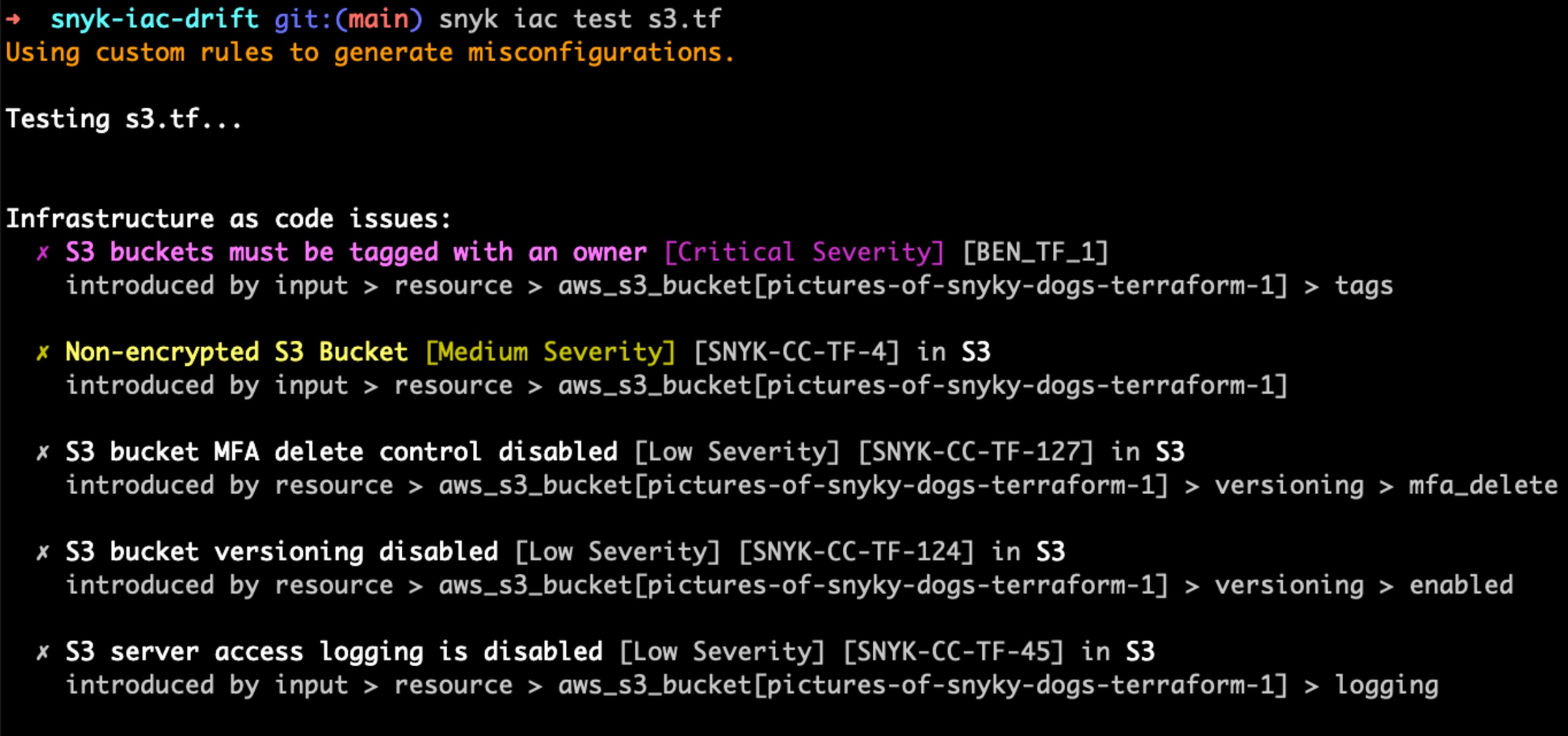
In addition to predefined, best practice rulesets, we recently launched Custom Rules for Snyk IaC to offer a new level of security specificity and flexibility. In case there is a specific scenario for your organization these best practice rulesets do not cover, you can now create a custom rule leveraging the Snyk Custom Rules SDK and Rego to write, test, bundle, and publish rulesets around use cases such as tagging standardization or establishing a pre-approved list of cloud resources.
Continuous improvement of the developer experience
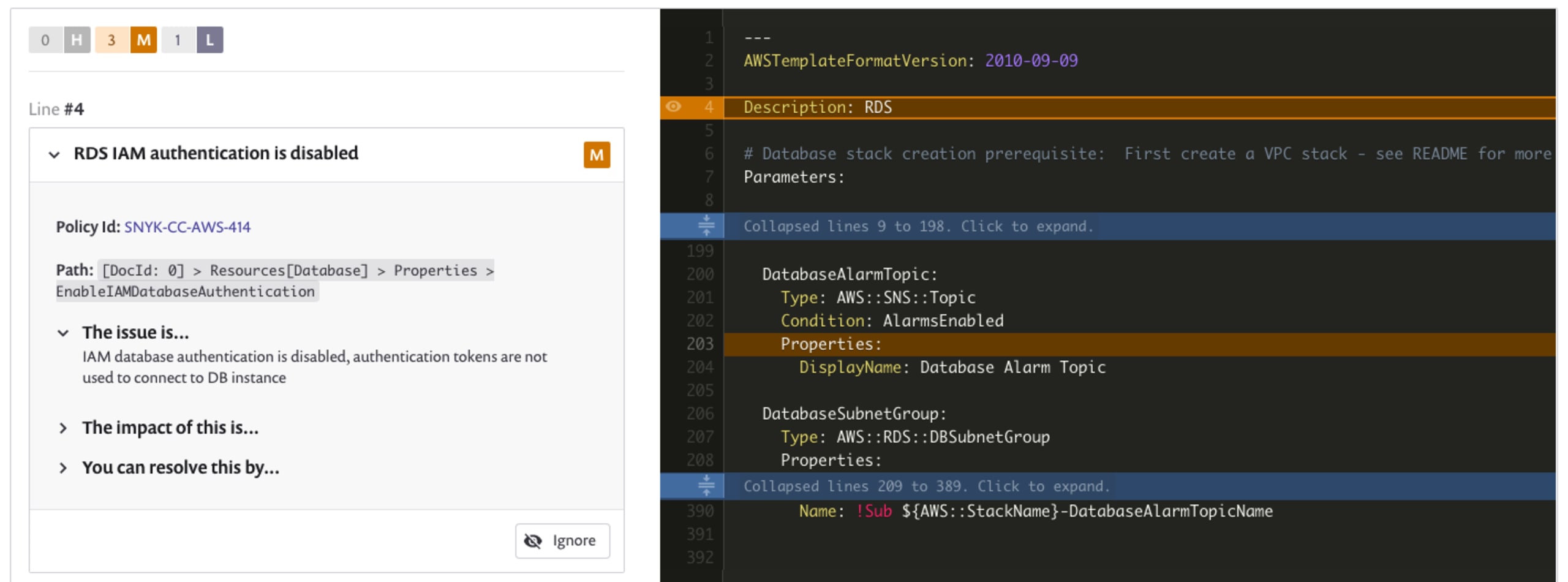
An IaC tool built for developers not only gives great visibility into your repositories, but it also meets developers where they work in their development environments, finds issues with speed and accuracy, and guides fixes in line with code. Snyk IaC sets the standard for developer-friendliness with actionable and automated fix workflows for misconfigurations.
Earlier this year, we announced the Snyk Plugin for JetBrains, automating IaC scanning directly in the integrated development environment (IDE). With this powerful new functionality, you can complete a scan and get actionable, developer-friendly fix advice within seconds. We are constantly iterating to improve the quality and experience of security intelligence for developers by fitting natively into developer workflows and adding improvements to our existing workflows.

Along these lines, we shipped scanning of your IaC in the Snyk CLI on your local machine or in your CI environment in 2021. Scanning via the CLI results in enhanced speed of IaC tests as well as an additional layer of security for your organization — as all test results are kept locally with no output sent back to Snyk. Here's an example of scanning a Kubernetes or Terraform file in the Snyk CLI:
In addition to this, we added the ability to ignore IaC vulnerabilities when running IaC tests so developers can effectively dismiss issues not relevant to them via ignore rules, automating the process of doing away with pesky notifications. Here's an example of ignoring the instance of the “publicly readable bucket” vulnerability in the Snyk CLI:
Integrating where it matters
And who can forget the partnerships and integrations we built along the way? Snyk IaC integrates early and across the development lifecycle from code development and Git repositories to CI/CD pipelines, but in 2021 we extended our integrations to the Terraform workspace.
Today, over 39% of our Snyk customers are using Hashicorp’s Terraform for provisioning and managing their infrastructure. In our mission to help embed security into DevOps processes and empower developers with expert security guidance, we announced our integration with Terraform Cloud now in beta. Combining Snyk & Terraform Cloud helps our customers streamline Terraform fixes before the “Apply” stage, by automating IaC scanning and checking against 400+ quality security rules and policies for AWS, Azure, GCP, and Kuberenetes into each and every Terraform Cloud “Run” as well as providing developers with frustration-free fixes and context they understand.
Last but not least, the team behind the leading open-source drift detection tool Driftctl joined us in October via our acquisition of CloudSkiff. It’s our commitment to keep Driftctl as it is— free to the community and open source—thereby we’ll be continually investing in the Driftctl technology and growing the community while coming up with creative new workflows and integrating drift detection and the ability to discover unmanaged infrastructure within Snyk IaC in months to come.
Updates are coming to Snyk IaC… in 2022
As migration to the cloud and adoption of IaC tools rises, so does the importance of IaC security. While infrastructure as code has made cloud provisioning a faster and more efficient process, it's also introduced a new way for misconfigurations to multiply and expose applications to attackers.
IaC security caught the world’s attention in 2021 when a misconfiguration error was found to be the means of entry in the October Twitch breach, with further analysis finding database credentials compromised in Terraform code.
Snyk Infrastructure as Code already stands apart with our coverage of Terraform, CloudFormation, Kubernetes, ARM templates, and other IaC formats. And we will continually invest in our security depth to find more and more unique misconfigurations in IaC across the development lifecycle — whether it be supplied by Snyk or custom policies contributed by your organization. In the year ahead, we have some exciting new additions planned including the integration of DriftCTL into our platform and the ability to detect changes in your managed (and unmanaged) resources!
We’re also more focused than ever on the developer experience, with more workflows based on your team’s requirements and preferences. This includes improvements coming for the Snyk CLI, a new plugin with Jetbrains IDEs to embed developer-friendly fixes directly into development environments, and the Snyk Terraform Cloud (now in Public Beta) integration to streamline security for Terraform Plan.
2022 will be an eventful year for Snyk Infrastructure as code, you can keep in touch with us on social (@snyksec) or join our DriftCtl community on Discord.
From all of us at Snyk, we hope you have a wonderful winter holiday and a happy (and secure) New Year!
Une infrastructure sécurisée à la source
Snyk automatise la sécurité et la conformité de l’IaC dans les workflows, et détecte les ressources manquantes ou ayant dérivé.
* Note that in Snyk IaC, we focus on quality or the number of misconfigurations captured by our ruleset, and not the number of rules themselves. Misconfigurations are what you want to find and fix — irrespective of their source, be it Terraform, ARM, CloudFormation, etc.