.NET developers alert: Moq NuGET package exfiltrates user emails from git
9 de agosto de 2023
0 minutos de leituraEditor's note: August 10, 2023
This blog post has been updated to reflect new information on this live situation. Stay tuned for further updates.
TL;DR
On August 8, 2023, the .NET community was informed that the testing library called Moq exfiltrates developer's emails from their development machine and sends them off to third-party remote servers.
Snyk has already published a security advisory and will alert developers who scan and monitor their .NET projects with Snyk.
Primeiros passos com Capture the Flag
Saiba como resolver desafios de Capture the Flag assistindo ao nosso workshop virtual de conceitos básicos sob demanda.
Updates as of August 10th, 2023:
The NuGet package Devlooped.SponsorLink was reported to the NuGet registry team.
Several Moq forks created, handle with care:
You’re encouraged to evaluate other packages from the same maintainer account.
About the Moq testing library for .NET
Moq is a testing library for .NET developers and describes itself as “the most popular and friendly mocking library for .NET”. It indeed earned community support, demonstrated by its outstanding 475 million downloads counts throughout time since its release and it’s 5.3k Stars count on GitHub.
What happened? Moq harvests developer emails
Beginning with version 4.20.0, Moq’s maintainer introduced a new build-time behavior that spawns a `git config` command to find and extract the developer’s git user profile’s configured email address.
Once the developer email is extracted, an HTTP HEAD request is sent to an Azure blob storage service with the email address hashed in the URL. This remote endpoint service interacts with a 3rd-party SponsorLink service, determining if the developer has installed its GitHub app.
While the aforementioned process aims to determine whether the developer is an active sponsor of the Moq project, PII data in the form of their email address is explicitly exfiltrated and shared with a third-party service endpoint.
This discovered incident is in fact part of an experiment to fund the maintainer’s work, carried out since January 2023 in other open source projects they maintain.
Moq’s supply chain security and package health concerns
Moq’s story is yet another case of a supply chain security concern due to open source libraries and their widespread impact due to the sheer growth of open source adoption within Enterprises and developer ecosystems.
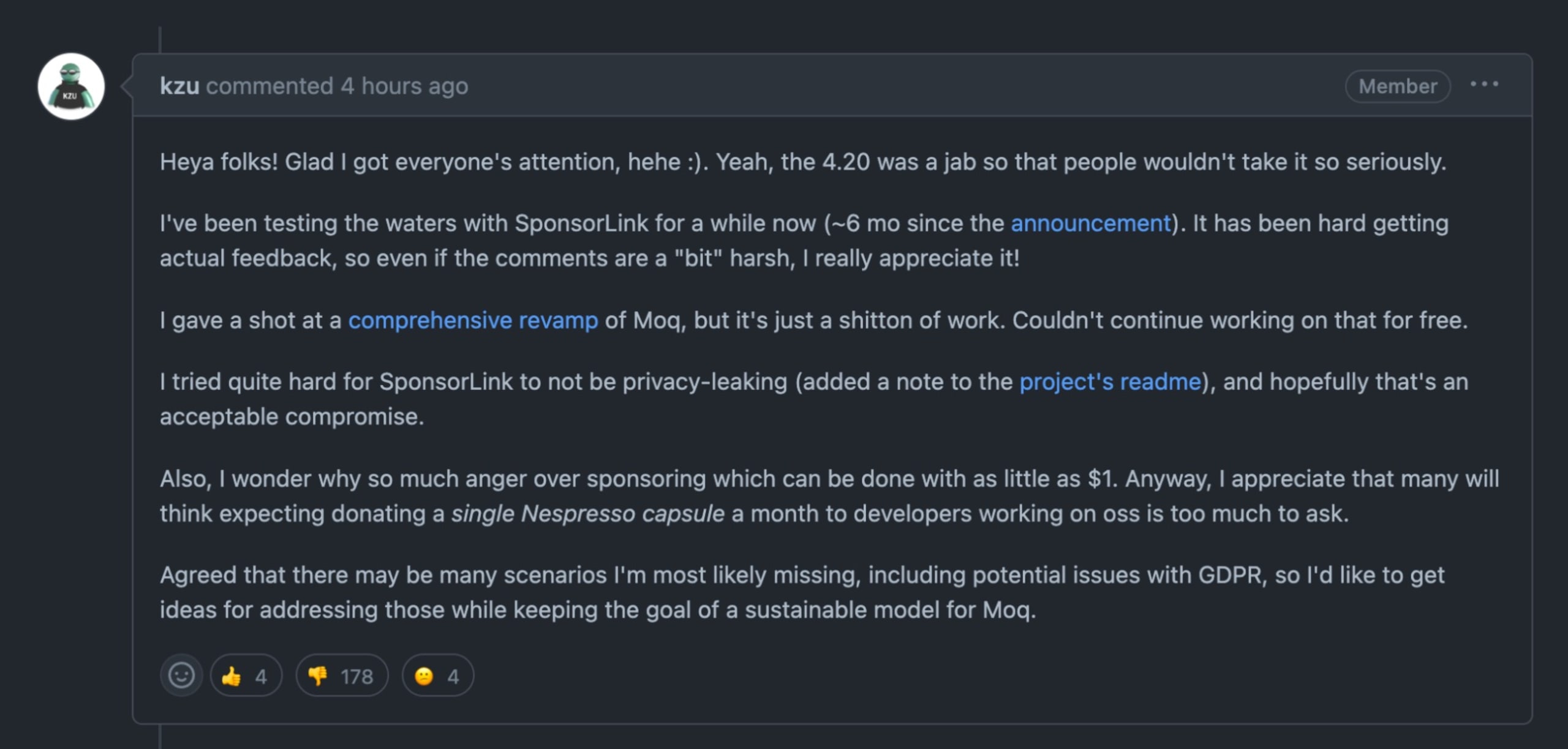
Unlike with security vulnerabilities, this NuGet package incident lends its story to the responsibility imbalance shouldered by open source software development maintainers in pursuing sponsorship, funding, and recognition for their work.
Moq, perhaps with good intentions, notified developers using the library with a “thank you for your support” message sent to their console. But without their consent, they had further harvested their email addresses, which is personally identifying information, and sent it to third-party service named SponsorLink.
The maintainer’s comment on GitHub says it all:
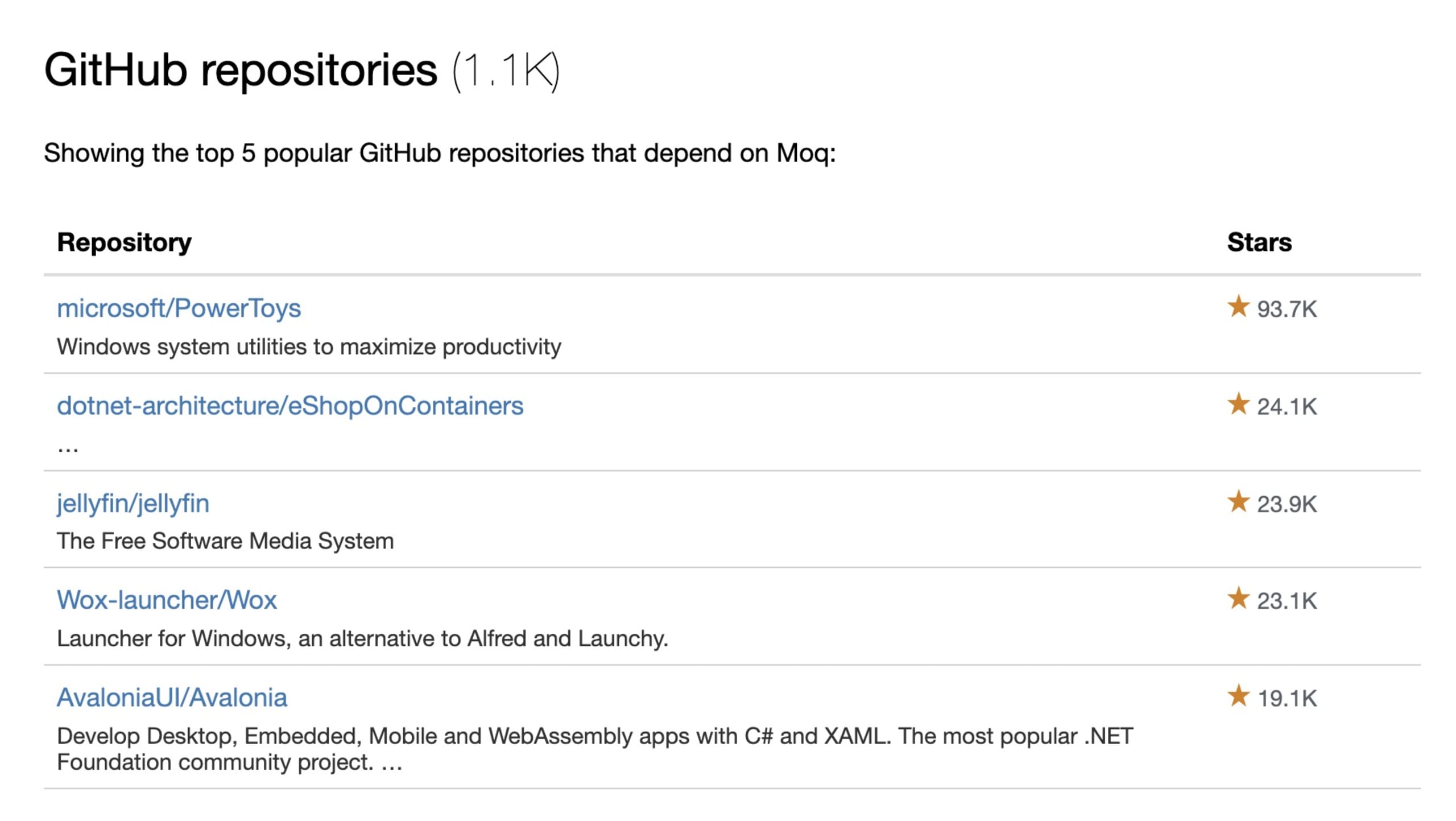
Moq’s scope of impact
Despite version 4.20.0 being removed from the NuGet registry, the historical download statistics help us visualize the blast radius of this version — which, while live for less than 24 hours, already accounted for 10,356 installs.
It’s worth noting that the maintainer acknowledged, in his January 2023 write-up, that the email addresses aren’t sent in plain-text and are instead hashed with the one-way algorithm SHA256.
Moq’s prior version, 4.18.4, free of the exfiltration behavior, accounts for 6,765,006 downloads in the past six weeks, demonstrating the potential blast radius of privacy breach if a developer hadn’t noticed the issue and raised it with the community.
Some of the projects that were impacted by this incident are Microsoft’s PowerToys developers, Jellyfin, and a thousand more project repositories that relied on Moq for its testing capabilities but were probably unaware.
Moq incident: What to do next?
Quick summary:
If you weren’t using version 4.20.0 of Moq, you avoided the PII exfiltration of user emails from the Moq library.
Version 4.20.0 was unpublished from the NuGet registry.
Pull Request #1375 was created and merged. However, the degree to which it reverted the user data exfiltration has not been determined.
Newer Moq versions were published, such as 4.20.2. However, we advise against installing them since it hasn’t been confirmed that no data exfiltration occurs.
What do next:
Remove the 4.20.0 dependency to avoid data exfiltration.
Block this dependency in your organization’s package management tools, such as Artifactory or Nexus, so other developers don’t accidentally install it.
Consider re-routing DNS records associated with SponsorLinks to avoid accidental data leaks.
Add Snyk to your CI or build workflows and Git repositories to detect Moq’s vulnerable 4.20.0 version and other security vulnerabilities, malicious libraries, and potential data leaks in software libraries.
Snyk is a developer-security tooling company and offers .NET developers tools to scan and detect issues in their .NET project dependencies, such as security vulnerabilities and undesired behavior issues, such as Moq’s incident. Get started here for your NuGet and Paket projects dependencies.
Snyk Code is a static analysis tool to help C# developers find insecure code in their code projects.