Fastify Node.js framework improves JSON security thanks to a security report
10 de março de 2020
0 minutos de leituraOn April 9th Francesco Soncina — also known as phra on the HackerOne security bug bounty platform — reported a Server-side JavaScript code injection vulnerability to the Node.js Security working group. This vulnerability, initially identified Fastify, a Node.js web application framework, as the affected target of this security issue.
Matteo Collina, one of the maintainers of the open source Fastify project, was invited to triage the report in a timely manner and review the proof-of-concept exploit code. The proof-of-concept attack employed a JavaScript code injection spawning a reverse shell that was embedded in the JSON schema read by the framework.
This security report was eventually deemed relatively harmless since it doesn’t affect Fastify by itself. This happened because the JSON schema is provided by the user as an application configuration item and thus is regarded as a trusted input.
Nonetheless, it is interesting, but also critical, to highlight the importance of such security reports, whether they end up as a verified CVE security bug or not.
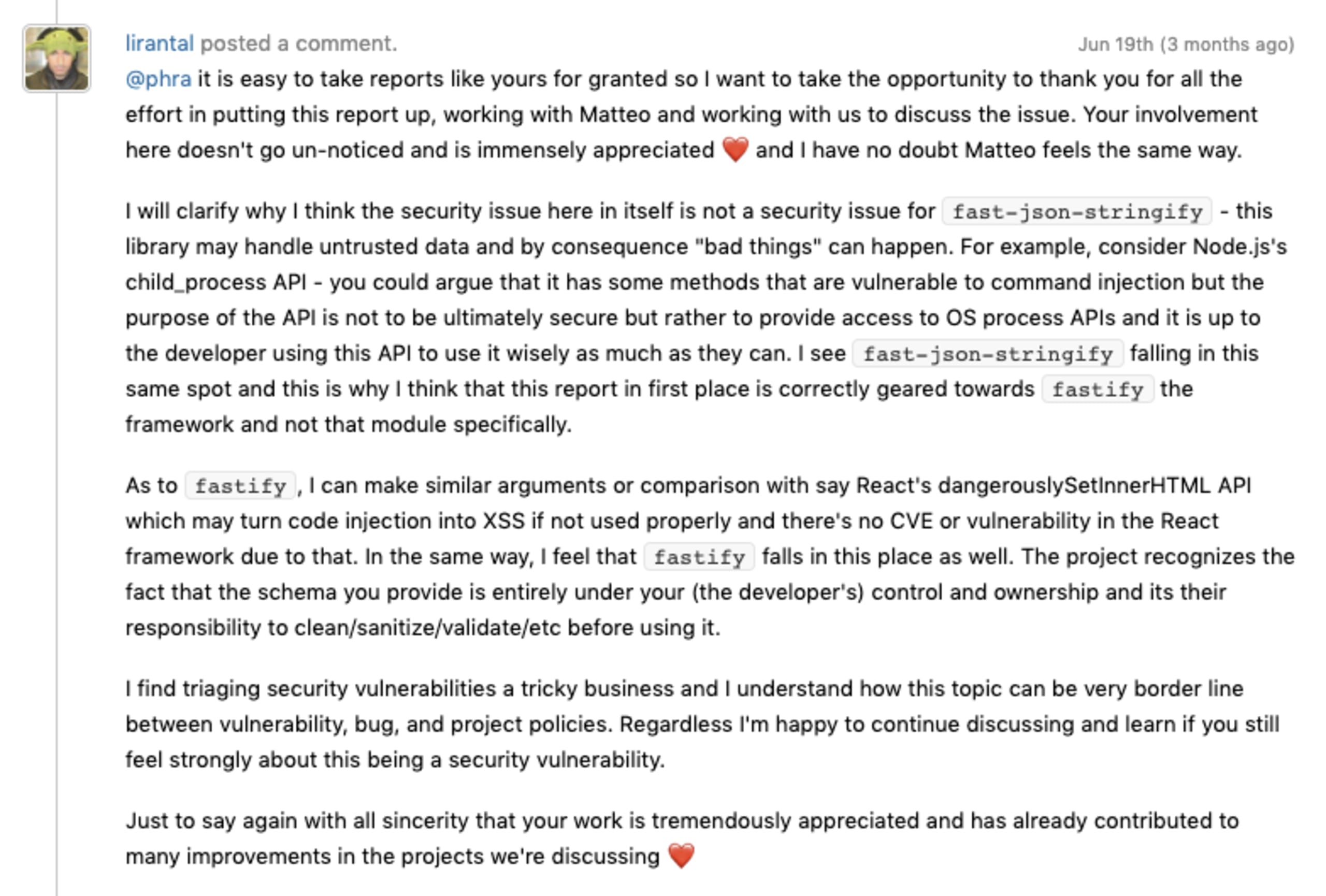
In this case, in particular, the security discussion throughout the report revolves around an ongoing debate between Fastify’s maintainer and the security researcher who disclosed it. The collaborative effort and determination from Collina and Soncina, is quite fascinating. Their effort focuses on flushing out all possible security sinks in the JSON rendering logic in order to make it as fault-tolerant as possible to security issues that may crawl up.
Most interestingly, this security vulnerability report led to:
A more robust and secure JSON parsing in
fast-json-stringifythat manifests through this pull request on GitHub and its follow-up official release in version 1.15.3.A security disclaimer in the documentation that clearly states the concerns and areas of risk so that users of the library will be well-informed on how to handle data. It was introduced through this pull request.
As I was wrapping up this report and preparing it for disclosure, it became clear to me that we should be doing more to recognize the value of security disclosures. Although the reported issue didn’t directly impact Fastify or fast-json-stringify,it sparked a meaningful discussion. Most importantly, it promoted awareness among maintainers of security concerns around their code.
Closing notes
If you’re a security researcher or a module maintainer, I’ll leave you off with this note from the original report. And once again, I want to thank you for all your work and effort to help us secure the Node.js, JavaScript and open source ecosystem.